Premium Only Content
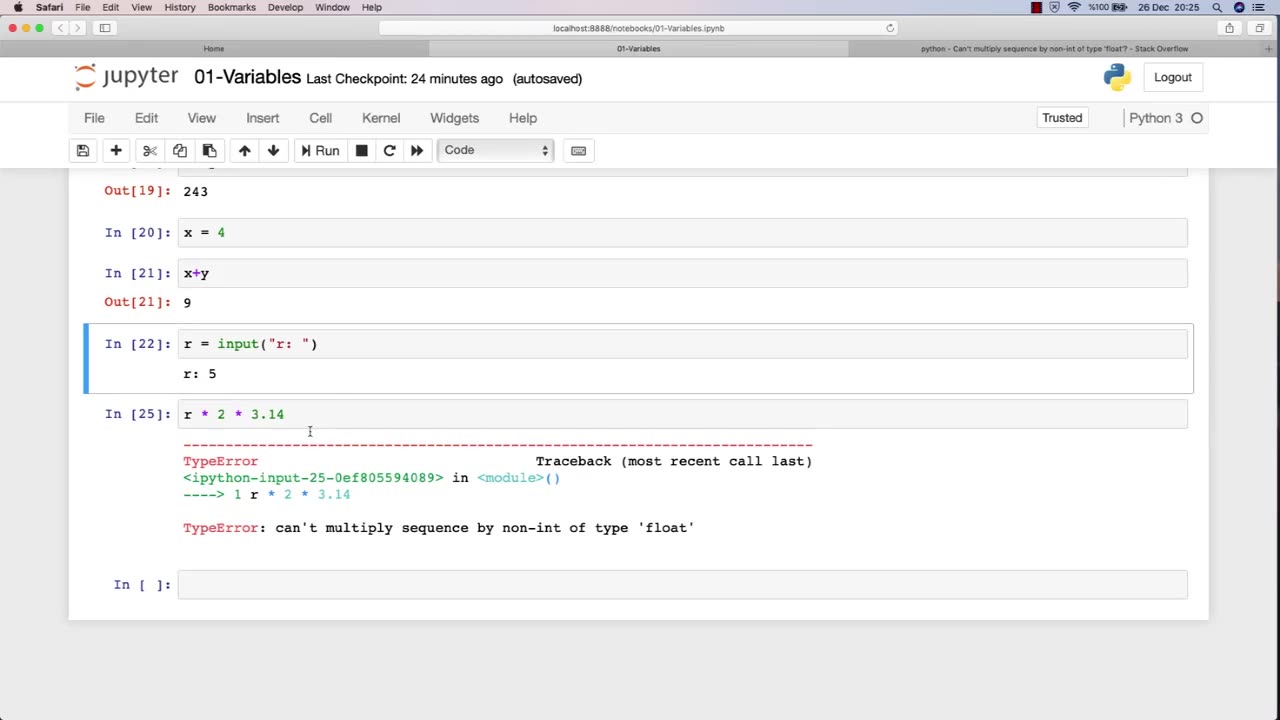
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
The Jimmy Dore Show
2 hours agoEmmy Winners DEMAND Israel Stop the Genocide! Charlie Kirk’s LAST INTERVIEW Before His Death!
5,681 watching -
 LIVE
LIVE
LFA TV
22 hours agoLFA TV ALL DAY STREAM - MONDAY 9/15/25
928 watching -
 54:12
54:12
Donald Trump Jr.
2 hours agoCharlie's Vision. Our Future. | TRIGGERED Ep274
123K92 -
 1:03:35
1:03:35
BonginoReport
3 hours agoKirk’s Alleged Killer Dating Hateful Transgender??? - Nightly Scroll w/ Hayley Caronia (Ep.134)
61.5K85 -
 1:01:12
1:01:12
The Nick DiPaolo Show Channel
5 hours agoKirk Assassination Exposes Insane Left | The Nick Di Paolo Show #1793
25.9K14 -
 LIVE
LIVE
The Mike Schwartz Show
3 hours agoTHE MIKE SCHWARTZ SHOW Evening Edition 09-15-2025
5,040 watching -
 LIVE
LIVE
LIVE WITH CHRIS'WORLD
5 hours agoLIVE WITH CHRIS'WORLD - They Just Created 1 Million Charlie Kirks
136 watching -
 LIVE
LIVE
Quite Frankly
6 hours agoStaggering Evil, Official Stories & Open Lines | Rich Baris 9/15/25
746 watching -
 1:09:33
1:09:33
TheCrucible
4 hours agoThe Extravaganza! EP: 36 (9/15/25)
154K17 -
 1:13:06
1:13:06
Candace Show Podcast
3 hours agoThey Are Lying About Charlie Kirk. | Candace Ep 235
75.9K390