Premium Only Content
Chapter-27, PEC-10 | Dictionary | #ethicalhacking #hacking #education #growthhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
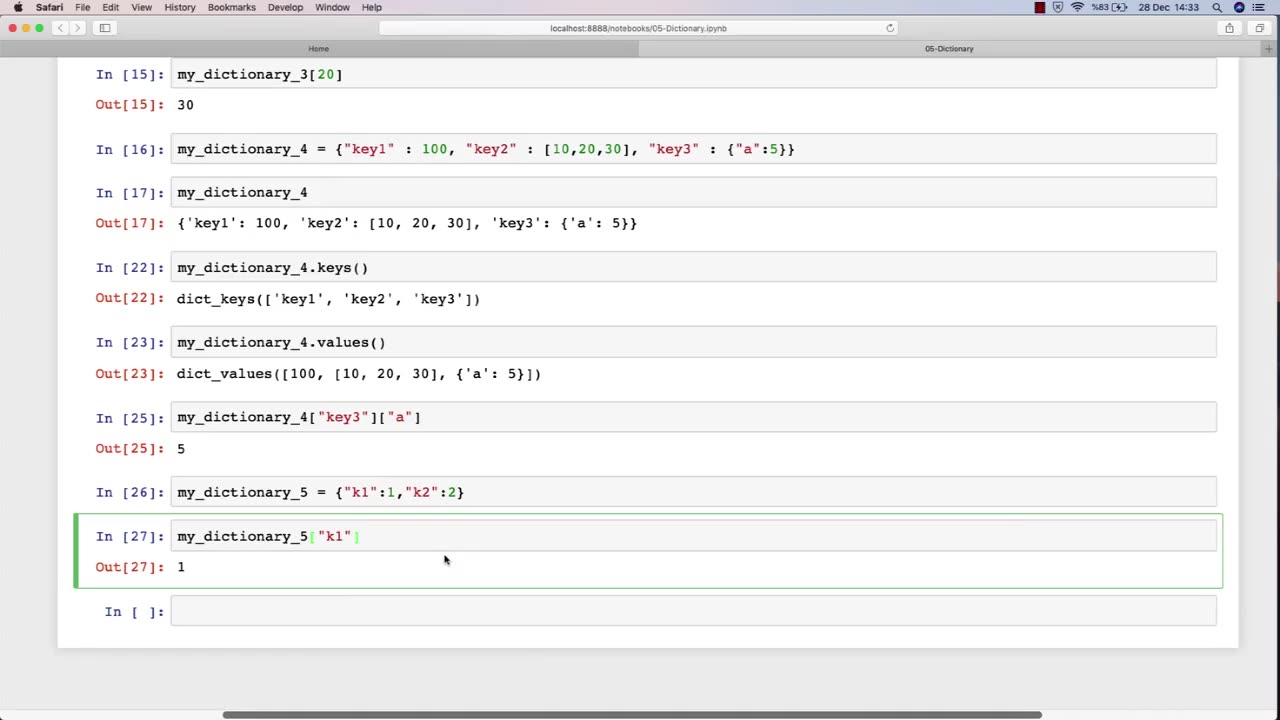
Dictionary: "Ethical Hacking Terminology"
Description: The ethical hacking terminology dictionary is a collection of technical terms and jargon commonly used in the field of ethical hacking. These terms are used to describe various tools, techniques, and methodologies used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a list of some of the common terms that may be included in an ethical hacking course:
Exploit - A piece of software or code that takes advantage of a vulnerability in a computer system or network.
Payload - The part of an exploit that performs a malicious action, such as stealing data or taking control of a system.
Vulnerability - A weakness in a computer system or network that can be exploited by attackers to gain unauthorized access or perform malicious actions.
Penetration Testing - The process of identifying and exploiting vulnerabilities in a computer system or network to assess its security posture.
Social Engineering - The use of psychological manipulation to trick people into revealing sensitive information or performing actions that are harmful to their organization.
Malware - Software that is designed to perform malicious actions, such as stealing data or taking control of a system.
Brute Force Attack - A method of guessing a password by trying every possible combination until the correct one is found.
Rootkit - A type of malware that hides its presence on a system and gives an attacker privileged access to the system.
Denial of Service (DoS) Attack - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Firewall - A security measure that monitors and controls incoming and outgoing network traffic to prevent unauthorized access.
The ethical hacking terminology dictionary is an important resource for students to learn and understand the technical terms and jargon used in the field of ethical hacking. By mastering these terms, students can communicate effectively with other professionals in the field and better understand the technical aspects of ethical hacking.
-
 LIVE
LIVE
Dr Disrespect
9 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - THE GREAT RESET... BEGINS
1,317 watching -
 44:39
44:39
BonginoReport
8 hours agoFun, Faith, and Freedom at Old State Saloon - Nightly Scroll w/ Hayley Caronia (Ep.202)
32.5K7 -
 LIVE
LIVE
The Jimmy Dore Show
1 hour agoDOJ REDACTS Trump From Epstein Files Release! Chappelle Rips Into HYPOCRITE Bill Maher!
6,023 watching -
 LIVE
LIVE
SpartakusLIVE
1 hour agoMAXIMIZED and MOTIVATED this MONDAY w/ Muscle Monster MASCULINITY
121 watching -
 LIVE
LIVE
Akademiks
1 hour agoNicki Minaj goes to Political War? The Game in denial dat kendrick lamar dont fw him. 6ix9ine robber
980 watching -
 2:50:19
2:50:19
Nikko Ortiz
3 hours agoDrops!! Ghost Of Tabor... | Rumble LIVE
1.66K -
 LIVE
LIVE
GritsGG
5 hours ago#1 Warzone Victory Leaderboard! 270+ Ws !
108 watching -
 LIVE
LIVE
ThisIsDeLaCruz
1 hour agoCruz on Crews with Pooch
31 watching -
 33:31
33:31
Jasmin Laine
5 hours agoRoom Goes SILENT as Poilievre WARNS Canadians: “Don’t Let Them Gaslight You”
3.84K13 -
 LIVE
LIVE
Quite Frankly
7 hours agoBoys Will Be Boys, Georgia Election, Christmas Travel | 12/22/25
385 watching