Premium Only Content
Chapter-30, LEC-4 | Functions Advanced | #rumble #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
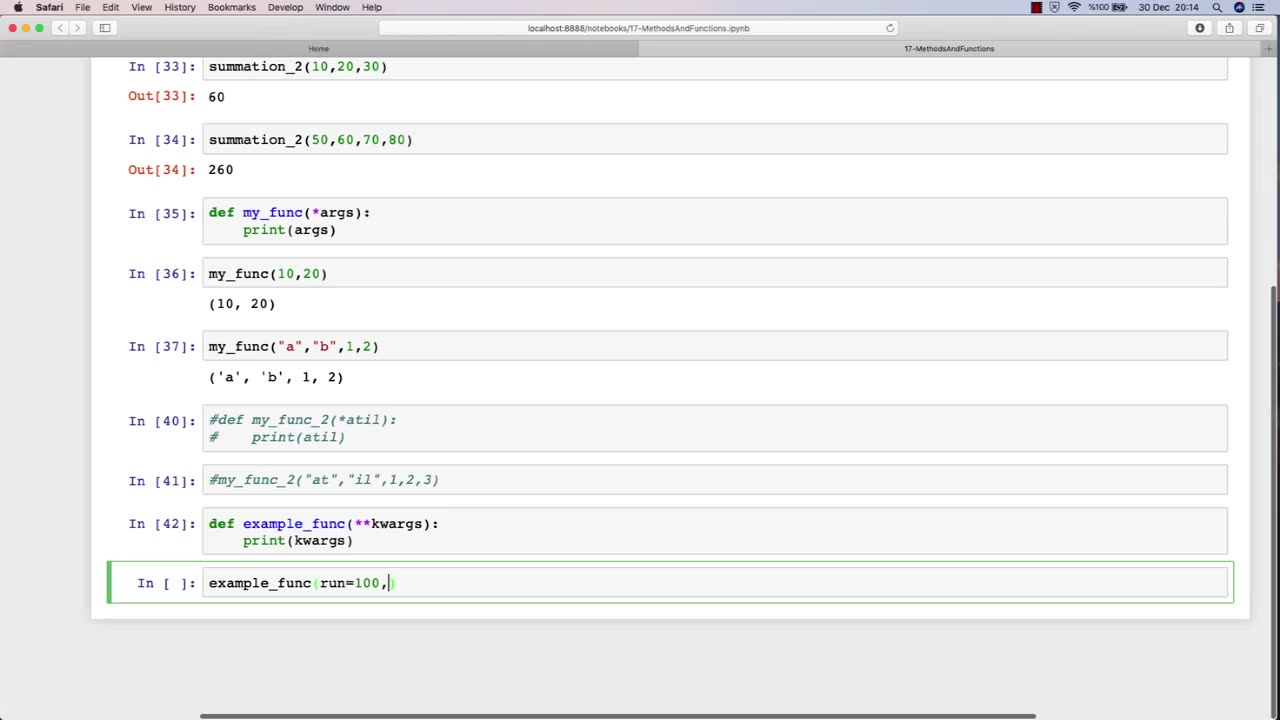
The function of an advanced ethical hacking course is to provide experienced professionals with the latest knowledge, techniques, and tools in the field of cybersecurity. This course is designed for individuals who have already completed a basic ethical hacking course and are looking to enhance their skills and expertise in this rapidly evolving field.
The advanced ethical hacking course typically covers advanced topics such as exploit development, reverse engineering, cryptography, network forensics, and advanced penetration testing techniques. The course also provides students with in-depth knowledge of the latest cybersecurity threats and vulnerabilities, and how to defend against them.
One of the primary functions of an advanced ethical hacking course is to teach students how to develop and use custom exploits and tools to exploit vulnerabilities that may not be detected by commercial security tools. This requires a deep understanding of programming, scripting, and operating system internals.
In addition to technical skills, the advanced ethical hacking course also emphasizes the importance of soft skills, such as communication, documentation, and project management. Students learn how to effectively communicate their findings to technical and non-technical stakeholders, and how to manage complex ethical hacking projects from start to finish.
Overall, the function of an advanced ethical hacking course is to provide experienced professionals with the advanced knowledge and skills necessary to stay ahead of the curve in the constantly evolving field of cybersecurity. This course equips students with the tools and techniques needed to effectively identify and address the latest cybersecurity threats and vulnerabilities, and to help protect organizations from potentially devastating cyber attacks.
-
 3:06:33
3:06:33
IsaiahLCarter
12 hours ago $9.40 earnedCharlie Kirk, American Martyr (with Mikale Olson) || APOSTATE RADIO 028
69.8K19 -
 16:43
16:43
Mrgunsngear
15 hours ago $10.18 earnedKimber 2K11 Pro Review 🇺🇸
50.4K14 -
 13:40
13:40
Michael Button
1 day ago $3.17 earnedThe Strangest Theory of Human Evolution
46.8K23 -
 10:19
10:19
Blackstone Griddles
1 day agoMahi-Mahi Fish Tacos on the Blackstone Griddle
32.6K3 -
 23:51
23:51
Jasmin Laine
1 day ago“Stop Wasting My Time!”—Trump's BRUTAL WARNING To Canada As Poilievre ROASTS CBC LIVE
24.8K29 -
 9:54
9:54
Millionaire Mentor
1 day agoNBC Host EXPOSES JB Pritzker For Saying This About Trump
16.2K14 -
 1:35:39
1:35:39
SB Mowing
2 days agoIt took the WHOLE NEIGHBORHOOD to uncover this yards SHOCKING SECRET
99.1K65 -
 12:52
12:52
ROSE UNPLUGGED
1 day agoFrom Vision to Legacy: Charlie Kirk
62.9K22 -
 1:14:22
1:14:22
Jeff Ahern
12 hours ago $12.56 earnedThe Sunday Show with Jeff Ahern
87.5K39 -
 16:37
16:37
Professor Nez
13 hours ago🚨Internet MELTS DOWN over JD Vance & Trump BREAKING the Democrats!
76.7K198