Premium Only Content
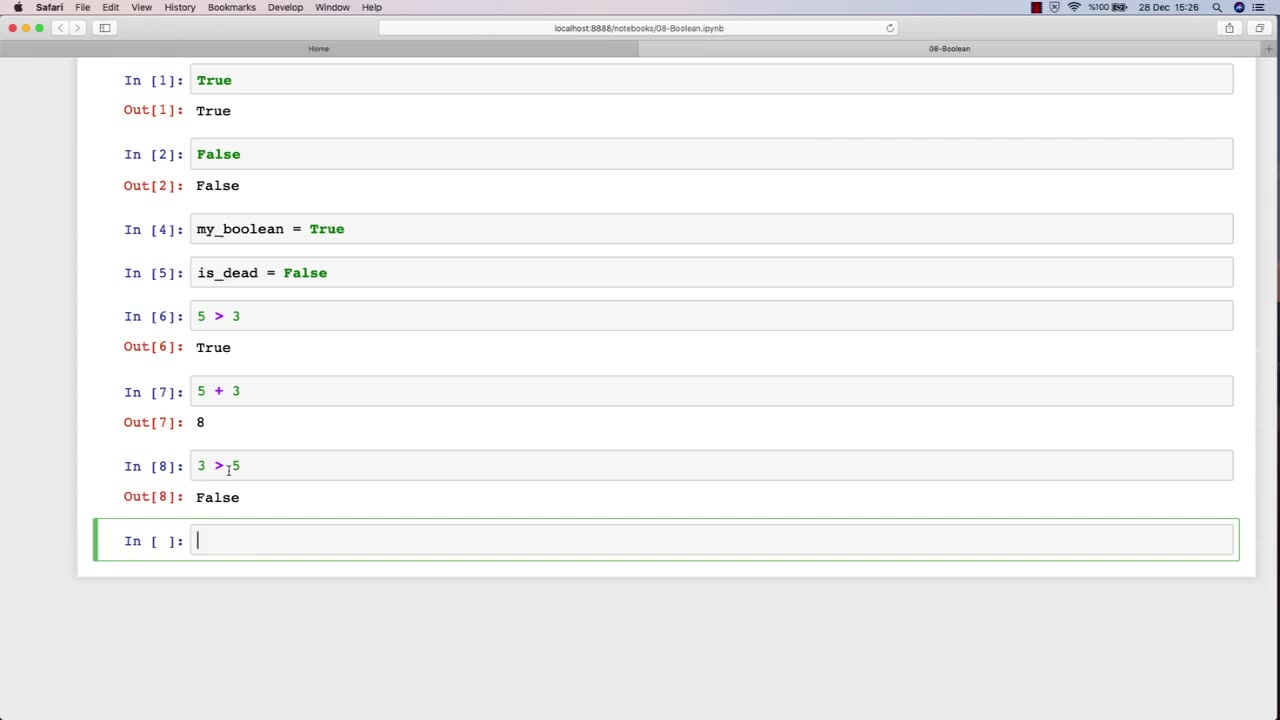
Chapter-27, LEC-13 | 13. Boolean | #ethicalhacking #hacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Boolean: "Security Controls"
Description: In the field of ethical hacking, security controls refer to the various measures and technologies that organizations use to protect their computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction. The following are some examples of security controls that may be covered in an ethical hacking course:
Access controls - The use of passwords, biometrics, and other mechanisms to restrict access to systems and data to authorized users only.
Firewalls - Network security devices that filter traffic based on predefined rules to prevent unauthorized access to networks.
Intrusion detection and prevention systems (IDPS) - Security technologies that monitor network traffic and alert administrators to potential threats or attacks.
Encryption - The use of cryptographic techniques to protect sensitive information from unauthorized disclosure or modification.
Anti-virus and anti-malware software - Programs that detect, prevent, and remove malicious software from systems and networks.
Physical security measures - The use of locks, surveillance cameras, and access control systems to prevent unauthorized physical access to data centers and other critical infrastructure.
Network segmentation - The division of a network into smaller, more secure subnetworks to limit the impact of security breaches.
Incident response plans - Policies and procedures that organizations follow in the event of a security incident or data breach.
In an ethical hacking course, students learn how to identify and test the effectiveness of these security controls by simulating attacks and vulnerabilities. By understanding how these security controls work and their limitations, ethical hackers can help organizations strengthen their security posture and protect against cyber threats.
-
 LIVE
LIVE
The Rubin Report
31 minutes agoBill Maher’s Crowd Stunned as Van Jones Gives a Brutal Message to Liberal Media
1,674 watching -
 LIVE
LIVE
Right Side Broadcasting Network
1 hour agoLIVE: White House Press Secretary Karoline Leavitt Holds a Press Briefing - 10/6/25
1,145 watching -
 LIVE
LIVE
LFA TV
15 hours agoLIVE & BREAKING NEWS! | MONDAY 10/6/25
3,677 watching -
 LIVE
LIVE
Bannons War Room
7 months agoWarRoom Live
12,903 watching -
 1:01:24
1:01:24
VINCE
2 hours agoDomestic Terrorism Is Spreading, And Fast | Episode 140 - 10/06/25
52.4K76 -
 40:58
40:58
Clownfish TV
5 hours agoHollywood is BROKE and JOBLESS?! Animation Most Affected! | Clownfish TV
9003 -
 LIVE
LIVE
Benny Johnson
1 hour agoTrump Deploys National Guard to Chicago as Democrat Leader Caught CALLING For Murder of Republicans
5,635 watching -
 LIVE
LIVE
Caleb Hammer
11 hours ago$300,000 Of Debt To "Flee Trump’s America" | Financial Audit
94 watching -

The Big Mig™
2 hours agoNow We Know Why They Raided Mar A Lago!
1317 -
 LIVE
LIVE
Badlands Media
5 hours agoBadlands Daily: October 6, 2025
4,246 watching
