Premium Only Content
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
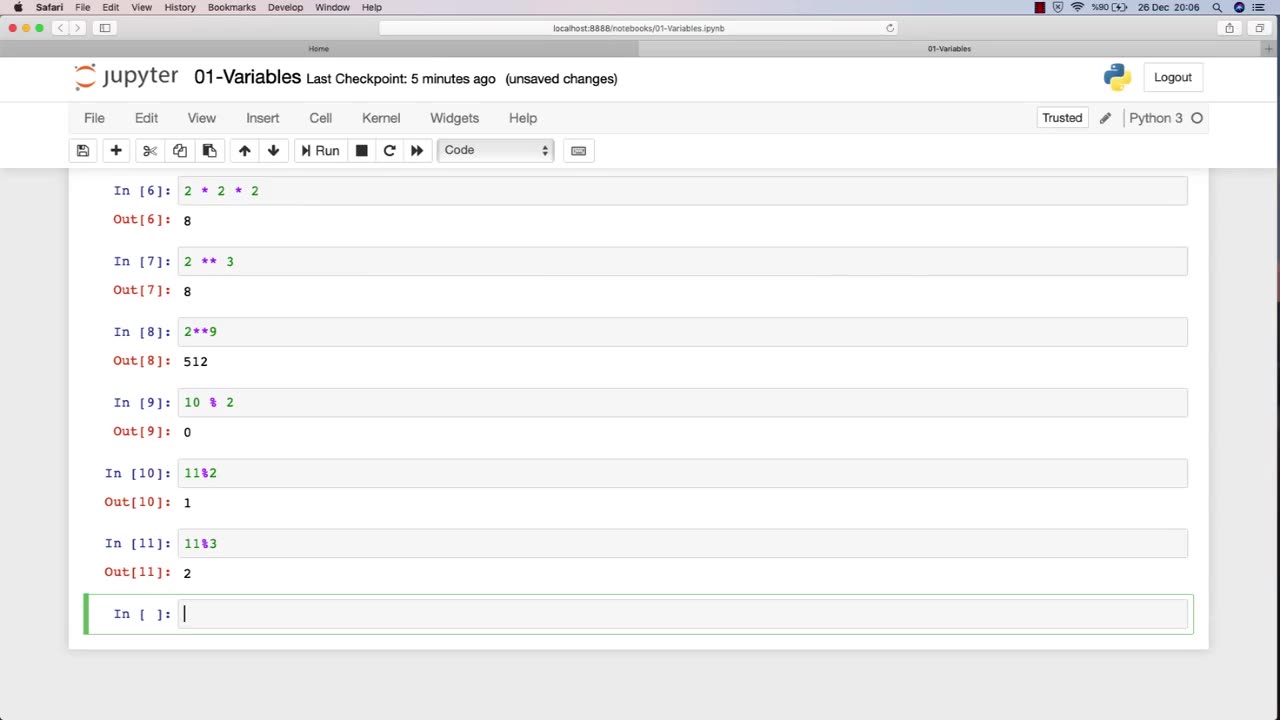
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 13:14
13:14
Upper Echelon Gamers
22 hours ago $2.09 earnedThe "Slop YouTubers" Are Angry... (And the Reason is Hilarious)
8.46K9 -
 1:06:28
1:06:28
A Cigar Hustlers Podcast Every Day
1 day agoHustler Every Week Day Episode 433 "Oscars And Chill"
13.7K -
 4:26
4:26
GreenMan Studio
1 day agoGREENMANS STOCKING STUFFERS 5 – GREENMAN AI
14.9K5 -
 5:00
5:00
SethDrums
4 days ago $8.42 earnedStaind – It's Been Awhile if it was 1980s
69.6K18 -
 20:18
20:18
itsSeanDaniel
2 days agoCandace Owens CALLED OUT by Piers Morgan, So She FIRES BACK
23.2K22 -
 4:57:14
4:57:14
Akademiks
13 hours ago21 Savage Wants Young Thug, Wham & Gunna to SQUASH IT! Future Sneak Dissing? Jim Jones Pays 50 Cent?
398K13 -
 6:01:38
6:01:38
Right Side Broadcasting Network
2 days agoLIVE: President Trump to Deliver Remarks in Rocky Mount, NC - 12/19/25
154K65 -
 3:24:48
3:24:48
VapinGamers
12 hours ago $50.36 earnedDestiny 2 - Dungeons and Loot with Friends - !rumbot !music
118K1 -
 2:07:44
2:07:44
TimcastIRL
13 hours agoTrump's Secret Plan To Make Charlie Kirk VP, America Fest IN CIVIL WAR | Timcast IRL
247K261 -
 4:09:13
4:09:13
I_Came_With_Fire_Podcast
22 hours agoLive Fire: Christmas Special
60.4K19