Premium Only Content
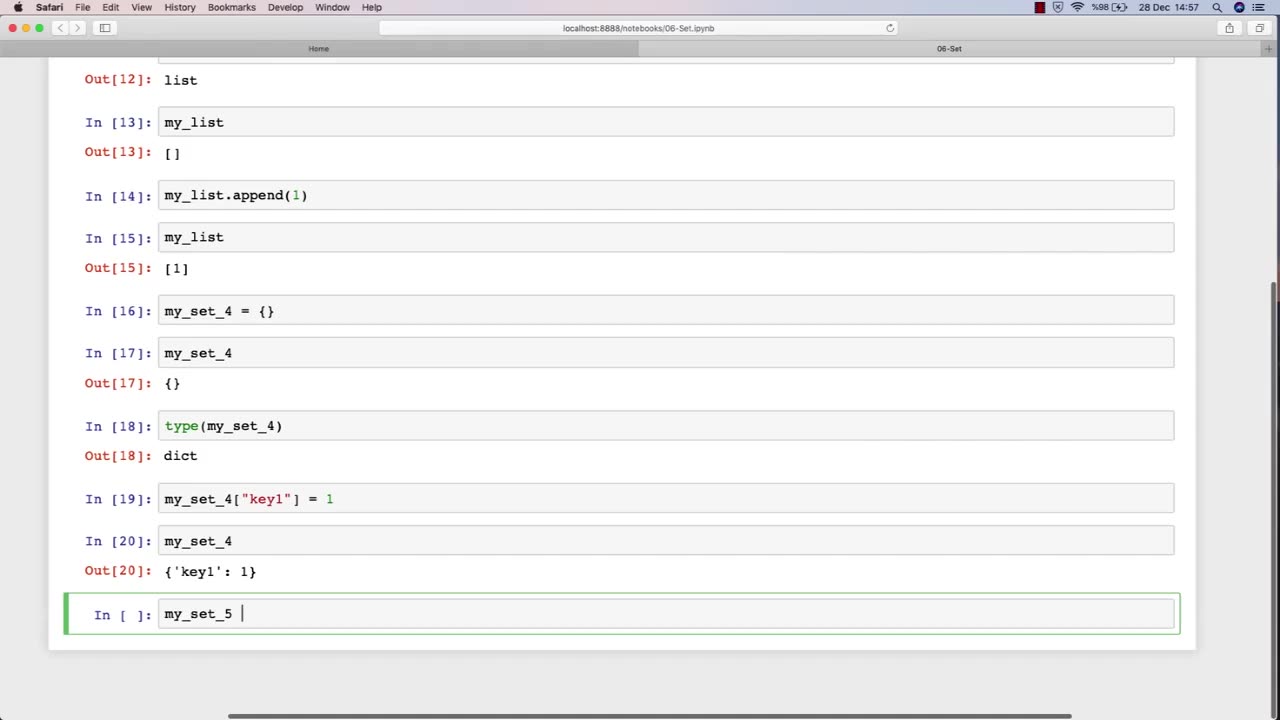
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
Badlands Media
9 hours agoBaseless Conspiracies Ep. 171
5,677 watching -
 2:47:32
2:47:32
TimcastIRL
3 hours agoTPUSA Halftime HITS NUMBER ONE | Timcast IRL #1445 w/ Scott Greer
246K113 -
 LIVE
LIVE
Drew Hernandez
21 hours agoNETANYAHU ATTEMPTS DEFLECTION FROM EPSTEIN FILES AS CONGRESS VIEWS UNREDACTED FILES
968 watching -
 16:53
16:53
Stephen Gardner
3 hours agoWhat Newsom Tried to Hide From Trump & Homan Will Shock You
32.3K34 -
 2:01:56
2:01:56
TheSaltyCracker
4 hours agoWoke Bowl is Dead ReeEStream 02-09-26
79.5K163 -
 54:08
54:08
Amy Dangerfield
2 hours ago $1.16 earnedIyah May: Israel, Faith & Demonic Music Industry
19K5 -
 21:23
21:23
Jasmin Laine
4 hours agoTrump Leaves Canada SPEECHLESS—Demands IMMEDIATE Tariff Negotiations After SECRET China Deal
19.4K23 -
 56:25
56:25
Flyover Conservatives
8 hours agoTwo Halftime Shows, Two Americas: The Propaganda Playbook Revealed; Historic 2-Week Silver Plunge — Setting up $300 - $500 by Summer? - Dr. Kirk Elliott | FOC Show
22.5K -
 1:54:12
1:54:12
Barry Cunningham
4 hours agoLIVE TONIGHT: Ghislaine Maxwell Deposition | Top SB Commercials | TPUSA Halftime Show Watch Party!
77.3K49 -
 8:49:05
8:49:05
Dr Disrespect
12 hours ago🔴LIVE - DR DISRESPECT - WARZONE - NEON HUNTER
145K13