Premium Only Content
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
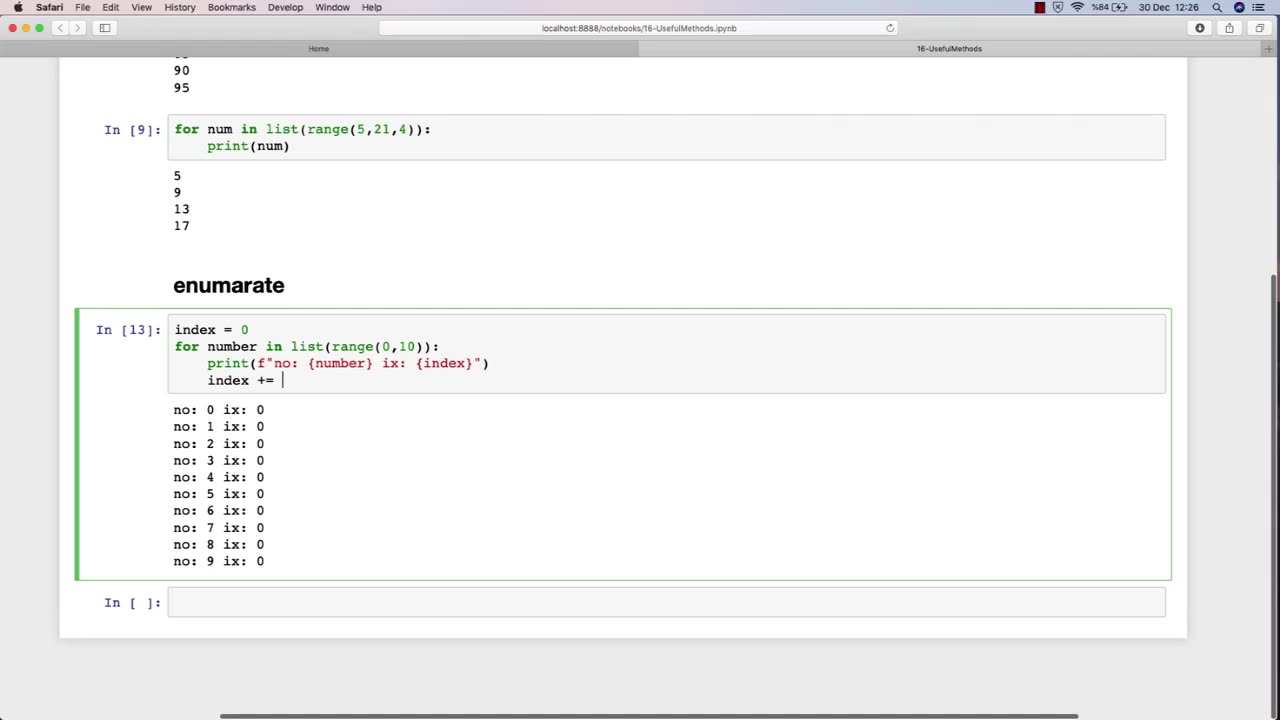
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 1:55:20
1:55:20
The White House
4 hours agoPresident Trump Participates in the Memorial Service for Charlie Kirk
36.9K43 -
 UPCOMING
UPCOMING
Sarah Westall
3 hours agoDomestic Terror Operation: Death Threats, Smear Campaigns, Gang Stalking w/ Journalist Sarah Fields
788 -
 DVR
DVR
Nerdrotic
3 hours ago $4.12 earnedGobekli Tepe Discovery and "Reconstruction" | Forbidden Frontier #118
27.3K2 -
 29:07
29:07
Tactical Advisor
3 hours agoATF Changes Ruling on SBR & Tacpack unboxing | Vault Room Live Stream 039
28.2K9 -
 22:09
22:09
Tundra Tactical
7 hours ago $0.10 earnedStupid Gun Myths & Questions Ep. 1 🛑NEW SERISE!!🛑
2971 -
 2:00
2:00
From Zero → Viral with AI
9 hours agoAre You Being Left Behind? Why AI Marketing is No Longer Optional
7 -
 9:10
9:10
BlackDiamondGunsandGear
6 hours agoI Finally Got it! / Now i need to BUILD IT!
2071 -
 9:44
9:44
Millionaire Mentor
3 days agoCharlie Kirk Brings Woke Student To STUTTERING Over White Privilege Lies
1535 -
 24:12
24:12
MudandMunitions
7 hours agoOff-Roading with NYPrepper Wild Elk & PA’s Most Remote Backroads
23 -
 LIVE
LIVE
Bannons War Room
7 months agoWarRoom Live
5,260 watching