Premium Only Content
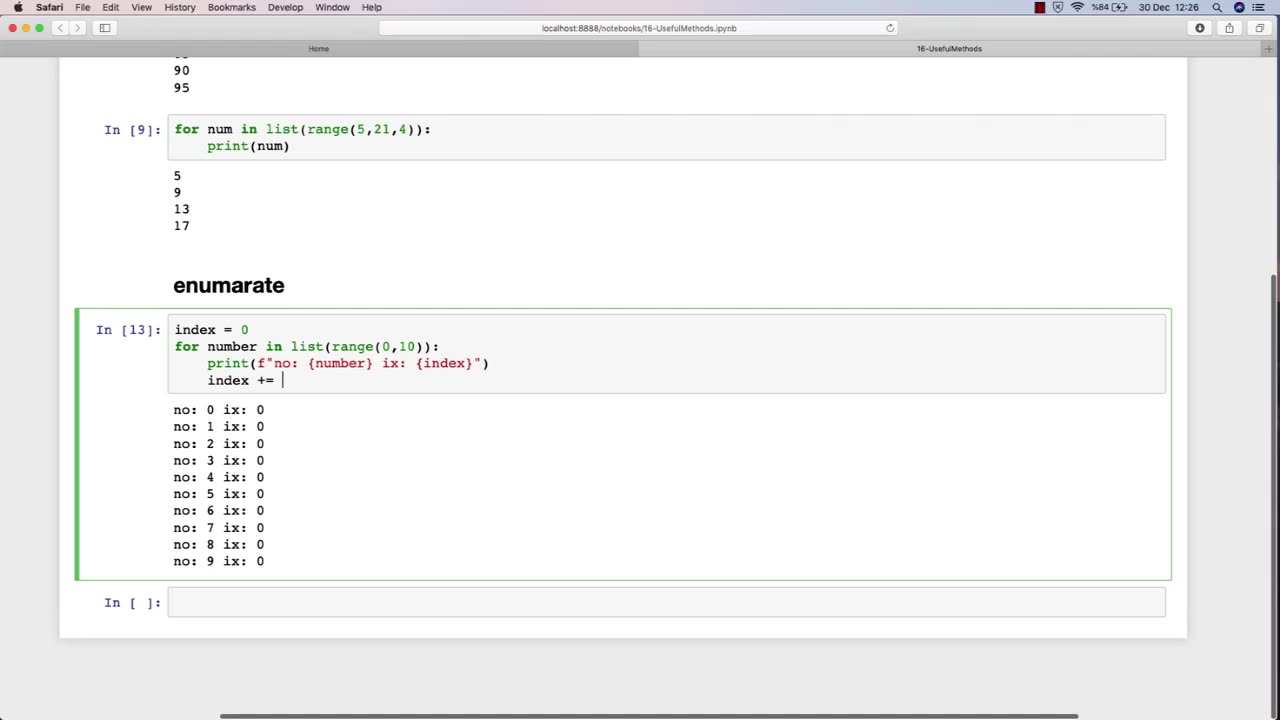
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 4:57:14
4:57:14
Akademiks
10 hours ago21 Savage Wants Young Thug, Wham & Gunna to SQUASH IT! Future Sneak Dissing? Jim Jones Pays 50 Cent?
376K10 -
 6:01:38
6:01:38
Right Side Broadcasting Network
2 days agoLIVE: President Trump to Deliver Remarks in Rocky Mount, NC - 12/19/25
139K57 -
 3:24:48
3:24:48
VapinGamers
9 hours ago $42.91 earnedDestiny 2 - Dungeons and Loot with Friends - !rumbot !music
102K1 -
 2:07:44
2:07:44
TimcastIRL
10 hours agoTrump's Secret Plan To Make Charlie Kirk VP, America Fest IN CIVIL WAR | Timcast IRL
228K210 -
 4:09:13
4:09:13
I_Came_With_Fire_Podcast
18 hours agoLive Fire: Christmas Special
48.2K8 -
 46:26
46:26
Sarah Westall
12 hours agoWhat’s Behind the Silver Surge? Large Institutions Cashing In w/ Andy Schectman
47.8K3 -
 6:42:10
6:42:10
Turning Point USA
17 hours agoLIVE NOW: AMFEST DAY 2 - VIVEK, JACK POSOBIEC, MEGYN KELLY, ALEX CLARK AND MORE…
1.32M189 -
 1:14:37
1:14:37
Flyover Conservatives
1 day agoHow to Win 2026 Before It Starts — Clay Clark’s Goal-Setting Blueprint | FOC Show
48.2K1 -
 12:52
12:52
The Kevin Trudeau Show Limitless
2 days agoBeyond Good And Bad: The Hidden Reality Code
95.6K21 -
 1:03:11
1:03:11
BonginoReport
13 hours agoBrown U Security Failures EXPOSED - Nightly Scroll w/ Hayley Caronia (Ep.201)
168K49