Premium Only Content
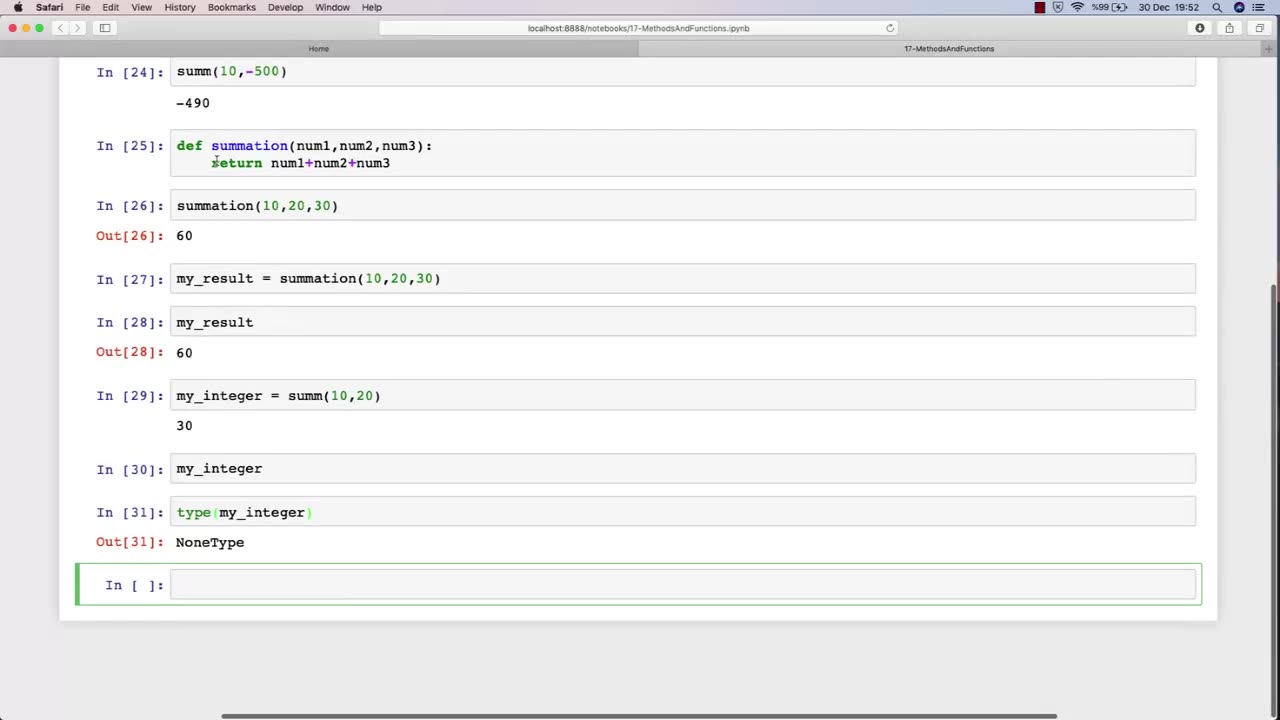
Chapter-30, LEC-3 | Functions Explained (lec-2) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
In Lecture 2 of an ethical hacking course, the function is to introduce students to the basic principles and concepts of ethical hacking. This lecture typically covers topics such as the difference between ethical hacking and illegal hacking, the various types of hackers, and the ethical and legal issues associated with ethical hacking.
The main objective of this lecture is to establish a foundational understanding of what ethical hacking is, why it is important, and the ethical and legal considerations that must be taken into account when conducting ethical hacking activities.
Students in this lecture learn about the various types of hackers, including black hat hackers, white hat hackers, and grey hat hackers. They learn about the motivations and characteristics of each type of hacker and how they differ in terms of their intentions and activities.
The lecture also covers the ethical considerations associated with ethical hacking, such as the importance of obtaining permission before conducting any testing, respecting the privacy of individuals and organizations, and adhering to ethical and professional standards.
Finally, the lecture covers the legal issues associated with ethical hacking, including the various laws and regulations governing cybersecurity and data protection, and the potential consequences of violating these laws.
Overall, the function of Lecture 2 in an ethical hacking course is to provide students with a broad understanding of the ethical and legal principles that underpin ethical hacking, and to ensure that they are equipped with the knowledge and skills necessary to conduct ethical hacking activities in a responsible and professional manner.
-
 4:09:13
4:09:13
I_Came_With_Fire_Podcast
19 hours agoLive Fire: Christmas Special
48.2K9 -
 46:26
46:26
Sarah Westall
12 hours agoWhat’s Behind the Silver Surge? Large Institutions Cashing In w/ Andy Schectman
47.8K3 -
 6:42:10
6:42:10
Turning Point USA
18 hours agoLIVE NOW: AMFEST DAY 2 - VIVEK, JACK POSOBIEC, MEGYN KELLY, ALEX CLARK AND MORE…
1.32M189 -
 1:14:37
1:14:37
Flyover Conservatives
1 day agoHow to Win 2026 Before It Starts — Clay Clark’s Goal-Setting Blueprint | FOC Show
48.2K1 -
 12:52
12:52
The Kevin Trudeau Show Limitless
2 days agoBeyond Good And Bad: The Hidden Reality Code
95.6K22 -
 1:03:11
1:03:11
BonginoReport
14 hours agoBrown U Security Failures EXPOSED - Nightly Scroll w/ Hayley Caronia (Ep.201)
168K49 -
 51:09
51:09
Patriots With Grit
9 hours agoWill A.I. Replace Doctors? | Dr. Stella Immanuel MD
31.6K6 -
 4:10:32
4:10:32
Nerdrotic
15 hours ago $18.19 earnedHollywood's DOOMSDAY! WB FIRESALE! - Friday Night Tights 385 w Zachary Levi
90K24 -
 12:25:53
12:25:53
LFA TV
1 day agoLIVE & BREAKING NEWS! | FRIDAY 12/19/25
208K32 -
 1:08:59
1:08:59
Edge of Wonder
12 hours agoNASA’s Intergalactic Spacecraft, Real Dwarves Spotted & Research Roundup
31.9K7