Premium Only Content
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
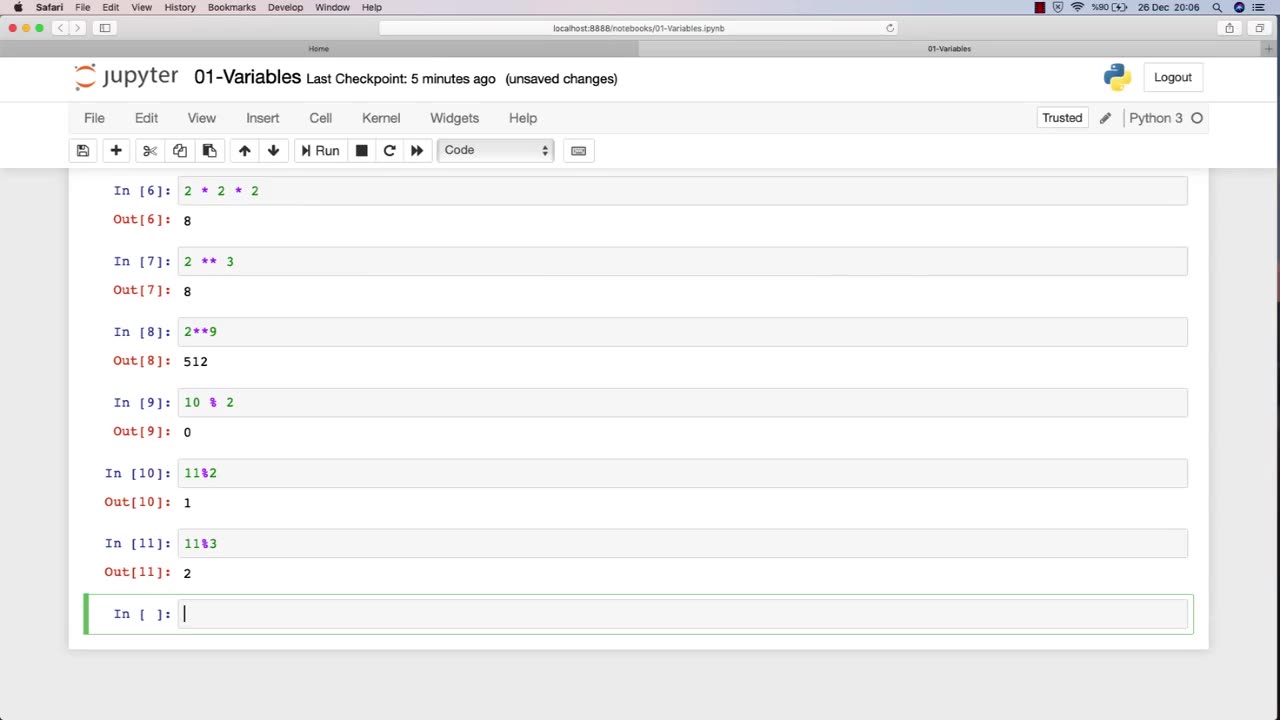
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
The Mel K Show
1 hour agoMORNINGS WITH MEL K - Constitution Incompatible with Globalist Goals 9-16-25
589 watching -
 LIVE
LIVE
Grant Stinchfield
1 hour agoRFK Jr. Speaks Out: The Pain of Assassination & the Loss of Charlie Kirk
71 watching -
 1:59:33
1:59:33
Benny Johnson
2 hours agoKash Patel Testifying LIVE Now on Charlie Kirk Assassination, Trump to Declare Antifa TERRORISTS?!
72.5K48 -
 2:07:38
2:07:38
Timcast
3 hours ago🚨LIVE: Kash Patel Testifies Over Charlie Kirk Assassination In Senate | Tim Pool
82.9K54 -
 LIVE
LIVE
Trumpet Daily
54 minutes agoTrumpet Daily LIVE | Sept. 16, 2025
497 watching -
 LIVE
LIVE
The Shannon Joy Show
1 hour agoTrojan Horse Trump Pushing ‘Worse Than Biden’ Speech Control Using Kirk Killing. Guest Brett Miller
231 watching -
 1:01:35
1:01:35
VINCE
3 hours agoThe Left's 'Malignant' Violence Problem | Episode 126 - 09/16/25
225K113 -
 LIVE
LIVE
LFA TV
6 hours agoLFA TV ALL DAY STREAM - TUESDAY 9/16/25
4,357 watching -
 1:45:59
1:45:59
Dear America
4 hours agoKiller ADMITS To Killing Charlie In DISCORD. Terror Cell EXPOSED! + JD Fills In on Charlie’s Show!
162K87 -
 2:59:28
2:59:28
Wendy Bell Radio
7 hours agoThe Left Lives In A Bubble
72K139