Premium Only Content
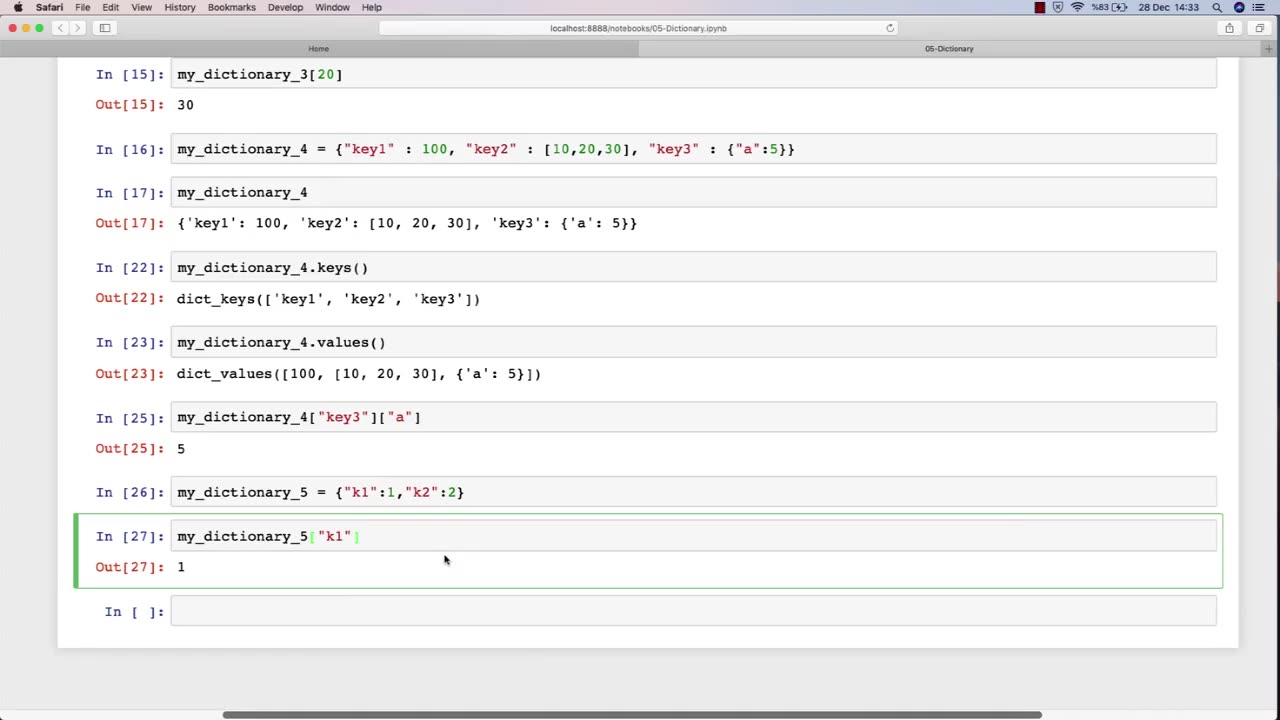
Chapter-27, PEC-10 | Dictionary | #ethicalhacking #hacking #education #growthhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
Dictionary: "Ethical Hacking Terminology"
Description: The ethical hacking terminology dictionary is a collection of technical terms and jargon commonly used in the field of ethical hacking. These terms are used to describe various tools, techniques, and methodologies used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a list of some of the common terms that may be included in an ethical hacking course:
Exploit - A piece of software or code that takes advantage of a vulnerability in a computer system or network.
Payload - The part of an exploit that performs a malicious action, such as stealing data or taking control of a system.
Vulnerability - A weakness in a computer system or network that can be exploited by attackers to gain unauthorized access or perform malicious actions.
Penetration Testing - The process of identifying and exploiting vulnerabilities in a computer system or network to assess its security posture.
Social Engineering - The use of psychological manipulation to trick people into revealing sensitive information or performing actions that are harmful to their organization.
Malware - Software that is designed to perform malicious actions, such as stealing data or taking control of a system.
Brute Force Attack - A method of guessing a password by trying every possible combination until the correct one is found.
Rootkit - A type of malware that hides its presence on a system and gives an attacker privileged access to the system.
Denial of Service (DoS) Attack - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Firewall - A security measure that monitors and controls incoming and outgoing network traffic to prevent unauthorized access.
The ethical hacking terminology dictionary is an important resource for students to learn and understand the technical terms and jargon used in the field of ethical hacking. By mastering these terms, students can communicate effectively with other professionals in the field and better understand the technical aspects of ethical hacking.
-
 LIVE
LIVE
The Quartering
1 hour agoPAM BONDI MELTDOWN, TRANS MONSTER TAKES 10 LIVES, MAMDANI FALLING APART & EPSTEIN REVEAL!
7,905 watching -
 LIVE
LIVE
Dr Disrespect
3 hours ago🔴LIVE - DR DISRESPECT - ROCKET LEAGUE PRO TRYOUTS (Am I Ready?!)
1,114 watching -
 LIVE
LIVE
MattMorseTV
1 hour ago🔴They just DROPPED a NUKE...🔴
3,307 watching -
 LIVE
LIVE
Darkhorse Podcast
2 hours agoThe 313th Evolutionary Lens with Bret Weinstein and Heather Heying
274 watching -
 6:18
6:18
Buddy Brown
2 hours ago $0.23 earnedAmericans Ain't Buying the "White House Version" on EL Paso! | Buddy Brown
31519 -
 1:04:20
1:04:20
DeVory Darkins
2 hours agoPam Bondi UNLOADS on Congress in SCREAMING MATCH regarding Epstein Debacle
120K62 -
 1:00:06
1:00:06
Timcast
3 hours agoTRANS SHOOTER COVERUP?
139K53 -
 1:04:48
1:04:48
BonginoReport
4 hours agoGuthrie Kidnapping Case Blows Wide Open - Scrolling w/ Hayley (Ep. 233) - 02/11/26
90.9K43 -
 1:15:15
1:15:15
Sean Unpaved
3 hours agoTom Brady Gives Logan Paul A Brutal REALITY CHECK! | UNPAVED
18.7K3 -

Zach Costello
3 hours agoCandace Owens Calls on Cops to Question Erika Kirk! Carrie Prejean Boller FIRED!!!
4.03K1