Premium Only Content
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
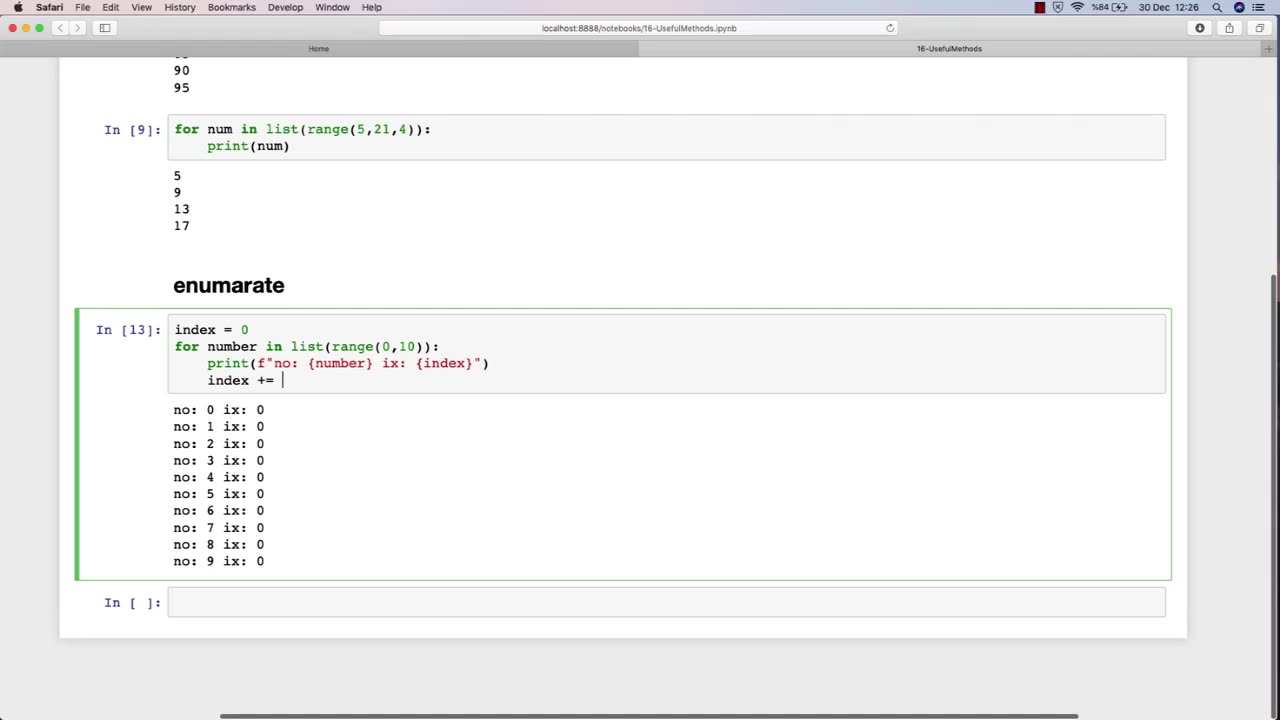
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 50:18
50:18
Side Scrollers Podcast
2 hours agoLIVE SPECIAL EVENT - Blabs SPITS on Her Ancestors by BURNING Pasta
7.19K1 -
 LIVE
LIVE
putther
1 hour ago⭐ Bounty Hunting on GTA Online & GTA 5 RP ❗
143 watching -
 LIVE
LIVE
StuffCentral
2 hours agoBad Company Presents: Ball in the fall, Two 1v1 cash prize tournaments back to back!
87 watching -
 LIVE
LIVE
Midnight In The Mountains™
1 hour agoGaming w/ Gaming w/ PER·SE·VER·ANCE | Family Event OVER EARLY! | Midnights Split Stream!
37 watching -
 LIVE
LIVE
Mally_Mouse
6 days ago🌶️ 🥵Spicy BITE Saturday!! 🥵🌶️- Let's Play: Unrailed 2!
122 watching -
 23:53
23:53
MYLUNCHBREAK CHANNEL PAGE
21 hours agoIstanbul SHOULD NOT Exist - Pt 3
22.6K14 -
 LIVE
LIVE
BigTallRedneck
5 hours agoROCKET LEAGUE - STUFF CENTRAL'S 1V1 TOURNEY
75 watching -
 LIVE
LIVE
Phyxicx
2 hours agoRocket League 1v1 Tournament hosted by StuffCentral - 9/27/2025
26 watching -
 3:04:24
3:04:24
Barry Cunningham
6 hours agoPRESIDENT TRUMP HAS LAUNCHED HIS OPERATION TO TAKE DOWN THE DEEP STATE! ARE YOU READY?
62.3K90 -
 DVR
DVR
The Sufari Hub
55 minutes ago🔴LIVE - THE BIG TRIP - DAY 3 - GOING TO BASSLAKE