Premium Only Content
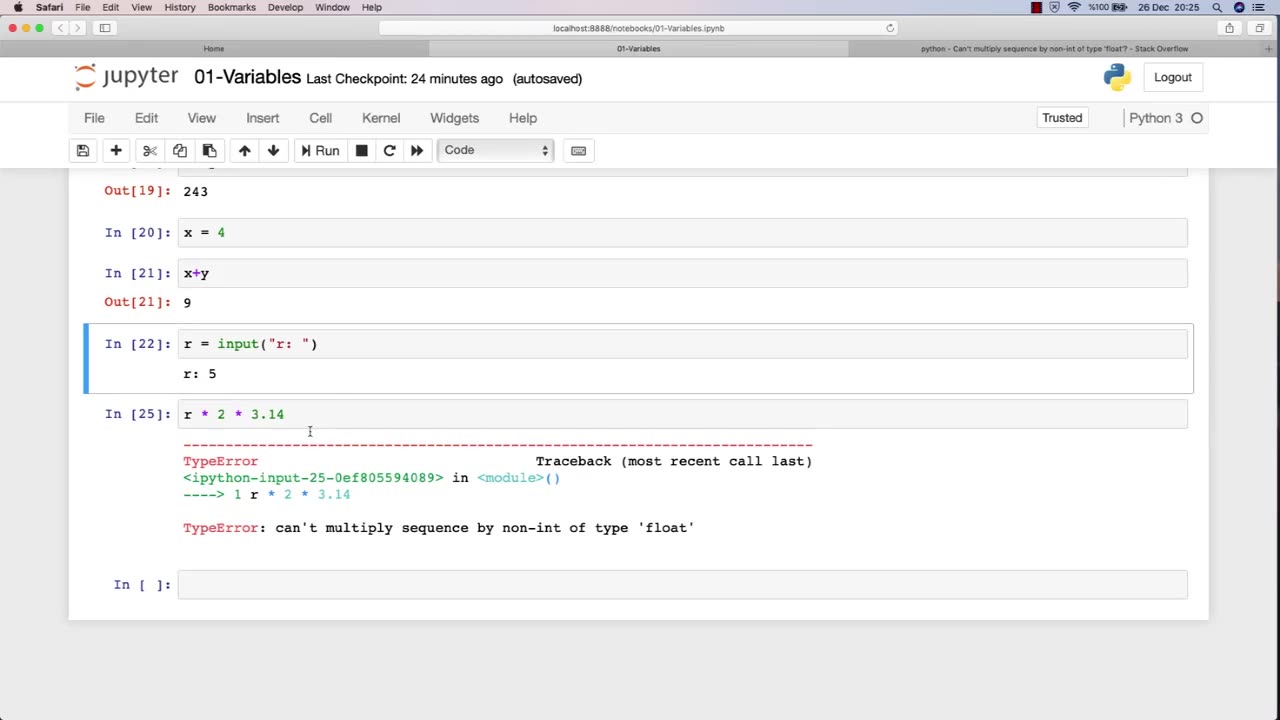
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-

Drew Hernandez
1 day agoNETANYAHU ATTEMPTS DEFLECTION FROM EPSTEIN FILES AS CONGRESS VIEWS UNREDACTED FILES
39.3K21 -
 16:53
16:53
Stephen Gardner
6 hours agoWhat Newsom Tried to Hide From Trump & Homan Will Shock You
60.6K55 -
 2:01:56
2:01:56
TheSaltyCracker
7 hours agoWoke Bowl is Dead ReeEStream 02-09-26
103K204 -
 54:08
54:08
Amy Dangerfield
5 hours ago $4.57 earnedIyah May: Israel, Faith & Demonic Music Industry
43.9K13 -
 21:23
21:23
Jasmin Laine
7 hours agoTrump Leaves Canada SPEECHLESS—Demands IMMEDIATE Tariff Negotiations After SECRET China Deal
37.3K28 -
 56:25
56:25
Flyover Conservatives
11 hours agoTwo Halftime Shows, Two Americas: The Propaganda Playbook Revealed; Historic 2-Week Silver Plunge — Setting up $300 - $500 by Summer? - Dr. Kirk Elliott | FOC Show
61.9K -
 1:54:12
1:54:12
Barry Cunningham
7 hours agoLIVE TONIGHT: Ghislaine Maxwell Deposition | Top SB Commercials | TPUSA Halftime Show Watch Party!
102K62 -
 8:49:05
8:49:05
Dr Disrespect
15 hours ago🔴LIVE - DR DISRESPECT - WARZONE - NEON HUNTER
159K13 -
 51:23
51:23
Donald Trump Jr.
11 hours agoRighting the Left’s Wrongs, Plus Explosive 2020 Revelations | Triggered Ep.315
226K91 -
 14:14
14:14
Robbi On The Record
2 months ago $19.88 earnedThe Identity Crisis No One Wants to Admit | Identity VS. Personality
135K29