Premium Only Content
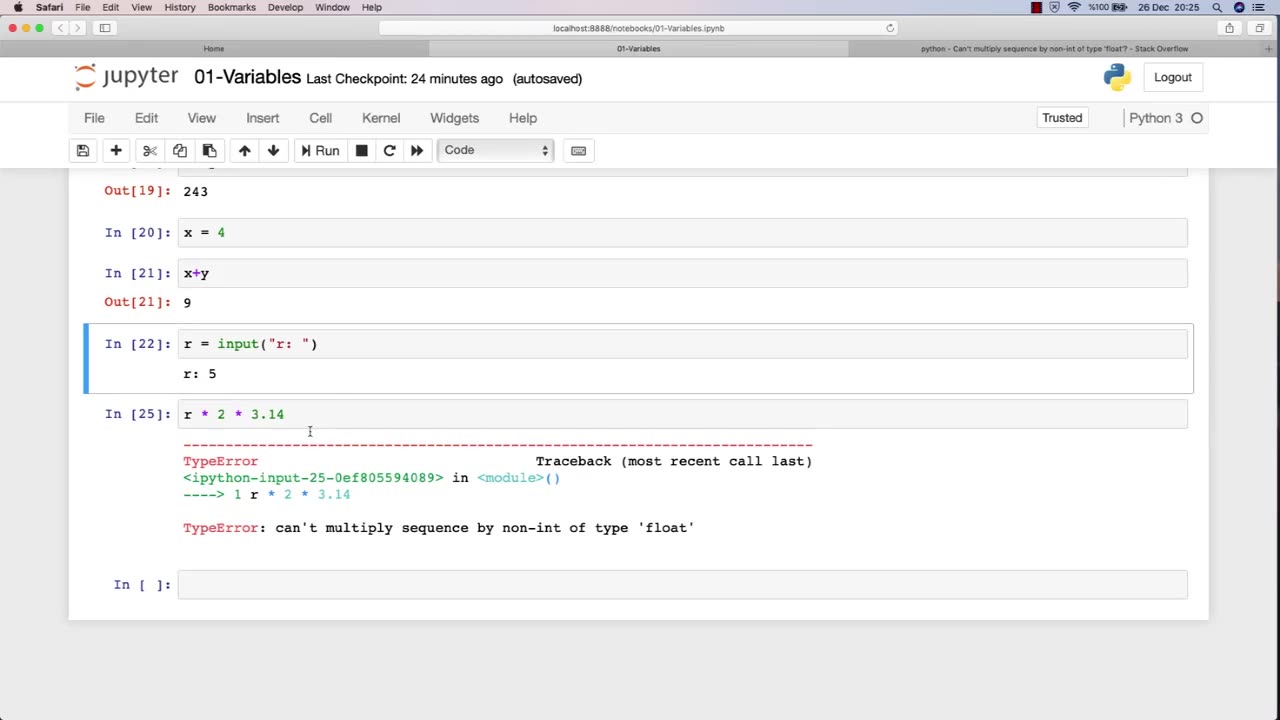
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
Wendy Bell Radio
6 hours agoLike Sheep To Slaughter
7,978 watching -
 DVR
DVR
DML
1 hour agoDML LIVE: NYC Goes Socialist: Mamdani’s Victory
18.9K6 -
 1:04:43
1:04:43
Chad Prather
14 hours agoTruth on Trial: When Fear Meets Faith
58.8K29 -
 LIVE
LIVE
LFA TV
13 hours agoLIVE & BREAKING NEWS! | WEDNESDAY 11/5/25
3,365 watching -
 1:57:16
1:57:16
The Chris Salcedo Show
13 hours ago $0.09 earnedDems Win In Dem States...And They Celebrate?
26.5K10 -
 1:04:43
1:04:43
Crypto Power Hour
11 hours ago $0.03 earnedPsychology Of Crypto Market Cycles
40.2K6 -
 9:58
9:58
Clintonjaws
12 days ago $0.17 earnedKaroline Leavitt's Response To 'The View' Host's Nasty Attacks Is Perfect
42.6K25 -
 24:23
24:23
World2Briggs
21 hours ago $0.03 earnedTop 10 Towns You Can Retire on $1900 a month in the Pacific North West.
33.2K9 -
 21:23
21:23
Lady Decade
17 hours ago $0.04 earnedThe Lost Sega Neptune Console Refuses To Die !
36.5K6 -
 17:14
17:14
ThinkStory
23 hours agoIT: WELCOME TO DERRY Episode 2 Breakdown, Theories, & Details You Missed!
29.3K