Premium Only Content

Chapter-17, LEC-5 | Capturing Keylogss | #ethicalhacking #cybersport #cybersecurity #education
Capturing keylogs is a post-hacking session technique used by attackers to record keystrokes entered on a compromised system. Keylogging is an effective way to capture sensitive information such as usernames, passwords, credit card numbers, and other sensitive data.
When an attacker gains access to a system using a Meterpreter payload or other post-exploitation tool, they can use keylogging tools to capture keystrokes entered on the victim's keyboard. The attacker can then review the captured keystrokes to identify sensitive information or use automated tools to search for keywords or patterns that match specific data types.
Keylogging can be done using a variety of techniques, including hardware keyloggers, software-based keyloggers, and network-based keyloggers. Hardware keyloggers are small devices that are plugged into the victim's keyboard and capture keystrokes directly, while software-based keyloggers are programs that are installed on the victim's system and run in the background, recording keystrokes as they are entered. Network-based keyloggers capture keystrokes as they are transmitted over the network, allowing attackers to capture keystrokes entered on remote systems.
To prevent detection, attackers may use techniques such as obfuscation, encryption, or steganography to hide the captured keystrokes. They may also use various methods to exfiltrate the captured data, such as sending it directly to the attacker's system or storing it in a hidden location on the compromised system.
Capturing keylogs is a powerful post-hacking session technique that can provide attackers with valuable information about the victim's activities and credentials. However, it is also a high-risk technique that can be detected by security tools and is often illegal when done without permission on a system or network. As such, it should only be used by ethical hackers and penetration testers as part of legitimate security assessments.
-
 LIVE
LIVE
I_Came_With_Fire_Podcast
12 hours agoThe Normalization of Political Violence | Right Wing In-Fighting | China Chooses China
151 watching -
 LIVE
LIVE
PandaSub2000
7 hours agoLIVE 10:30pm ET | BUZZ TRIVIA with Chat!
122 watching -
 LIVE
LIVE
ThisIsDeLaCruz
1 hour agoWhat Fans Never Hear: Pearl Jam’s Audio Engineer Tells His Story
84 watching -
 1:39:58
1:39:58
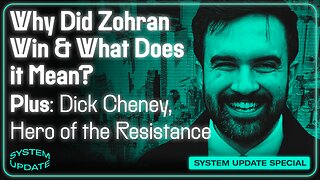
Glenn Greenwald
4 hours agoWhy Did Zohran Win & What Does it Mean? Plus: Dick Cheney, "Hero of the Resistance" | SYSTEM UPDATE #543
113K63 -
 LIVE
LIVE
This is the Ray Gaming
1 hour agoRAYmember RAYmember the 5th of November | Rumble Premium Creator
60 watching -
 1:44:39
1:44:39
vivafrei
4 hours agoArctic Frost is Bigger Scandal than you Think!! Live with Former Green Beret Ivan Raiklin!
48.6K42 -
 2:29:57
2:29:57
Turning Point USA
3 hours agoTPUSA Presents This Is the Turning Point Tour LIVE with Eric and Lara Trump at Auburn University!
46.5K11 -

XDDX_HiTower
2 hours agoBATTLEFIELD 6 REDSEC! [RGMT CONTENT Mgr.
5.33K1 -
 LIVE
LIVE
Joker Effect
1 hour agoSTREAMER NEWS: What actually occurred at Dreamhack ATL. Frontier Airlines. Kick Staff Trolled me?!
460 watching -
 LIVE
LIVE
VapinGamers
2 hours agoBF6 RedSpec - Nothing but Wins and New Rum Bot Testing - !rumbot !music
26 watching