Premium Only Content
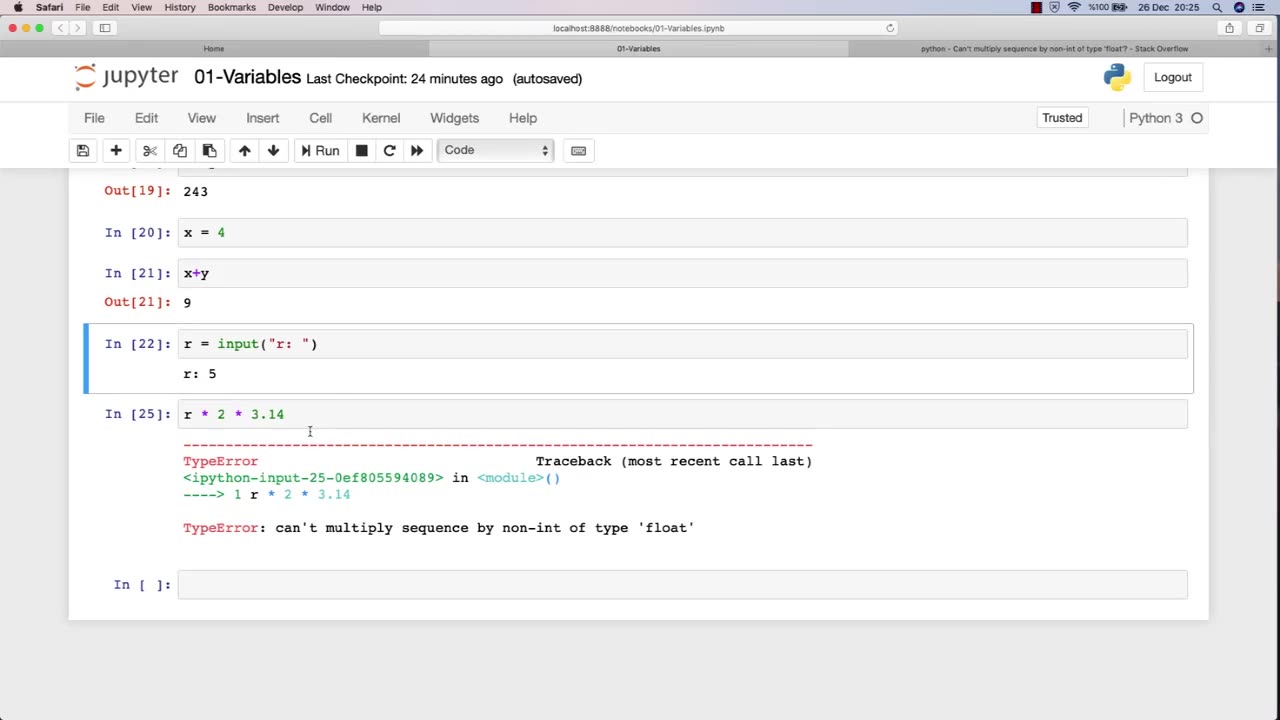
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 8:13
8:13
Danny Rayes
1 day agoMost Hated Teacher on Tiktok
5921 -
 15:31
15:31
Chris Harden
9 days agoWhat Happened to Kewanee, Illinois?
8193 -
 10:13
10:13
JohnXSantos
1 day agoThis AI Tool Makes Product Manufacturing 10X Smarter (FOR FREE)
7651 -
 16:28
16:28
Artur Stone Garage
12 days ago $0.15 earned$1000 AUDI A4 — WILL IT START After 10 Years?
1.22K -
 26:57
26:57
Advanced Level Diagnostics
18 days ago2021 Ram Promaster - No Crank! Key Stuck In Ignition! Diag & Fix!
1.03K -
 8:11
8:11
MattMorseTV
16 hours ago $17.65 earnedTrump's DECLARATION of WAR.
30.8K80 -
 3:44
3:44
GritsGG
15 hours agoUpdate Your Warzone Loadouts w/ These Tips!
12.7K1 -
 2:31:01
2:31:01
The Connect: With Johnny Mitchell
17 hours ago $15.16 earned"It's About To Get Worse"- CIA Agent Andrew Bustamante Explains Why It's Time To Leave America
21.3K29 -
 36:28
36:28
TruthStream with Joe and Scott
1 day agoMark Attwood joins TruthStream in Ireland by the lake to discuss all things from Crowley to Ireland to UFOs
14.2K32 -
 2:13:30
2:13:30
Side Scrollers Podcast
1 day agoUK Introduces MANDATORY Digital ID + Dallas ICE Shooting BLAMED on Gaming + More | Side Scrollers
200K62