Premium Only Content
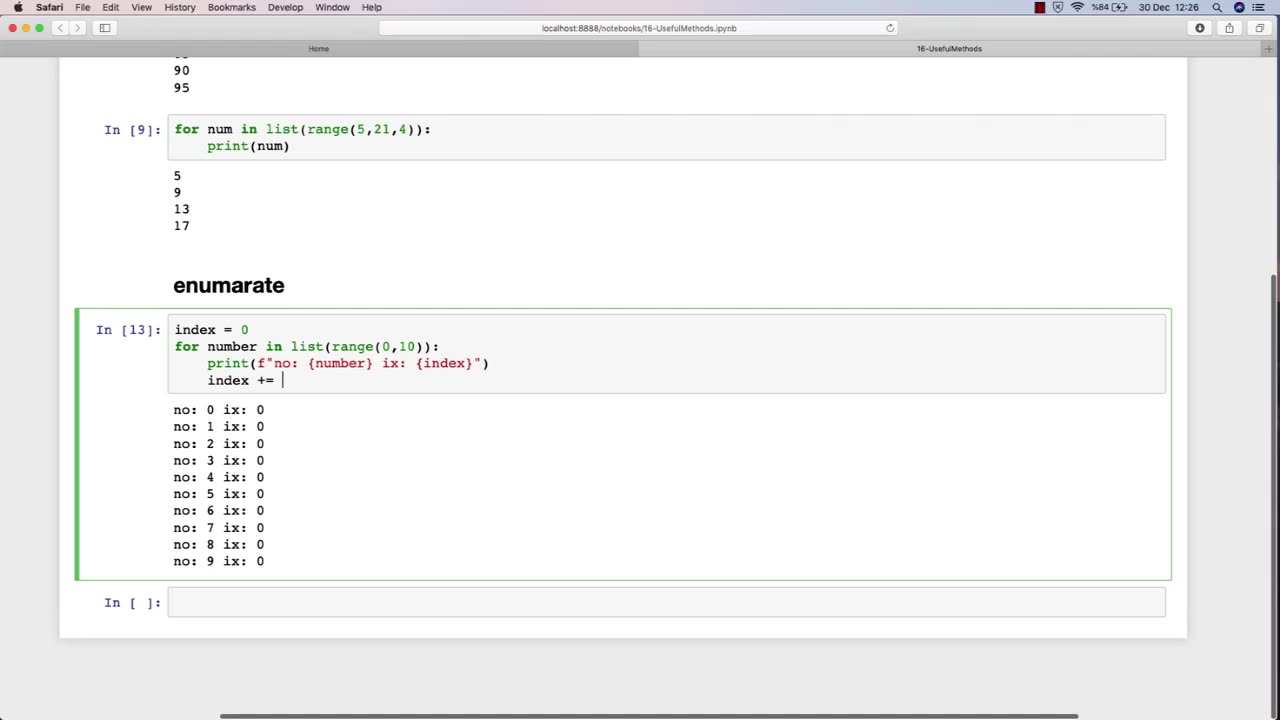
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 LIVE
LIVE
Badlands Media
8 hours agoBadlands Daily: November 5, 2025
2,946 watching -
 LIVE
LIVE
Wendy Bell Radio
5 hours agoLike Sheep To Slaughter
8,006 watching -
 DVR
DVR
DML
1 hour agoDML LIVE: NYC Goes Socialist: Mamdani’s Victory
2.46K4 -
 1:04:43
1:04:43
Chad Prather
14 hours agoTruth on Trial: When Fear Meets Faith
47.2K25 -
 LIVE
LIVE
LFA TV
13 hours agoLIVE & BREAKING NEWS! | WEDNESDAY 11/5/25
3,369 watching -
 1:57:16
1:57:16
The Chris Salcedo Show
13 hours ago $0.09 earnedDems Win In Dem States...And They Celebrate?
15.7K10 -
 1:04:43
1:04:43
Crypto Power Hour
11 hours ago $0.03 earnedPsychology Of Crypto Market Cycles
28.3K6 -
 9:58
9:58
Clintonjaws
12 days ago $0.17 earnedKaroline Leavitt's Response To 'The View' Host's Nasty Attacks Is Perfect
26.9K24 -
 24:23
24:23
World2Briggs
20 hours ago $0.03 earnedTop 10 Towns You Can Retire on $1900 a month in the Pacific North West.
18.6K9 -
 21:23
21:23
Lady Decade
17 hours ago $0.04 earnedThe Lost Sega Neptune Console Refuses To Die !
27.3K5