Premium Only Content
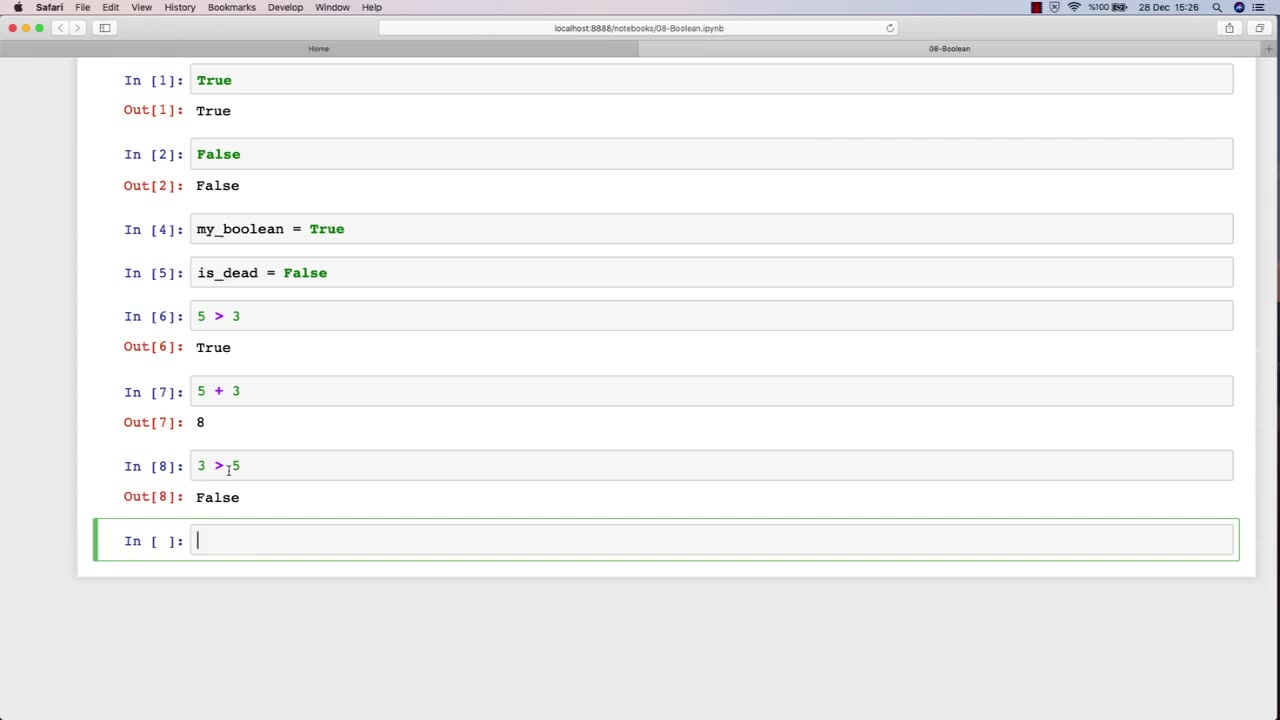
Chapter-27, LEC-13 | 13. Boolean | #ethicalhacking #hacking #education #growthhacking
ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Boolean: "Security Controls"
Description: In the field of ethical hacking, security controls refer to the various measures and technologies that organizations use to protect their computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction. The following are some examples of security controls that may be covered in an ethical hacking course:
Access controls - The use of passwords, biometrics, and other mechanisms to restrict access to systems and data to authorized users only.
Firewalls - Network security devices that filter traffic based on predefined rules to prevent unauthorized access to networks.
Intrusion detection and prevention systems (IDPS) - Security technologies that monitor network traffic and alert administrators to potential threats or attacks.
Encryption - The use of cryptographic techniques to protect sensitive information from unauthorized disclosure or modification.
Anti-virus and anti-malware software - Programs that detect, prevent, and remove malicious software from systems and networks.
Physical security measures - The use of locks, surveillance cameras, and access control systems to prevent unauthorized physical access to data centers and other critical infrastructure.
Network segmentation - The division of a network into smaller, more secure subnetworks to limit the impact of security breaches.
Incident response plans - Policies and procedures that organizations follow in the event of a security incident or data breach.
In an ethical hacking course, students learn how to identify and test the effectiveness of these security controls by simulating attacks and vulnerabilities. By understanding how these security controls work and their limitations, ethical hackers can help organizations strengthen their security posture and protect against cyber threats.
-
 15:31
15:31
MattMorseTV
8 hours ago $10.80 earnedTrump just DROPPED a NUKE...
45.9K76 -
 2:02:45
2:02:45
Side Scrollers Podcast
18 hours agoSide Scrollers Podcast Live | Thursday February 19th 2026
9.16K2 -
 12:00
12:00
MetatronHistory
8 days agoMedieval Kings who Died in Horrible Ways!
8.57K2 -
 11:13
11:13
GritsGG
13 hours agoMy Warzone Graphic Settings & MORE!
4.08K -
 20:50
20:50
MattMorseTV
12 hours ago $7.83 earnedThune is in HOT WATER.
32K59 -
 17:23
17:23
Nikko Ortiz
1 day agoThe President Chose Them Over Delta Force...
52.8K8 -
 29:57
29:57
MetatronCore
2 days agoAndrew Wilson EXPOSES Destiny's LIES
10.8K1 -
 1:21:58
1:21:58
PandaSub2000
5 days agoFive Dates (Trilogy) | MIDNIGHT ADVENTURE CLUB (HD Special)
56.7K7 -
 LIVE
LIVE
Lofi Girl
3 years agolofi hip hop radio 📚 - beats to relax/study to
688 watching -
 1:15:18
1:15:18
The Michelle Moore Show
17 hours ago'Prince Andrew Arrest, Cheap Walmart Meat, EPA Re-Approves Pesticide, Cows Saving the Planet, and more' Guest, Steve Jarvis | The Michelle Moore Show (Feb 19, 2026)
14K8