Premium Only Content
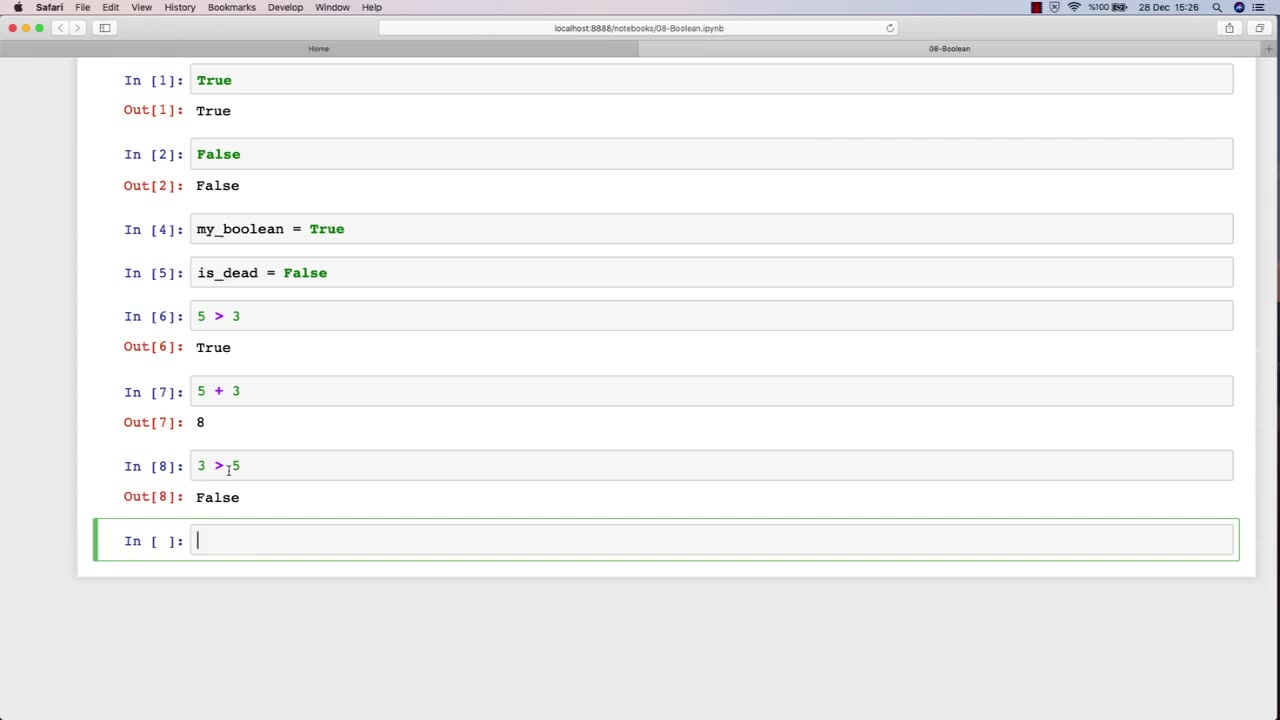
Chapter-27, LEC-13 | 13. Boolean | #ethicalhacking #hacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Boolean: "Security Controls"
Description: In the field of ethical hacking, security controls refer to the various measures and technologies that organizations use to protect their computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction. The following are some examples of security controls that may be covered in an ethical hacking course:
Access controls - The use of passwords, biometrics, and other mechanisms to restrict access to systems and data to authorized users only.
Firewalls - Network security devices that filter traffic based on predefined rules to prevent unauthorized access to networks.
Intrusion detection and prevention systems (IDPS) - Security technologies that monitor network traffic and alert administrators to potential threats or attacks.
Encryption - The use of cryptographic techniques to protect sensitive information from unauthorized disclosure or modification.
Anti-virus and anti-malware software - Programs that detect, prevent, and remove malicious software from systems and networks.
Physical security measures - The use of locks, surveillance cameras, and access control systems to prevent unauthorized physical access to data centers and other critical infrastructure.
Network segmentation - The division of a network into smaller, more secure subnetworks to limit the impact of security breaches.
Incident response plans - Policies and procedures that organizations follow in the event of a security incident or data breach.
In an ethical hacking course, students learn how to identify and test the effectiveness of these security controls by simulating attacks and vulnerabilities. By understanding how these security controls work and their limitations, ethical hackers can help organizations strengthen their security posture and protect against cyber threats.
-
 LIVE
LIVE
Inverted World Live
7 hours agoEpstein’s Blood Experiments, Trump’s UFO Speech, and the 9th Circle of Hell | Ep. 170
4,502 watching -
 2:52:40
2:52:40
TimcastIRL
3 hours agoIT WAS A HOAX | Timcast IRL #1446
199K62 -
 2:31:41
2:31:41
Decoy
4 hours agoHe's cooked now
82.3K10 -
 LIVE
LIVE
Isabella Moody
6 hours agoINSIDE SCOOP: Meeting Clavicular + Updates With His ARREST In AZ
165 watching -
 LIVE
LIVE
DLDAfterDark
1 hour agoGUN CONTROL Is To Keep You Safe from Criminals Right?? Gun Talk
150 watching -
 9:12
9:12
Nicholas Bowling
8 hours agoPreacher Gets MOBBED in Front of POLICE at Pride Festival!
4.36K4 -
 1:04:12
1:04:12
Katie Miller Pod
9 hours ago $0.09 earnedJoe & Tayler Lonsdale on Tech Investments, Life in Texas, & Homeschooling | KMP Ep. 26
129K15 -
 20:07
20:07
Jasmin Laine
4 hours agoTrump Puts Carney on NOTICE—Stalling for a Majority Just Backfired BADLY
7.56K19 -
 DVR
DVR
Flyover Conservatives
6 hours agoThey’ve Been Running the World Since WWII (And You Were Never Told) - Mel K | FOC Show
11.1K2 -
 LIVE
LIVE
Anthony Rogers
1 day agoEpisode 403 - The Epstein Files
80 watching