Premium Only Content
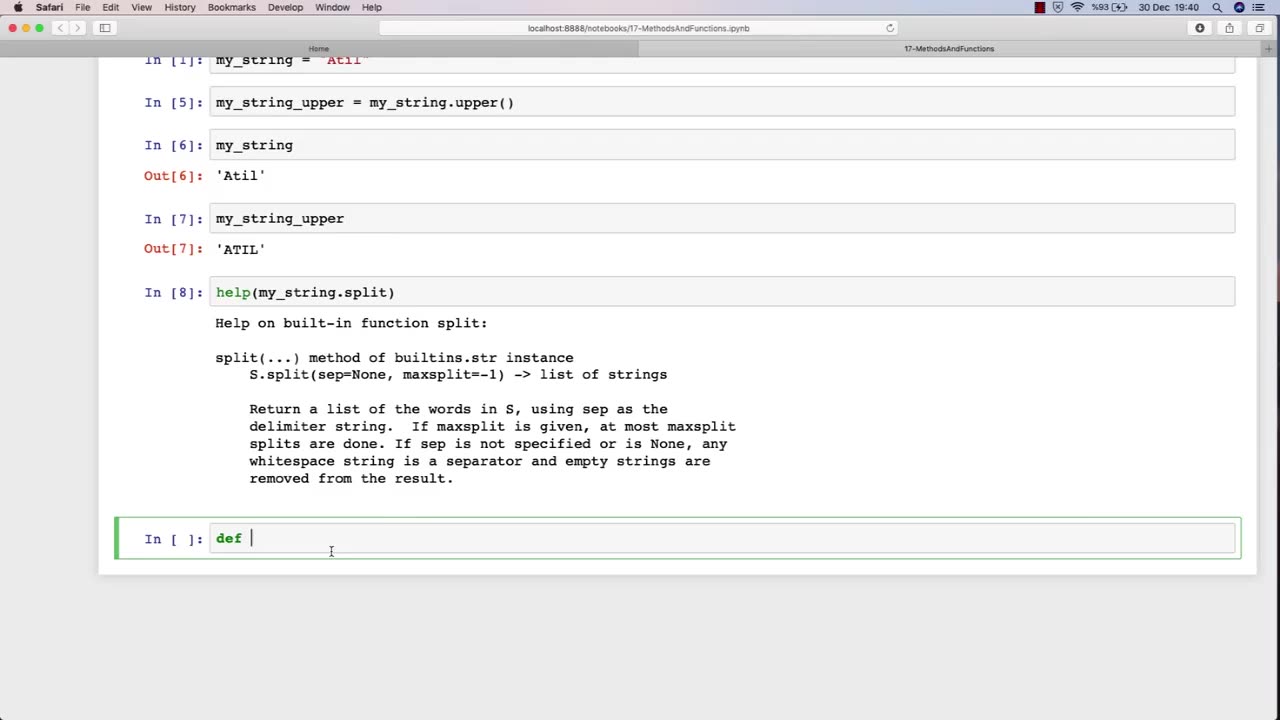
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 1:02:14
1:02:14
BonginoReport
3 hours agoICE Director Faces Congress as SAVE Act Ignites GOP Debate | Episode 223 – (02/11/26) VINCE
132K104 -
 LIVE
LIVE
Badlands Media
8 hours agoBadlands Daily: 2/11/26
2,898 watching -
 1:30:04
1:30:04
Whiskey and Windage Podcast
3 hours ago $0.19 earnedInside Faxon: Innovation, Barrels, and the Future of American Firearm Manufacturing
4.33K -
 14:52
14:52
Chris From The 740
13 hours ago $0.05 earnedGowutar EP-10 Review: Multi-Reticle, Enclosed Emitter, Budget Price!
2.79K -
 1:14:36
1:14:36
Chad Prather
18 hours agoWhen God Is the Only Audience
72.2K32 -
 1:31:53
1:31:53
Surviving The Survivor: #BestGuests in True Crime
1 day agoSavannah Guthrie Posts NEW Video in "Hour of Desperation" as Ransom Deadline for Mom Approaches
11.9K3 -
 38:11
38:11
ZeeeMedia
17 hours agoLes Wexner Named Co-Conspirator in Epstein Files, More Names Released | Daily Pulse Ep 194
16.6K26 -
 LIVE
LIVE
LFA TV
13 hours agoLIVE & BREAKING NEWS! | WEDNESDAY 2/11/26
2,518 watching -
 1:28:57
1:28:57
Crypto Power Hour
14 hours ago $2.70 earnedNFT The Movie, The Circus Is In Town With Jeff Crane & Miriam Reza
39.3K7 -
 54:08
54:08
Amy Dangerfield
1 day ago $14.06 earnedIyah May: Israel, Faith & Demonic Music Industry
112K37