Premium Only Content
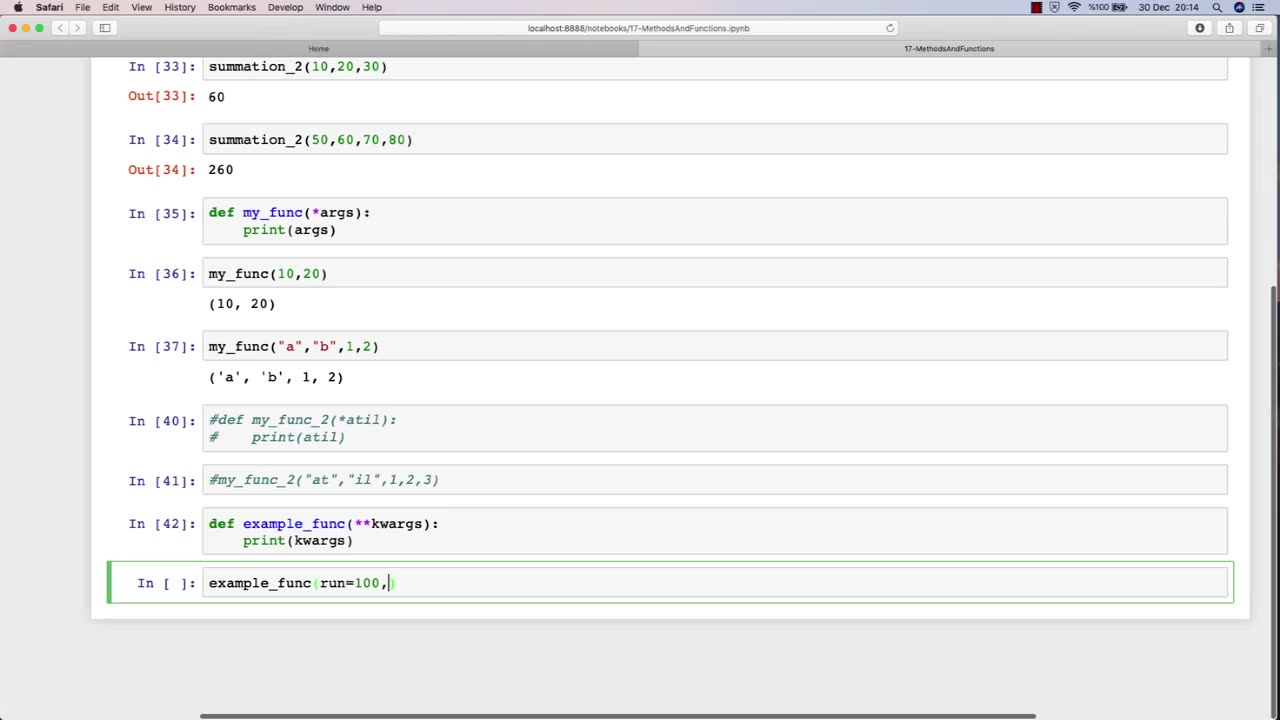
Chapter-30, LEC-4 | Functions Advanced | #rumble #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
The function of an advanced ethical hacking course is to provide experienced professionals with the latest knowledge, techniques, and tools in the field of cybersecurity. This course is designed for individuals who have already completed a basic ethical hacking course and are looking to enhance their skills and expertise in this rapidly evolving field.
The advanced ethical hacking course typically covers advanced topics such as exploit development, reverse engineering, cryptography, network forensics, and advanced penetration testing techniques. The course also provides students with in-depth knowledge of the latest cybersecurity threats and vulnerabilities, and how to defend against them.
One of the primary functions of an advanced ethical hacking course is to teach students how to develop and use custom exploits and tools to exploit vulnerabilities that may not be detected by commercial security tools. This requires a deep understanding of programming, scripting, and operating system internals.
In addition to technical skills, the advanced ethical hacking course also emphasizes the importance of soft skills, such as communication, documentation, and project management. Students learn how to effectively communicate their findings to technical and non-technical stakeholders, and how to manage complex ethical hacking projects from start to finish.
Overall, the function of an advanced ethical hacking course is to provide experienced professionals with the advanced knowledge and skills necessary to stay ahead of the curve in the constantly evolving field of cybersecurity. This course equips students with the tools and techniques needed to effectively identify and address the latest cybersecurity threats and vulnerabilities, and to help protect organizations from potentially devastating cyber attacks.
-
 10:24
10:24
Clyde Do Something
8 hours ago $0.02 earnedPresident Trump EXPOSES Carney’s Plan to Sell Canada to CHINA
5.52K2 -
 LIVE
LIVE
Flyover Conservatives
11 hours agoDR. BRYAN ARDIS | Newborn Babies. Monsanto. Transgenderism. What’s the Connection? You’re NOT Going to Believe it! | FOC Show
456 watching -
 25:42
25:42
Jasmin Laine
3 hours agoFox News Panel ROASTS Mark Carney Over China Deal—“Canada Is Detached From Reality”
6.19K14 -
 18:20
18:20
Connor Tomlinson
8 hours agoWas George Orwell an Ethnonationalist?
3.81K -
 1:03:58
1:03:58
Sarah Westall
3 hours agoEpstein Was the Front to Something Bigger | Cathy O’Brien
7.63K4 -
 LIVE
LIVE
SpartakusLIVE
4 hours agoGames w/ Rall || #1 Spartan and Dragon DYNAMIC Duo
318 watching -
 LIVE
LIVE
megimu32
2 hours agoON THE SUBJECT: 2000s Things That Don’t Exist Anymore 👽
86 watching -
 LIVE
LIVE
CHiLi's Dojo
1 hour agoTekken 8 | Fahk & Rank
40 watching -
![Cookies make everything better, so do you! 💙🍪 [ ART + CHILL + GAMES] !kofi !discord !cookie](https://1a-1791.com/video/fww1/56/s8/1/C/G/g/1/CGg1z.0kob-small-Cookies-make-everything-bet.jpg) LIVE
LIVE
KittenCog
1 hour agoCookies make everything better, so do you! 💙🍪 [ ART + CHILL + GAMES] !kofi !discord !cookie
59 watching -
 52:38
52:38
Donald Trump Jr.
8 hours agoLet’s Act to Save America, Interview with Sen Mike Lee | Triggered Ep.318
134K94