Premium Only Content
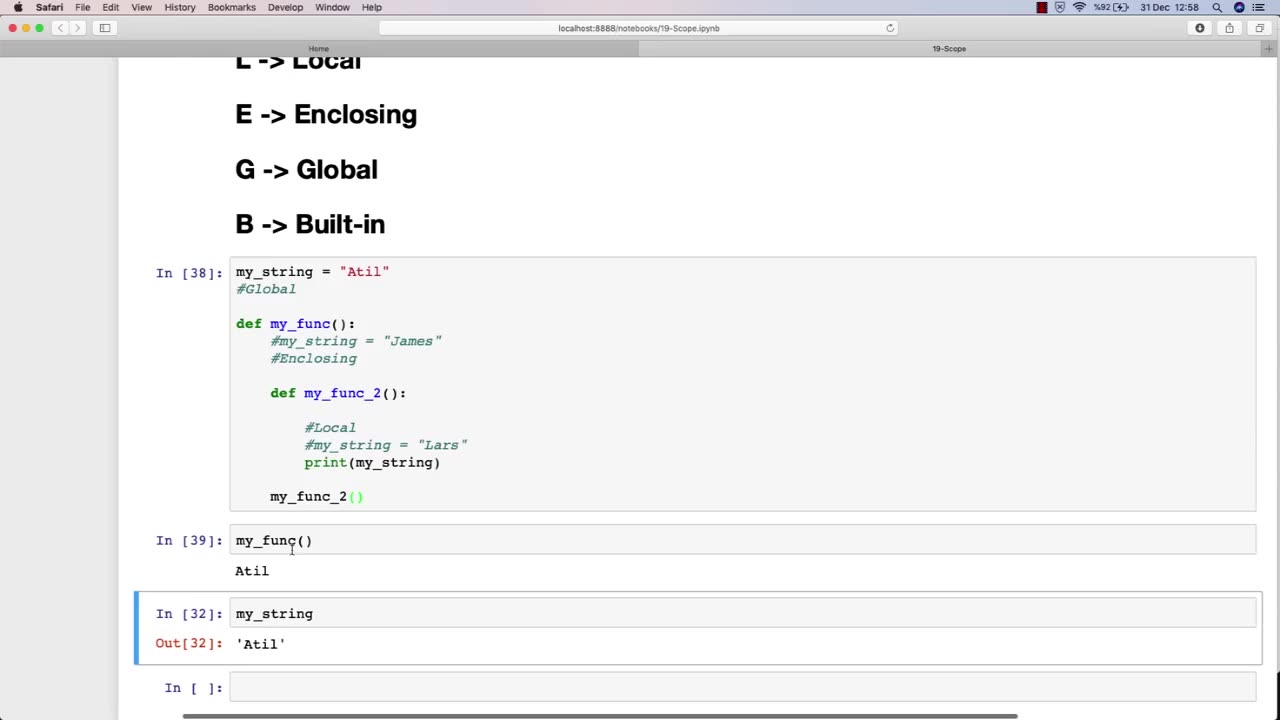
Chapter-30, LEC-6 | SCOPE | #ethicalhacking #education #hacking #rumble
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The scope of an ethical hacking course is vast and covers a wide range of topics related to cybersecurity and information security. At a high level, the scope of an ethical hacking course typically includes:
Understanding the fundamentals of cybersecurity: This includes understanding the various types of cybersecurity threats, such as viruses, malware, and phishing attacks, and the principles of risk management and threat modeling.
Network security: This includes understanding the fundamentals of network architecture and protocols, as well as how to secure networks against attacks such as denial-of-service (DoS) attacks and man-in-the-middle (MITM) attacks.
Web application security: This includes understanding the principles of web application architecture and how to secure web applications against common attacks such as cross-site scripting (XSS) and SQL injection.
Wireless security: This includes understanding the fundamentals of wireless networks and how to secure them against attacks such as rogue access points and eavesdropping.
Penetration testing: This includes understanding the principles of penetration testing and how to conduct effective ethical hacking activities, including reconnaissance, vulnerability assessment, and exploitation.
Ethical and legal considerations: This includes understanding the ethical and legal considerations associated with ethical hacking, such as obtaining permission and respecting privacy.
The scope of an ethical hacking course is constantly evolving to keep pace with the ever-changing cybersecurity landscape. As new threats emerge and new technologies are developed, the scope of an ethical hacking course must adapt to provide students with the latest knowledge and techniques in the field of cybersecurity.
-
 LIVE
LIVE
Jeff Ahern
1 hour agoThe Saturday Show with Jeff Ahern
832 watching -
 LIVE
LIVE
Spartan
1 hour agoFirst time playing Black Myth Wukong
56 watching -

iCkEdMeL
1 hour ago $5.19 earnedFrom Music to Murder? D4VD’s Tesla Horror Story
15.5K6 -
 LIVE
LIVE
TwinGatz
1 hour ago🔴LIVE - Strike Out Saturday | CS2 | Counter-Strike 2 | New Subs = Case Opening
23 watching -
 LIVE
LIVE
Simulation and Exploration
4 hours agoHow well does this play on a controller? Future console players check this out!
37 watching -
 LIVE
LIVE
MrR4ger
6 hours agoTHE THREE SPLOOGES (THE RECKONING) - ACTIVE MATTER w/ AKAGUMO & TONYGAMING
38 watching -
 1:25:04
1:25:04
Michael Franzese
4 hours agoJames Comey, Epstein Files Block, Tylenol | Michael Franzese Live
185K55 -
 1:24:44
1:24:44
Winston Marshall
9 hours agoThe Hamas Hoax That Fooled The West...
19.2K19 -
 LIVE
LIVE
Grant Cardone
4 hours agoReal Estate Live Training
156 watching -
 22:53
22:53
Jasmin Laine
1 day agoParliament ERUPTS After "WORST Decision EVER!"—Carney Left SPEECHLESS by SHOCKING Report
20K31