Premium Only Content
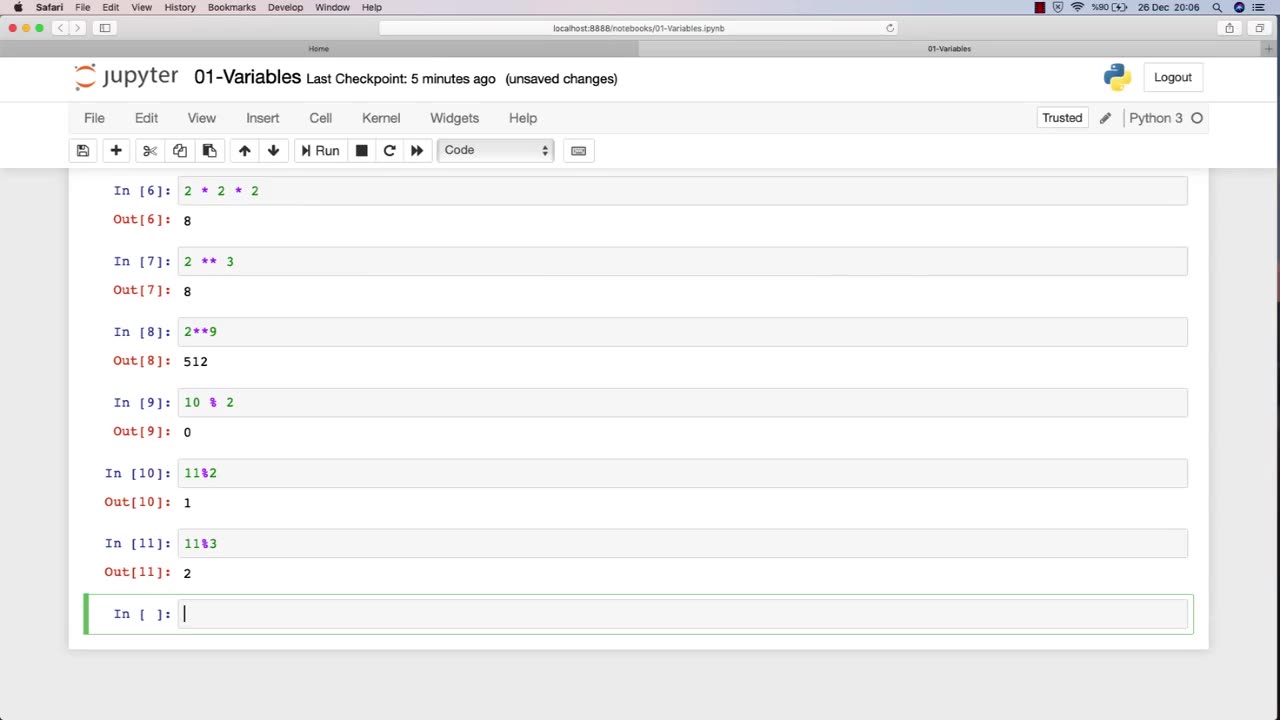
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 UPCOMING
UPCOMING
Rebel News
9 minutes agoConvoy punishments, Alberta vs BC Indigenous projects, Carney's body language | Buffalo Roundtable
-
 LIVE
LIVE
Steven Crowder
3 hours ago🔴Pillaging America: Lefty Celebs Prove Exactly Why Every Illegal Must Get Out
27,627 watching -
 LIVE
LIVE
Tim Young
1 hour agoShutdown Special LIVE w/ 19 members of Congress! Powered by @Kalshi
65 watching -
 1:05:29
1:05:29
The Rubin Report
2 hours agoFight Over Trump Lies Gets so Ugly It Could Be Eric Trump’s Final Appearance on This Show
20.4K19 -
 1:32:12
1:32:12
Nikko Ortiz
2 hours agoRealistic COP Simulator | Rumble LIVE
14.5K -
 LIVE
LIVE
LFA TV
13 hours agoLIVE & BREAKING NEWS! | WEDNESDAY 10/8/25
4,039 watching -
 LIVE
LIVE
The Mel K Show
1 hour agoMORNINGS WITH MEL K -Lobbyists and Greed have Replaced the Will of We the People 10-8-25
673 watching -
 LIVE
LIVE
The Shannon Joy Show
1 hour agoGold Surge Persists Signaling Recession, More Inflation & Potential War - Live W/ Peter Schiff!
218 watching -
 LIVE
LIVE
Grant Stinchfield
1 hour agoThe People Have Spoken: Trump Rising, Democrats Reeling
106 watching -
 LIVE
LIVE
Trumpet Daily
1 hour agoTrumpet Daily LIVE | Oct 8, 2025
156 watching
