Premium Only Content
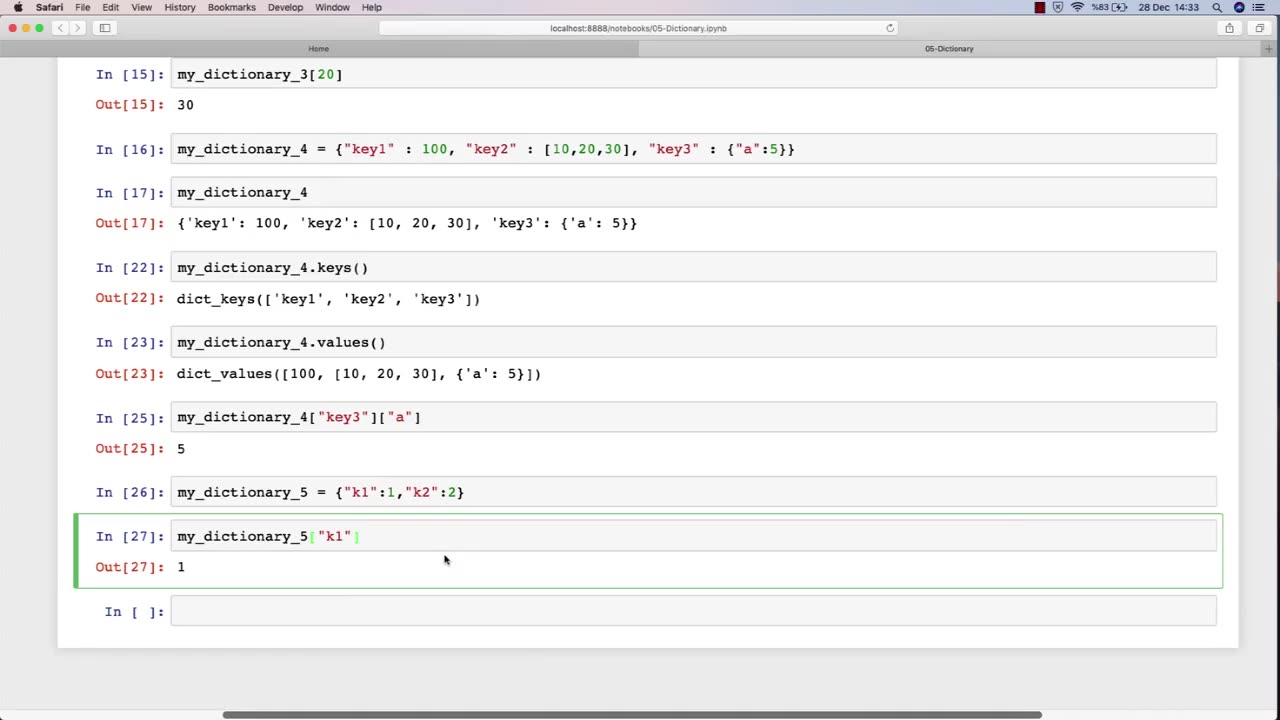
Chapter-27, PEC-10 | Dictionary | #ethicalhacking #hacking #education #growthhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
Dictionary: "Ethical Hacking Terminology"
Description: The ethical hacking terminology dictionary is a collection of technical terms and jargon commonly used in the field of ethical hacking. These terms are used to describe various tools, techniques, and methodologies used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a list of some of the common terms that may be included in an ethical hacking course:
Exploit - A piece of software or code that takes advantage of a vulnerability in a computer system or network.
Payload - The part of an exploit that performs a malicious action, such as stealing data or taking control of a system.
Vulnerability - A weakness in a computer system or network that can be exploited by attackers to gain unauthorized access or perform malicious actions.
Penetration Testing - The process of identifying and exploiting vulnerabilities in a computer system or network to assess its security posture.
Social Engineering - The use of psychological manipulation to trick people into revealing sensitive information or performing actions that are harmful to their organization.
Malware - Software that is designed to perform malicious actions, such as stealing data or taking control of a system.
Brute Force Attack - A method of guessing a password by trying every possible combination until the correct one is found.
Rootkit - A type of malware that hides its presence on a system and gives an attacker privileged access to the system.
Denial of Service (DoS) Attack - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Firewall - A security measure that monitors and controls incoming and outgoing network traffic to prevent unauthorized access.
The ethical hacking terminology dictionary is an important resource for students to learn and understand the technical terms and jargon used in the field of ethical hacking. By mastering these terms, students can communicate effectively with other professionals in the field and better understand the technical aspects of ethical hacking.
-
 2:06:49
2:06:49
vivafrei
18 hours agoEp. 289: Arctic Frost, Boasberg Impeachment, SNAP Funding, Trump - China, Tylenol Sued & MORE!
241K150 -
 2:56:28
2:56:28
IsaiahLCarter
13 hours ago $5.92 earnedThe Tri-State Commission, Election Weekend Edition || APOSTATE RADIO 033 (Guest: Adam B. Coleman)
29.7K4 -
 15:03
15:03
Demons Row
8 hours ago $10.44 earnedThings Real 1%ers Never Do! 💀🏍️
43.5K15 -
 35:27
35:27
megimu32
11 hours agoMEGI + PEPPY LIVE FROM DREAMHACK!
163K12 -
 1:03:23
1:03:23
Tactical Advisor
15 hours agoNew Gun Unboxing | Vault Room Live Stream 044
245K36 -
 19:12
19:12
Robbi On The Record
16 hours ago $21.49 earnedThe Loneliness Epidemic: AN INVESTIGATION
76.9K99 -
 14:45
14:45
Mrgunsngear
1 day ago $141.29 earnedFletcher Rifle Works Texas Flood 30 Caliber 3D Printed Titanium Suppressor Test & Review
132K30 -
 17:17
17:17
Lady Decade
1 day ago $11.42 earnedMortal Kombat Legacy Kollection is Causing Outrage
87.3K16 -
 35:51
35:51
Athlete & Artist Show
1 day ago $14.16 earnedIs Ryan Smith The Best Owner In The NHL?
97.3K15 -
 22:56
22:56
American Thought Leaders
2 days agoCharles Murray: I Thought Religion Was Irrelevant to Me. I Was Wrong.
79.4K40