Premium Only Content
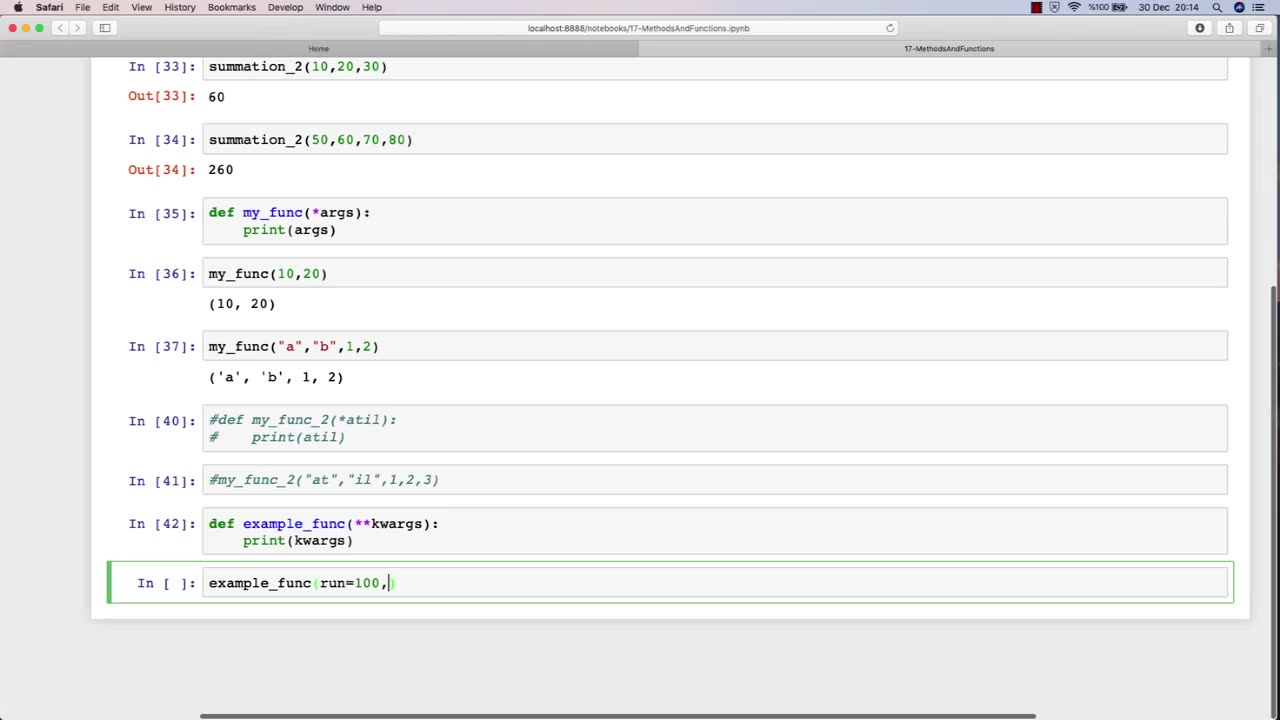
Chapter-30, LEC-4 | Functions Advanced | #rumble #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
The function of an advanced ethical hacking course is to provide experienced professionals with the latest knowledge, techniques, and tools in the field of cybersecurity. This course is designed for individuals who have already completed a basic ethical hacking course and are looking to enhance their skills and expertise in this rapidly evolving field.
The advanced ethical hacking course typically covers advanced topics such as exploit development, reverse engineering, cryptography, network forensics, and advanced penetration testing techniques. The course also provides students with in-depth knowledge of the latest cybersecurity threats and vulnerabilities, and how to defend against them.
One of the primary functions of an advanced ethical hacking course is to teach students how to develop and use custom exploits and tools to exploit vulnerabilities that may not be detected by commercial security tools. This requires a deep understanding of programming, scripting, and operating system internals.
In addition to technical skills, the advanced ethical hacking course also emphasizes the importance of soft skills, such as communication, documentation, and project management. Students learn how to effectively communicate their findings to technical and non-technical stakeholders, and how to manage complex ethical hacking projects from start to finish.
Overall, the function of an advanced ethical hacking course is to provide experienced professionals with the advanced knowledge and skills necessary to stay ahead of the curve in the constantly evolving field of cybersecurity. This course equips students with the tools and techniques needed to effectively identify and address the latest cybersecurity threats and vulnerabilities, and to help protect organizations from potentially devastating cyber attacks.
-
 2:59:40
2:59:40
Wendy Bell Radio
8 hours agoSo Many Smokescreens
61.2K90 -
 1:19:29
1:19:29
Sean Unpaved
5 hours agoCan Klint Kubiak SAVE The Las Vegas Raiders? | UNPAVED
29.2K -
 1:48:04
1:48:04
MattMorseTV
3 hours ago $20.96 earned🔴MASSIVE White House PRESS CONFERENCE.🔴
53.7K129 -
 2:30:41
2:30:41
Side Scrollers Podcast
4 hours agoSide Scrollers Podcast Live | Tuesday February 10th 2026
36.9K11 -
 1:59:04
1:59:04
Steven Crowder
6 hours agoThe Definitive Jeffrey Epstein Recap: Dissecting the Incoherent Narrative
484K231 -
 1:13:35
1:13:35
TheAlecLaceShow
3 hours agoTrump Epstein Narrative DESTROYED | Guests: Peter Schweizer & Jan Jekielek | The Alec Lace Show
16.5K6 -
 31:57
31:57
MYLUNCHBREAK CHANNEL PAGE
4 hours agoFinding Giants on an Island?
21.1K8 -
 1:42:16
1:42:16
The Dan Bongino Show
7 hours agoNo Dudes In Dresses (Ep. 2449) - 02/10/2026
674K709 -
 56:58
56:58
The Rubin Report
5 hours ago‘The View’s’ Sunny Hostin Didn’t Realize How Condescending She Sounded Lecturing Her Audience
70.9K46 -
 18:59
18:59
Scammer Payback
4 hours agoThe virus all scammers should fear
21.3K14