Premium Only Content
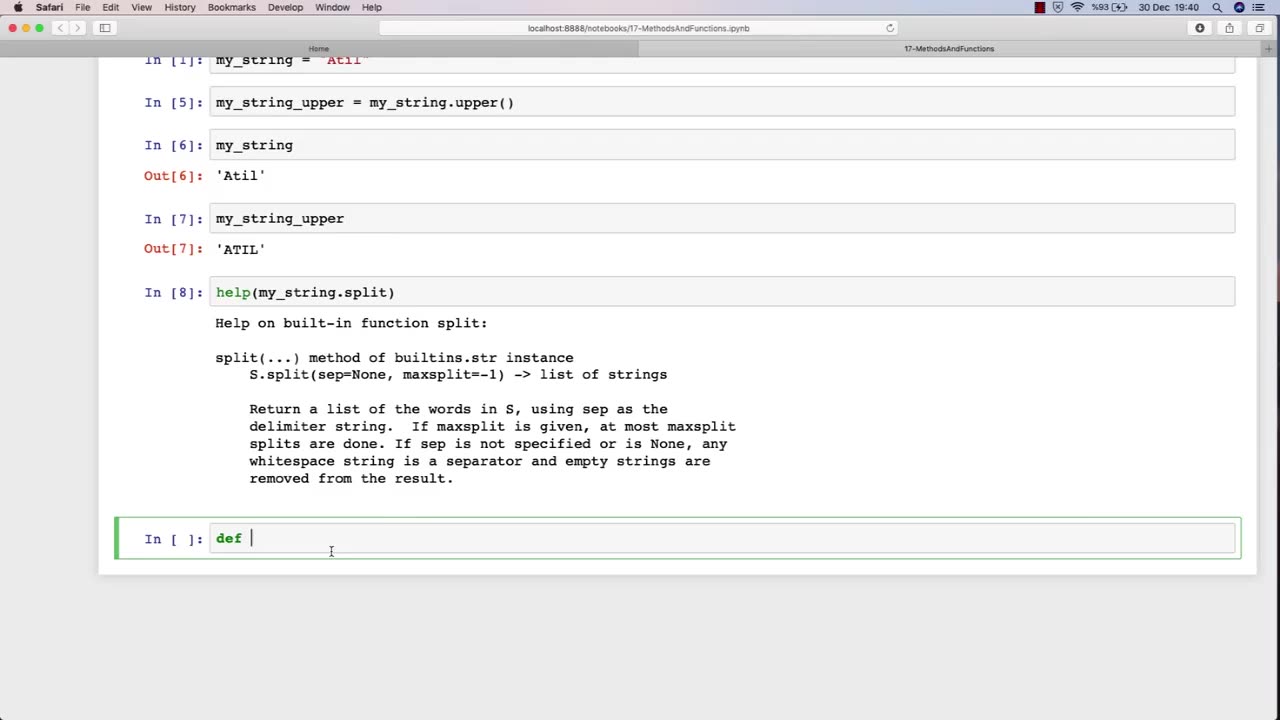
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 LIVE
LIVE
MattMorseTV
1 hour ago🔴Reacting to SAM HYDE.🔴
1,394 watching -
 LIVE
LIVE
Right Side Broadcasting Network
5 hours agoLIVE: President Trump Signs a Presidential Memorandum - 9/15/25
2,641 watching -
 LIVE
LIVE
Sean Unpaved
2 hours agoTurf Tumbles & Triumphs: Burrow's Setback, Chiefs' Crumble, Irish Iced, & Kelly's 3-0
270 watching -
 34:27
34:27
The Quiet Part
4 hours ago $0.06 earnedCanada DIDN'T EVEN TRY!
711 -
 LIVE
LIVE
SportsPicks
4 hours agoCrick's Corner: Episode 80
97 watching -
 2:06:51
2:06:51
The Charlie Kirk Show
3 hours agoVice President JD Vance Remembers Charlie Kirk | Miller, Tucker, RFK Jr., Wiles, Leavitt | 9.15.25
1.28M1.12K -
 LIVE
LIVE
Major League Fishing
5 days agoLIVE! - Fishing Clash Team Series: Heritage Cup - Day 2
402 watching -
 1:08:54
1:08:54
Simply Bitcoin
3 hours ago $0.46 earnedNEW REPORT SUGGESTS THE BITCOIN SUPPLY SHOCK IS ACCELERATING?! | EP 1332
8.08K -
 10:31
10:31
Dr. Eric Berg
3 hours ago13 Foods You Should Never Buy Organic
56.7K19 -
 15:10
15:10
SB Mowing
1 month agoShe had TEARS OF JOY on her face - An update on Beth
44K34