Premium Only Content
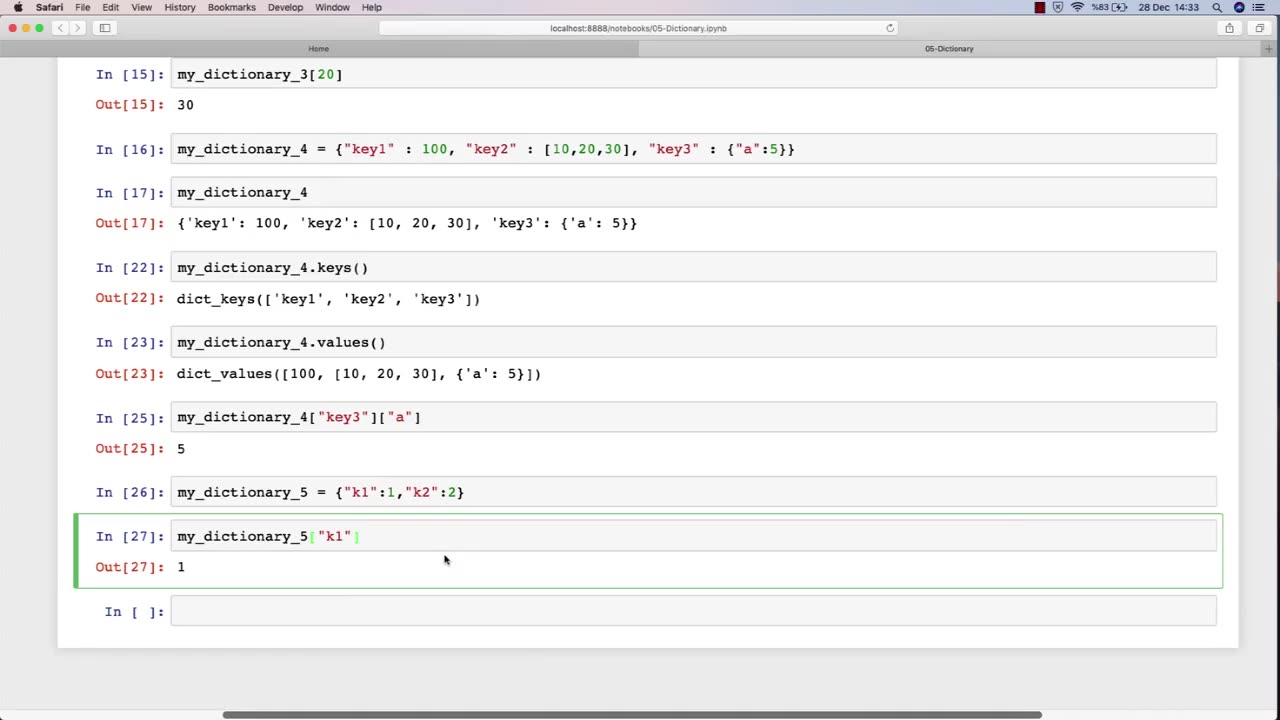
Chapter-27, PEC-10 | Dictionary | #ethicalhacking #hacking #education #growthhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
Dictionary: "Ethical Hacking Terminology"
Description: The ethical hacking terminology dictionary is a collection of technical terms and jargon commonly used in the field of ethical hacking. These terms are used to describe various tools, techniques, and methodologies used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a list of some of the common terms that may be included in an ethical hacking course:
Exploit - A piece of software or code that takes advantage of a vulnerability in a computer system or network.
Payload - The part of an exploit that performs a malicious action, such as stealing data or taking control of a system.
Vulnerability - A weakness in a computer system or network that can be exploited by attackers to gain unauthorized access or perform malicious actions.
Penetration Testing - The process of identifying and exploiting vulnerabilities in a computer system or network to assess its security posture.
Social Engineering - The use of psychological manipulation to trick people into revealing sensitive information or performing actions that are harmful to their organization.
Malware - Software that is designed to perform malicious actions, such as stealing data or taking control of a system.
Brute Force Attack - A method of guessing a password by trying every possible combination until the correct one is found.
Rootkit - A type of malware that hides its presence on a system and gives an attacker privileged access to the system.
Denial of Service (DoS) Attack - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Firewall - A security measure that monitors and controls incoming and outgoing network traffic to prevent unauthorized access.
The ethical hacking terminology dictionary is an important resource for students to learn and understand the technical terms and jargon used in the field of ethical hacking. By mastering these terms, students can communicate effectively with other professionals in the field and better understand the technical aspects of ethical hacking.
-
 4:49
4:49
Russell Brand
11 hours agoThis is Unbelievable...
41.6K45 -
 LIVE
LIVE
Badlands Media
11 hours agoDEFCON ZERQ Ep. 012: Featuring "AND WE KNOW" and a Special Guest
7,978 watching -
 2:56:36
2:56:36
TimcastIRL
5 hours agoLEAKED Memo Says NO BACK PAY For Federal Workers Amid Government Shutdown | Timcast IRL
265K161 -
 2:01:55
2:01:55
Inverted World Live
5 hours agoAI Robin Williams, Lab Grown Human Eggs, and Car-Sized Pumpkins | Ep. 119
12.4K3 -
 1:55:35
1:55:35
Turning Point USA
4 hours agoTPUSA Presents This is The Turning Point Tour LIVE with Vivek Ramaswamy!
31.6K19 -
 2:42:55
2:42:55
Laura Loomer
4 hours agoEP148: Remembering October 7th: Two Years Later
21K8 -
 1:35:59
1:35:59
Flyover Conservatives
23 hours agoWARNING! October 7th Unpacked and Exposed: What REALLY Happened?; GEN Z BACKS HAMAS?! - Hannah Faulkner | FOC Show
36.1K2 -
 2:46:11
2:46:11
Barry Cunningham
5 hours agoPRESIDENT TRUMP IS BRINGING THE RECKONING TO THE DEEP STATE!
48.2K33 -
 LIVE
LIVE
Drew Hernandez
3 hours agoCANDACE OWENS LEAKED CHARLIE KIRK MESSAGES CONFIRMED REAL & DEMS PUSH TO TRIGGER CIVIL WAR
1,065 watching -
 55:56
55:56
Sarah Westall
5 hours agoSuperhuman Hearing of the Matrix: Reality is Different w/ Sharry Edwards
29.3K3
