Premium Only Content
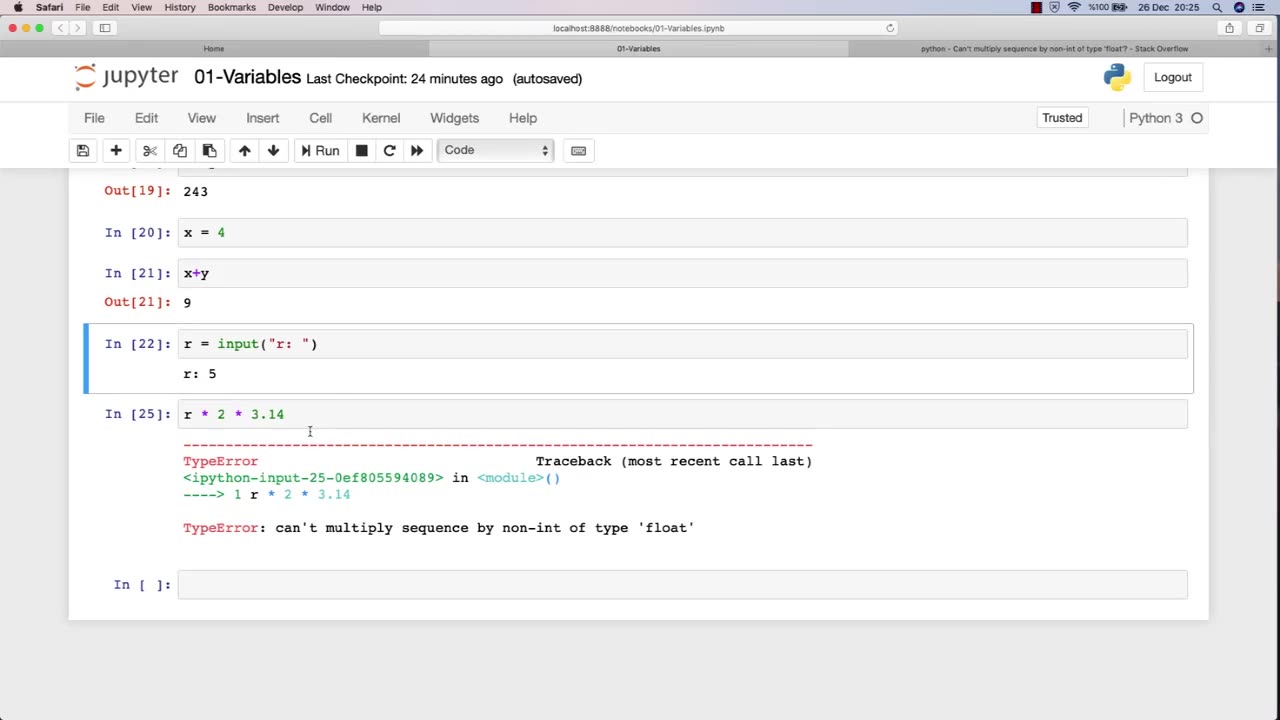
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 2:42:57
2:42:57
TimcastIRL
6 hours agoDOJ Releases Charlie Kirk Assassin Messages, Trans Left Aligned Confirmed | Timcast IRL
338K188 -
 1:09:13
1:09:13
Man in America
9 hours agoSICK: Xi & Putin Caught Plotting Organ Transplants for “Eternal Life”
70.1K24 -
 LIVE
LIVE
Drew Hernandez
11 hours agoMASS CONFUSION AROUND CHARLIE'S MURDER
1,360 watching -
 1:01:40
1:01:40
HotZone
6 days ago $9.76 earned"Prepare for WAR" - Confronting the URGENT Threat to America
71.2K17 -
 20:23
20:23
Scammer Payback
12 hours agoTerrifying Scammers with File Deletions
41.1K12 -
 16:22
16:22
The Gun Collective
8 hours agoWOW! 17 New Guns JUST GOT RELEASED!
52.2K10 -
 1:13:57
1:13:57
Glenn Greenwald
9 hours agoYoung Men and Online Radicalization: Dissecting Internet Subcultures with Lee Fang, Katherine Dee, and Evan Barker | SYSTEM UPDATE #516
184K76 -
 1:14:57
1:14:57
Sarah Westall
6 hours agoCEO of Crowds on Demand: The Fake World of Social Media, Protests & Movements w/ Adam Swart
65K9 -
 4:03:25
4:03:25
Geeks + Gamers
9 hours agoTuesday Night's Main Event
81.2K2 -
 40:36
40:36
RiftTV
8 hours agoHow We Got 400 Leftists FIRED for MOCKING Charlie Kirk | The Rift | Guest: Olivia Krolczyk
79.8K64