Premium Only Content
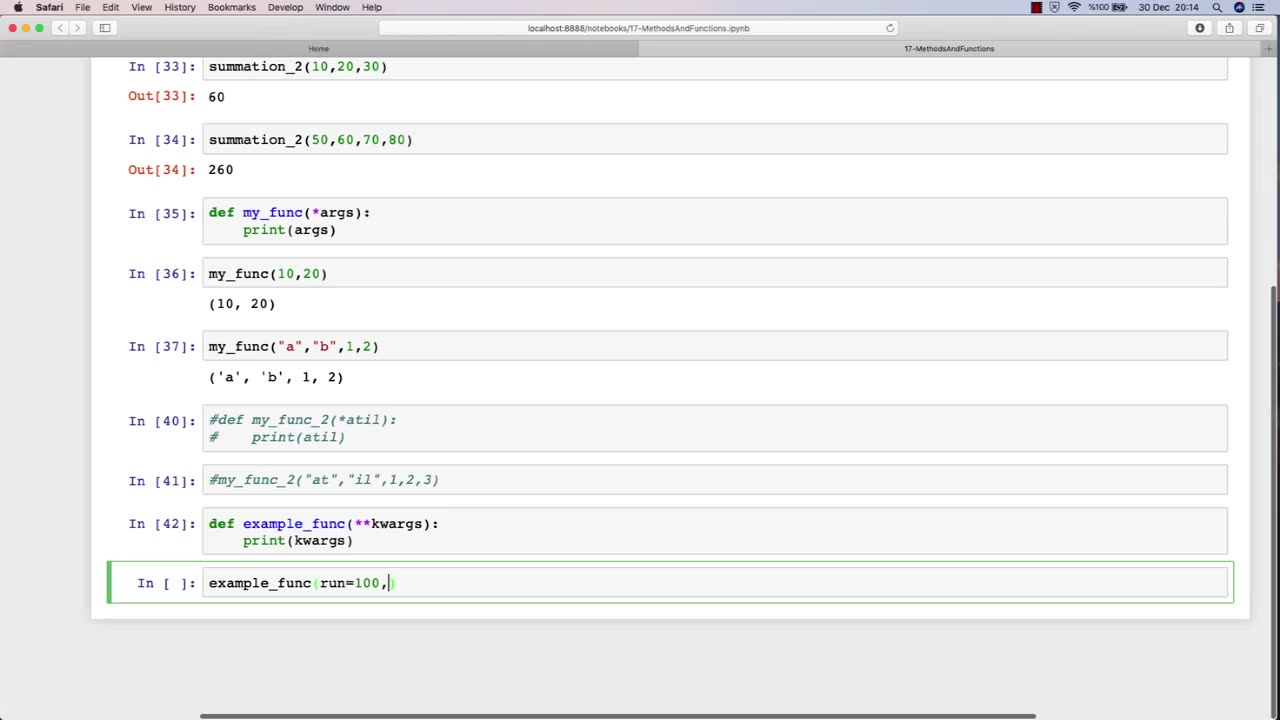
Chapter-30, LEC-4 | Functions Advanced | #rumble #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
The function of an advanced ethical hacking course is to provide experienced professionals with the latest knowledge, techniques, and tools in the field of cybersecurity. This course is designed for individuals who have already completed a basic ethical hacking course and are looking to enhance their skills and expertise in this rapidly evolving field.
The advanced ethical hacking course typically covers advanced topics such as exploit development, reverse engineering, cryptography, network forensics, and advanced penetration testing techniques. The course also provides students with in-depth knowledge of the latest cybersecurity threats and vulnerabilities, and how to defend against them.
One of the primary functions of an advanced ethical hacking course is to teach students how to develop and use custom exploits and tools to exploit vulnerabilities that may not be detected by commercial security tools. This requires a deep understanding of programming, scripting, and operating system internals.
In addition to technical skills, the advanced ethical hacking course also emphasizes the importance of soft skills, such as communication, documentation, and project management. Students learn how to effectively communicate their findings to technical and non-technical stakeholders, and how to manage complex ethical hacking projects from start to finish.
Overall, the function of an advanced ethical hacking course is to provide experienced professionals with the advanced knowledge and skills necessary to stay ahead of the curve in the constantly evolving field of cybersecurity. This course equips students with the tools and techniques needed to effectively identify and address the latest cybersecurity threats and vulnerabilities, and to help protect organizations from potentially devastating cyber attacks.
-
 1:04:43
1:04:43
Tucker Carlson
1 hour agoRay Dalio: How to Survive the Coming Civil War and Plot to Use Debt and CBDCs to Enslave You
38.9K38 -

Adam Does Movies
34 minutes agoThe The Mandalorian and Grogu Superbowl Spot Was Awful - Live Taping
-
 1:10:43
1:10:43
Sean Unpaved
2 hours agoSam Darnold Leads Seahawks To Super Bowl LX WIN vs. Patriots! | UNPAVED
4.76K -
 DVR
DVR
Nerdrotic
3 hours ago $1.87 earnedNerdrotic Nooner 559
47.7K1 -
 LIVE
LIVE
Rallied
1 hour ago $0.63 earnedWarzone Streaking with The Shotty Boys
81 watching -
 28:24
28:24
Neil McCoy-Ward
5 hours ago🚨 The Dollar Endgame Is Near... (Few Are Prepared For The New World Order) 🔥
3.14K4 -
 LIVE
LIVE
Daniel Davis Deep Dive
3 hours agoThere's No FORCING RUSSIA Into Anything /Lt Col Daniel Davis & Steve Jermy
106 watching -
 1:05:47
1:05:47
BonginoReport
4 hours agoOlympians ICE Out America on World Stage - Scrolling w/ Hayley (Ep. 231) - 02/09/26
154K67 -
 1:56:19
1:56:19
Steven Crowder
5 hours agoBad Bunny's Halftime Show Was Awful - But Not For the Reasons You Think
477K279 -
 3:17:36
3:17:36
iCkEdMeL
4 hours ago $2.70 earned🔴 BREAKING: Ransom Deadline Nears in Nancy Guthrie Case | Consent Search at Annie Guthrie’s Home
28.1K1