Premium Only Content
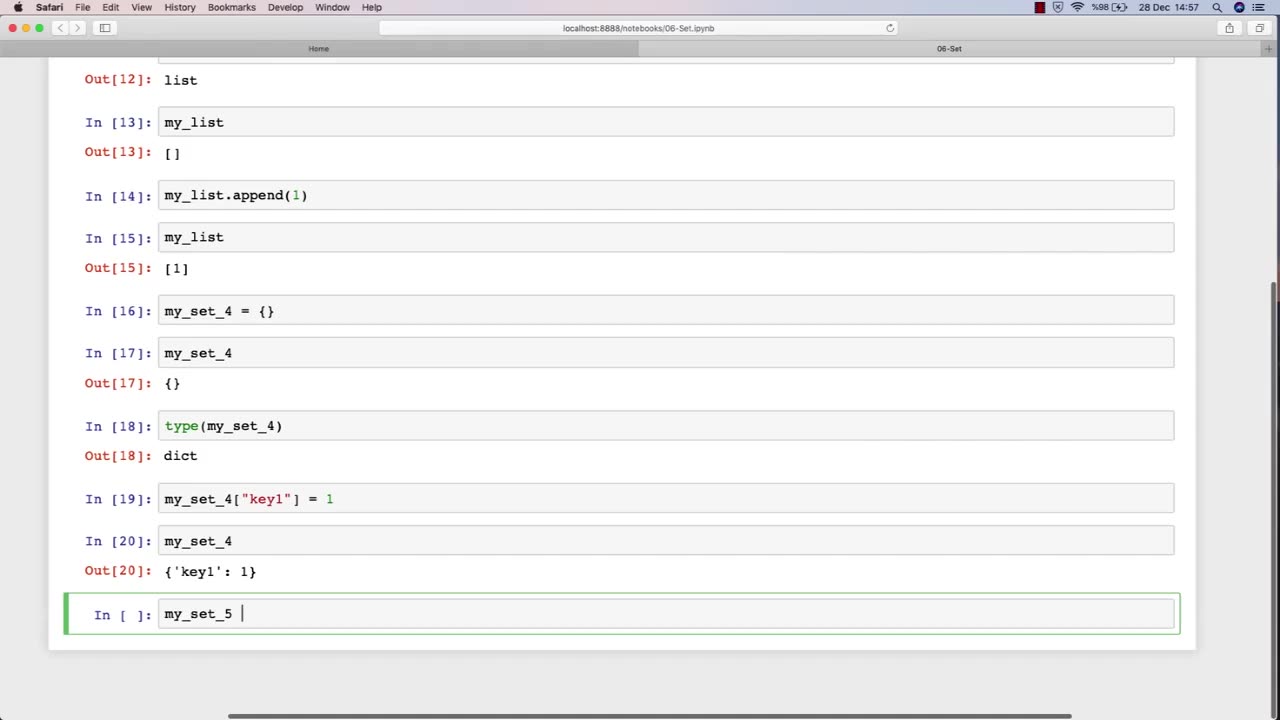
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 41:16
41:16
MattMorseTV
1 hour ago🔴Antifa is PREPARING for WAR.🔴
6.86K61 -
 50:18
50:18
Side Scrollers Podcast
2 hours agoLIVE SPECIAL EVENT - Blabs SPITS on Her Ancestors by BURNING Pasta
7.19K1 -
 LIVE
LIVE
putther
1 hour ago⭐ Bounty Hunting on GTA Online & GTA 5 RP ❗
140 watching -
 LIVE
LIVE
StuffCentral
2 hours agoBad Company Presents: Ball in the fall, Two 1v1 cash prize tournaments back to back!
85 watching -
 LIVE
LIVE
Midnight In The Mountains™
1 hour agoGaming w/ Gaming w/ PER·SE·VER·ANCE | Family Event OVER EARLY! | Midnights Split Stream!
38 watching -
 LIVE
LIVE
Mally_Mouse
6 days ago🌶️ 🥵Spicy BITE Saturday!! 🥵🌶️- Let's Play: Unrailed 2!
124 watching -
 23:53
23:53
MYLUNCHBREAK CHANNEL PAGE
21 hours agoIstanbul SHOULD NOT Exist - Pt 3
22.6K14 -
 LIVE
LIVE
BigTallRedneck
5 hours agoROCKET LEAGUE - STUFF CENTRAL'S 1V1 TOURNEY
75 watching -
 LIVE
LIVE
Phyxicx
2 hours agoRocket League 1v1 Tournament hosted by StuffCentral - 9/27/2025
28 watching -
 3:04:24
3:04:24
Barry Cunningham
6 hours agoPRESIDENT TRUMP HAS LAUNCHED HIS OPERATION TO TAKE DOWN THE DEEP STATE! ARE YOU READY?
62.3K90