Premium Only Content
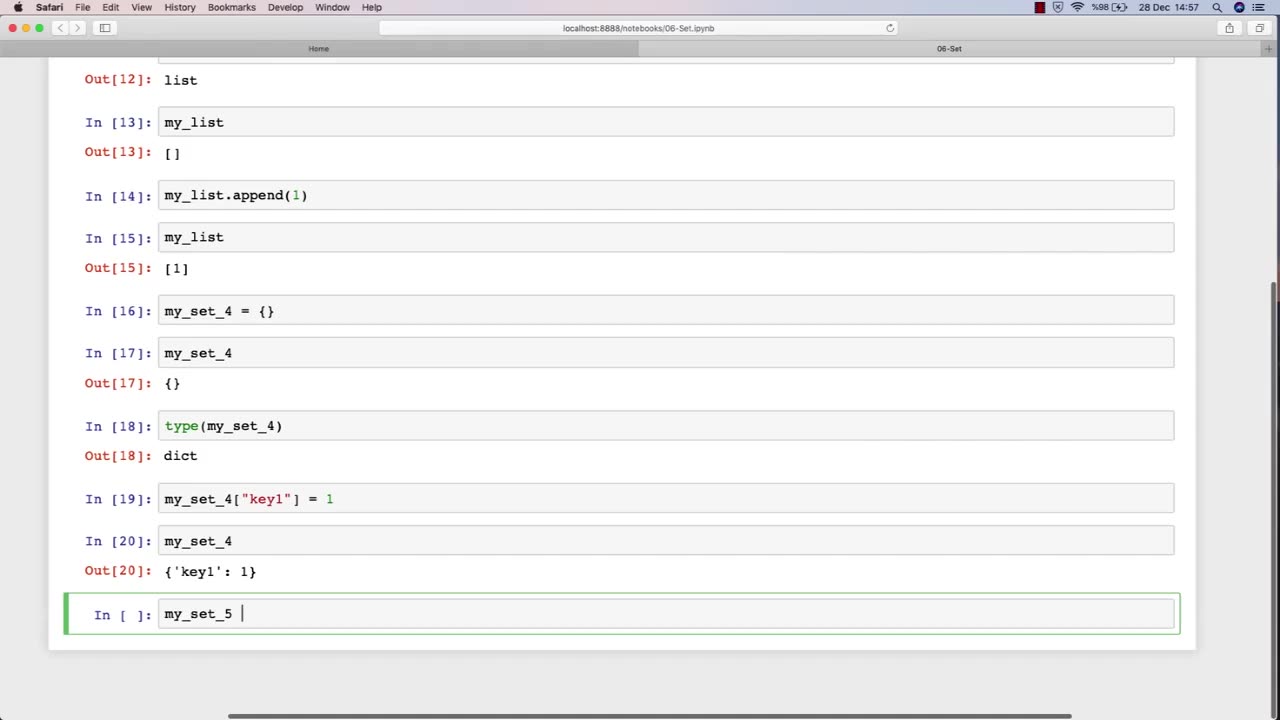
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
The Jimmy Dore Show
2 hours agoFBI Releases HIGHLY DUBIOUS Tyler Robinson Text Chain! Eurovision May BAN Israel! w/ Jose Vega
5,205 watching -
 LIVE
LIVE
Barry Cunningham
1 hour agoJIMMY KIMMEL CANCELLED | OBAMA IS WHINING! | JD VANCE ON JESSE WATTERS!
7,996 watching -
 LIVE
LIVE
TheSaltyCracker
1 hour agoWe Got Him Fired ReeEEStream 9-17-25
12,742 watching -
 LIVE
LIVE
LFA TV
14 hours agoLFA TV ALL DAY STREAM - WEDNESDAY 9/17/25
815 watching -
 DVR
DVR
Stephen Gardner
1 hour ago🔥Trump ERUPTS After Obama’s Charlie Kirk Comments!
1.55K5 -
 LIVE
LIVE
Total Horse Channel
12 hours ago2025 WDAA Western Dressage World Championship Show | Day Two | Arena One
196 watching -
 1:14:40
1:14:40
Glenn Greenwald
2 hours agoThe Right Wages Its Own Cancel Culture War: Lee Fang, Thomas Chatterton Williams, and Leighton Woodhouse on the State of Civil Discourse and More | SYSTEM UPDATE #517
134K23 -
 1:03:04
1:03:04
BonginoReport
3 hours agoBomb Squad Investigates Package at TPUSA HQ - Nightly Scroll w/ Hayley Caronia (Ep.136)
173K56 -
 1:23:11
1:23:11
Kim Iversen
5 hours agoDennis Kucinich Exposes 9/11 Israel's Lies
91.5K152 -
 LIVE
LIVE
The Mike Schwartz Show
3 hours agoTHE MIKE SCHWARTZ SHOW with DR. MICHAEL J SCHWARTZ 09-17-2025
3,766 watching