Premium Only Content
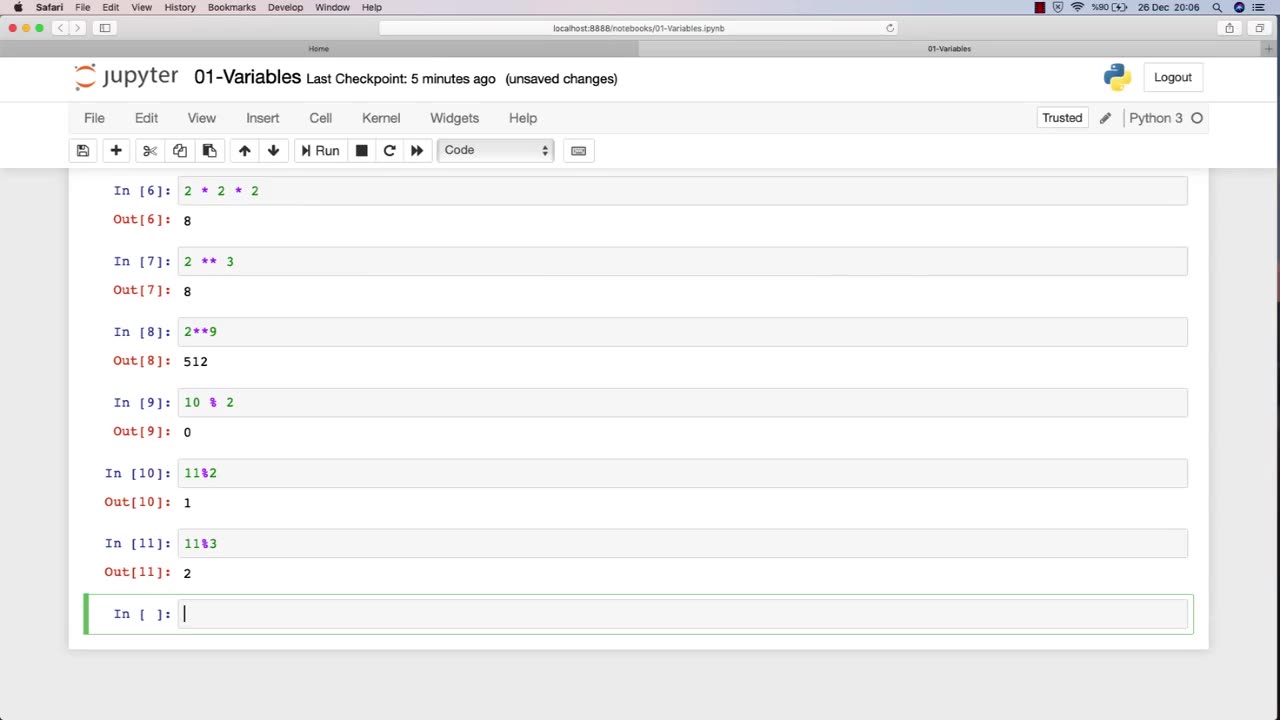
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
Dr Disrespect
7 hours ago🔴LIVE - DR DISRESPECT - BATTLEFIELD 6 - REDSEC - 10 WINS CHALLENGE
2,754 watching -
 LIVE
LIVE
Akademiks
2 hours agoAdin Ross x 6ix9ine x Akademiks stream
649 watching -
 LIVE
LIVE
StoneMountain64
4 hours agoBattlefield REDSEC HARDCORE, Ultra Movement, and CRAZY Portal Games
140 watching -
 1:09:44
1:09:44
Russell Brand
6 hours agoFrom Curb Your Enthusiasm to Courage — Cheryl Hines on Hollywood, RFK Jr. & Speaking Out - SF646
124K23 -
 1:30:26
1:30:26
The Quartering
5 hours agoWoke Is Back!
117K61 -
 1:18:21
1:18:21
DeVory Darkins
6 hours agoTrump issues CHILLING WARNING to GOP as SCOTUS hears arguments regarding Tariffs
119K105 -
 3:35:48
3:35:48
Barry Cunningham
7 hours agoBREAKING NEWS: PRESIDENT TRUMP SPEECH AT THE MIAMI BUSINESS FORUM! (MIKE JOHNSON PRESSER)
99K26 -
 2:04:47
2:04:47
The Charlie Kirk Show
6 hours agoOnward | Henderson, Laurie, Miles | 11.5.2025
106K26 -
 2:15:52
2:15:52
Steven Crowder
9 hours agoWho is the Real Myron Gaines | Ash Wednesday
367K479 -
 1:07:53
1:07:53
Sean Unpaved
5 hours agoRankings, Recaps, & Deadline Deals: CFB Shake-Ups & NFL Trades
60.6K3