Premium Only Content
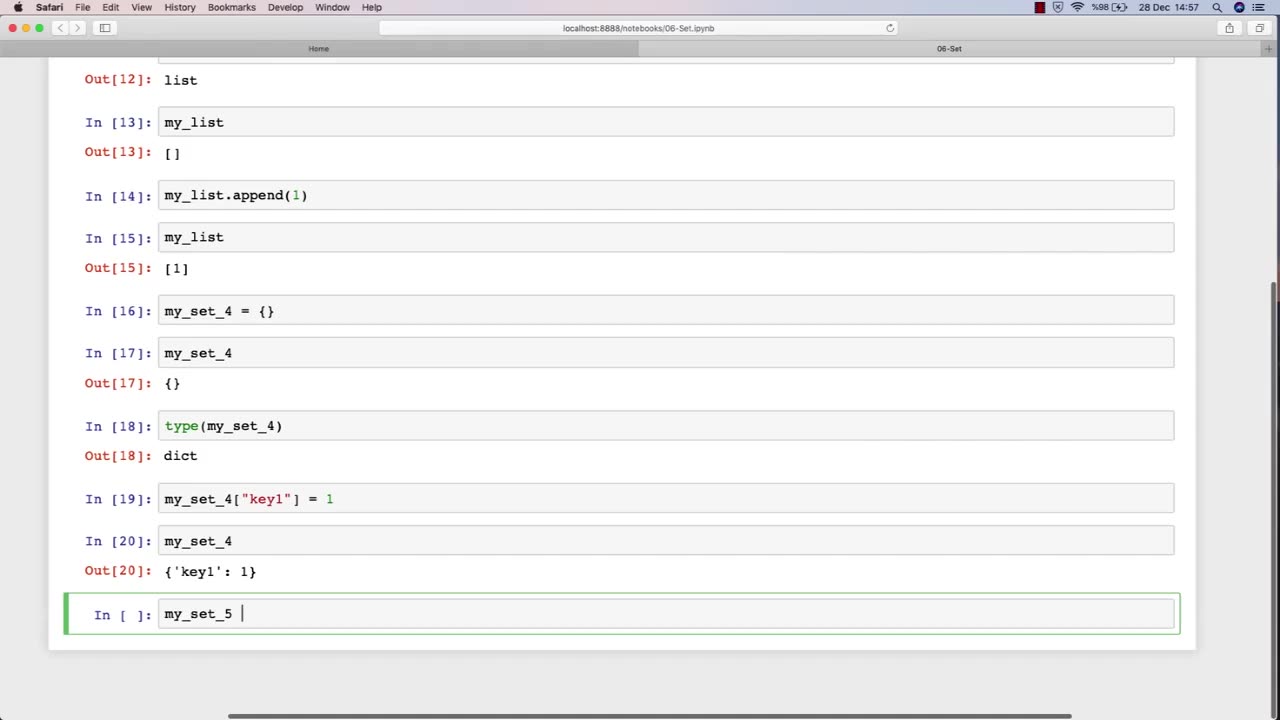
Chapter-27, LEC-11 | Sets | #ethicalhacking #hacking #education #growthhacking #biohacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking
Set: "Tools and Techniques"
Description: The tools and techniques used in ethical hacking refer to the software and hardware tools, as well as the methodologies and approaches, used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a set of some of the common tools and techniques that may be covered in an ethical hacking course:
Network scanners and vulnerability scanners, such as Nmap and Nessus, to identify weaknesses and vulnerabilities in networks and systems.
Password cracking tools, such as John the Ripper and Hashcat, to identify weak passwords and brute-force passwords.
Social engineering techniques, such as phishing and pretexting, to manipulate people into revealing sensitive information or performing actions that are harmful to their organization.
Exploit frameworks, such as Metasploit, to automate the process of identifying and exploiting vulnerabilities in systems and networks.
Packet sniffers and network analysis tools, such as Wireshark and Tcpdump, to capture and analyze network traffic for security purposes.
Forensic tools, such as EnCase and FTK, to gather and analyze digital evidence of security incidents and data breaches.
Malware analysis tools, such as IDA Pro and OllyDbg, to analyze and reverse-engineer malware to understand its functionality and behavior.
Virtualization and sandboxing tools, such as VirtualBox and Cuckoo Sandbox, to create isolated environments for testing and experimenting with potentially harmful software.
The tools and techniques used in ethical hacking are constantly evolving and changing, so it is important for students to stay up-to-date with the latest trends and developments in the field. By mastering these tools and techniques, students can become proficient in ethical hacking and develop the skills necessary to identify and address security vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
The Quartering
1 hour agoNuclear Fallout From Jimmy Kimmel Firing, New Head Of TP USA, Obama Whines
14,298 watching -
 1:28:39
1:28:39
Sean Unpaved
2 hours agoBills-Dolphins TNF Battle, Steelers' D in Crisis, & Coaching Hot Seat Alert!
9.92K -
 DVR
DVR
Human Events Daily with Jack Posobiec
1 hour agoHUMAN EVENTS DAILY WITH JACK POSOBIEC
4.61K8 -
 LIVE
LIVE
LindellTV
1 hour agoTHE MIKE LINDELL SHOW: JIMMY KIMMEL SUSPENDED
345 watching -
 1:57:27
1:57:27
The Charlie Kirk Show
3 hours agoMegyn Kelly Remembers Charlie + Jimmy Kimmel Off the Air | 9.18.2025
253K65 -
 LIVE
LIVE
SternAmerican
23 hours agoElection Integrity Call – Thurs, Sept 18 · 2 PM EST | Featuring Rhode Island
144 watching -
 4:22
4:22
Michael Heaver
2 hours agoLabour Face Brutal UK WIPEOUT
3.97K2 -
 10:32
10:32
Faith Frontline
17 hours agoKenneth Copeland EXPOSED as America’s CREEPIEST Pastor Yet
2.87K3 -
 4:33:50
4:33:50
Right Side Broadcasting Network
22 hours agoLIVE REPLAY: President Trump Holds a Press Conference with Prime Minister Keir Starmer - 9/18/25
70.9K38 -
 1:01:35
1:01:35
The Rubin Report
4 hours agoJimmy Kimmel Humiliated as NY Post Exposes His Dark Reaction to Being Canceled
62.9K101