Premium Only Content
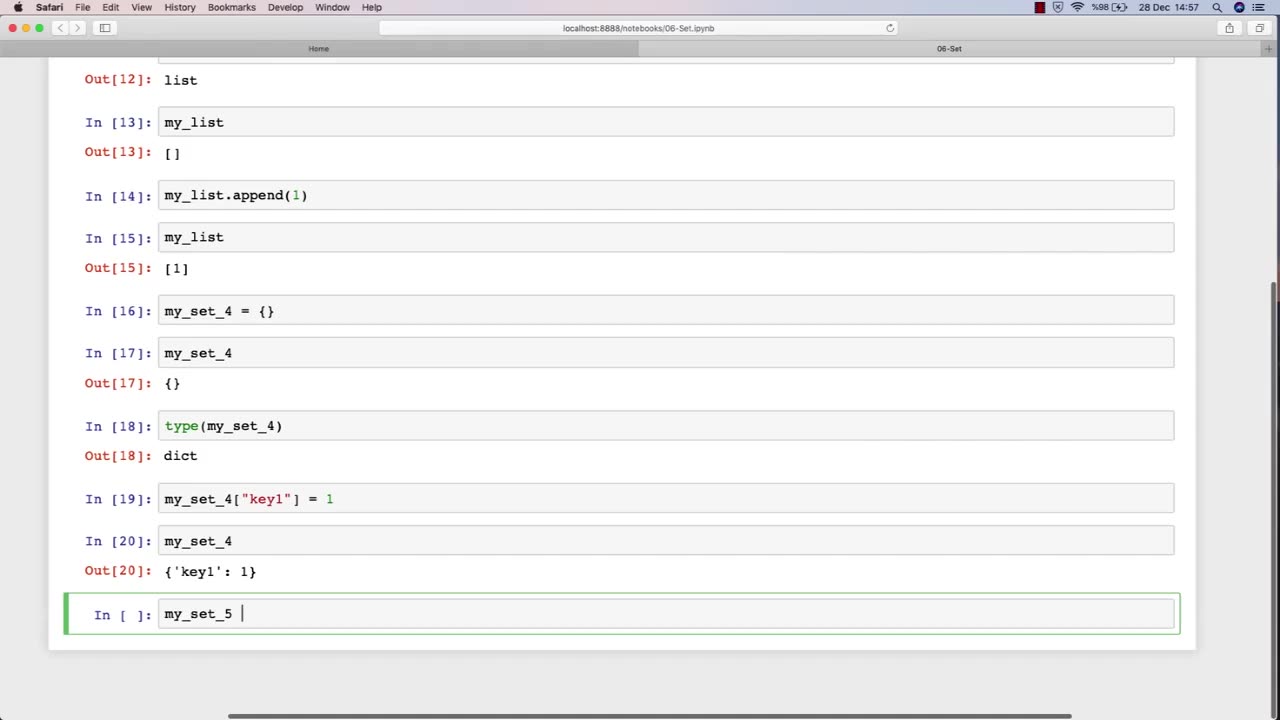
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-

Graham Allen
2 hours agoTold You The War Was FAR From Over… The Blue Wave Just Proved It! Evil Is Fighting Back!
32.9K68 -
 LIVE
LIVE
Badlands Media
8 hours agoBadlands Daily: November 5, 2025
3,408 watching -
 LIVE
LIVE
Wendy Bell Radio
5 hours agoLike Sheep To Slaughter
8,095 watching -
 DVR
DVR
DML
1 hour agoDML LIVE: NYC Goes Socialist: Mamdani’s Victory
2.46K6 -
 1:04:43
1:04:43
Chad Prather
14 hours agoTruth on Trial: When Fear Meets Faith
47.2K27 -
 LIVE
LIVE
LFA TV
13 hours agoLIVE & BREAKING NEWS! | WEDNESDAY 11/5/25
3,370 watching -
 1:57:16
1:57:16
The Chris Salcedo Show
13 hours ago $0.09 earnedDems Win In Dem States...And They Celebrate?
15.7K10 -
 1:04:43
1:04:43
Crypto Power Hour
11 hours ago $0.03 earnedPsychology Of Crypto Market Cycles
28.3K6 -
 9:58
9:58
Clintonjaws
12 days ago $0.17 earnedKaroline Leavitt's Response To 'The View' Host's Nasty Attacks Is Perfect
26.9K24 -
 24:23
24:23
World2Briggs
20 hours ago $0.03 earnedTop 10 Towns You Can Retire on $1900 a month in the Pacific North West.
18.6K9