Premium Only Content
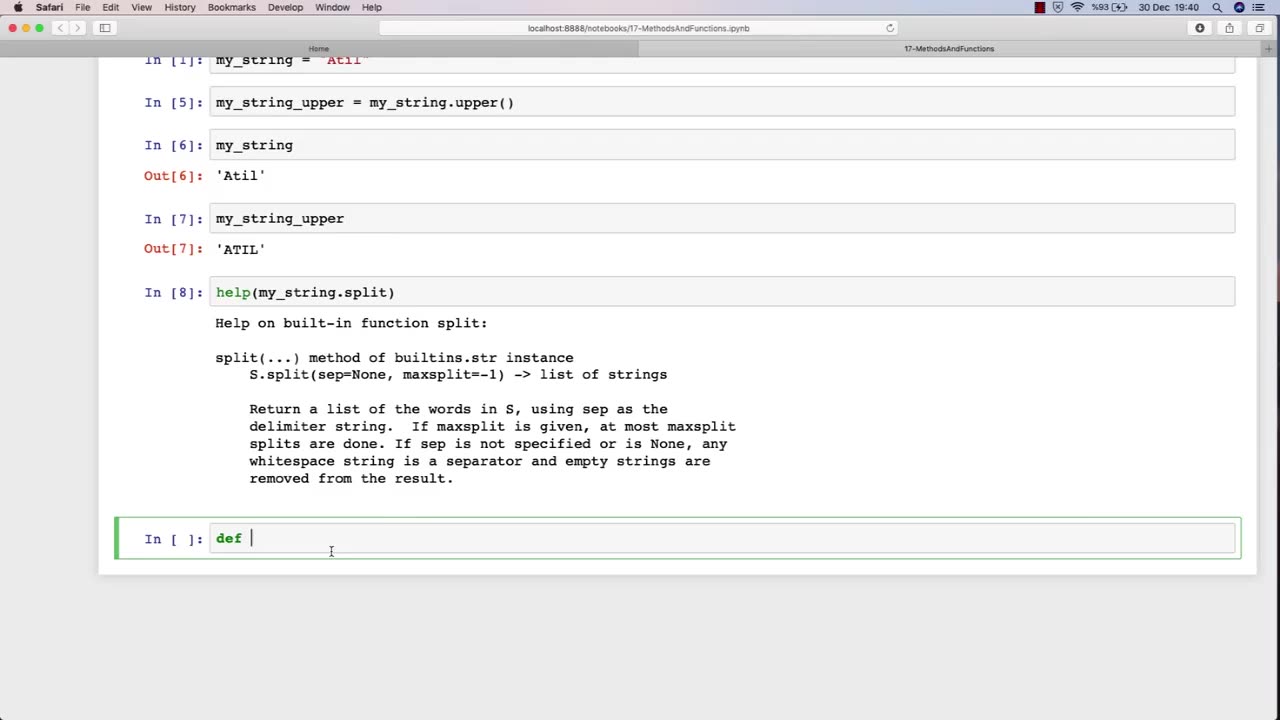
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 LIVE
LIVE
Right Side Broadcasting Network
1 hour agoLIVE: White House Press Secretary Karoline Leavitt Holds a Press Briefing - 10/6/25
1,145 watching -
 LIVE
LIVE
LFA TV
15 hours agoLIVE & BREAKING NEWS! | MONDAY 10/6/25
3,677 watching -
 LIVE
LIVE
Bannons War Room
7 months agoWarRoom Live
12,903 watching -
 1:01:24
1:01:24
VINCE
2 hours agoDomestic Terrorism Is Spreading, And Fast | Episode 140 - 10/06/25
52.4K79 -
 40:58
40:58
Clownfish TV
5 hours agoHollywood is BROKE and JOBLESS?! Animation Most Affected! | Clownfish TV
9003 -
 LIVE
LIVE
Benny Johnson
1 hour agoTrump Deploys National Guard to Chicago as Democrat Leader Caught CALLING For Murder of Republicans
5,635 watching -
 LIVE
LIVE
Caleb Hammer
11 hours ago$300,000 Of Debt To "Flee Trump’s America" | Financial Audit
94 watching -
 12:37
12:37
The Big Mig™
2 hours agoNow We Know Why They Raided Mar A Lago!
1317 -
 LIVE
LIVE
Badlands Media
5 hours agoBadlands Daily: October 6, 2025
4,246 watching -
 1:43:31
1:43:31
Dear America
3 hours agoDems Are The Party Of MURDER?! + TPUSA Debunks Claim By Candace Owens!
70.8K42
