Premium Only Content
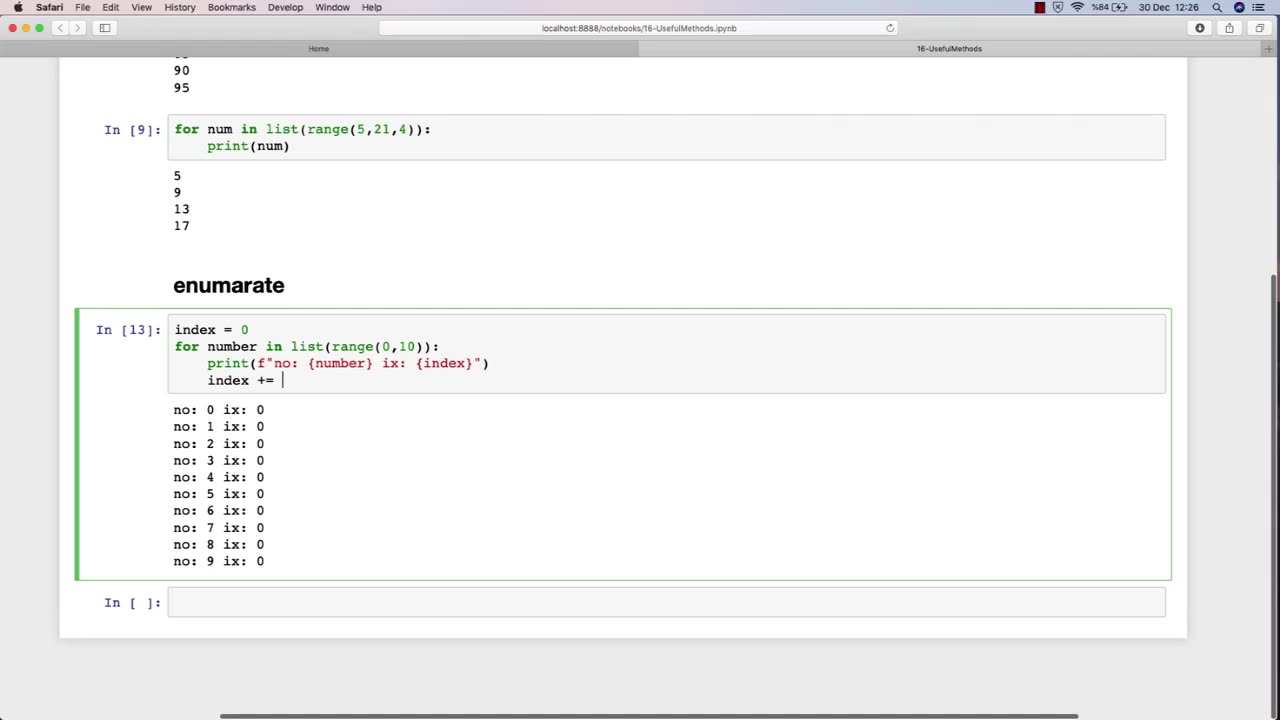
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 LIVE
LIVE
Right Side Broadcasting Network
1 hour agoLIVE: White House Press Secretary Karoline Leavitt Holds a Press Briefing - 10/6/25
1,145 watching -
 LIVE
LIVE
LFA TV
15 hours agoLIVE & BREAKING NEWS! | MONDAY 10/6/25
3,677 watching -
 LIVE
LIVE
Bannons War Room
7 months agoWarRoom Live
12,903 watching -
 1:01:24
1:01:24
VINCE
2 hours agoDomestic Terrorism Is Spreading, And Fast | Episode 140 - 10/06/25
52.4K76 -
 40:58
40:58
Clownfish TV
5 hours agoHollywood is BROKE and JOBLESS?! Animation Most Affected! | Clownfish TV
9003 -
 LIVE
LIVE
Benny Johnson
1 hour agoTrump Deploys National Guard to Chicago as Democrat Leader Caught CALLING For Murder of Republicans
5,635 watching -
 LIVE
LIVE
Caleb Hammer
11 hours ago$300,000 Of Debt To "Flee Trump’s America" | Financial Audit
94 watching -

The Big Mig™
2 hours agoNow We Know Why They Raided Mar A Lago!
1317 -
 LIVE
LIVE
Badlands Media
5 hours agoBadlands Daily: October 6, 2025
4,246 watching -
 1:43:31
1:43:31
Dear America
3 hours agoDems Are The Party Of MURDER?! + TPUSA Debunks Claim By Candace Owens!
70.8K42
