Premium Only Content
Chapter-30, LEC-6 | SCOPE | #ethicalhacking #education #hacking #rumble
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
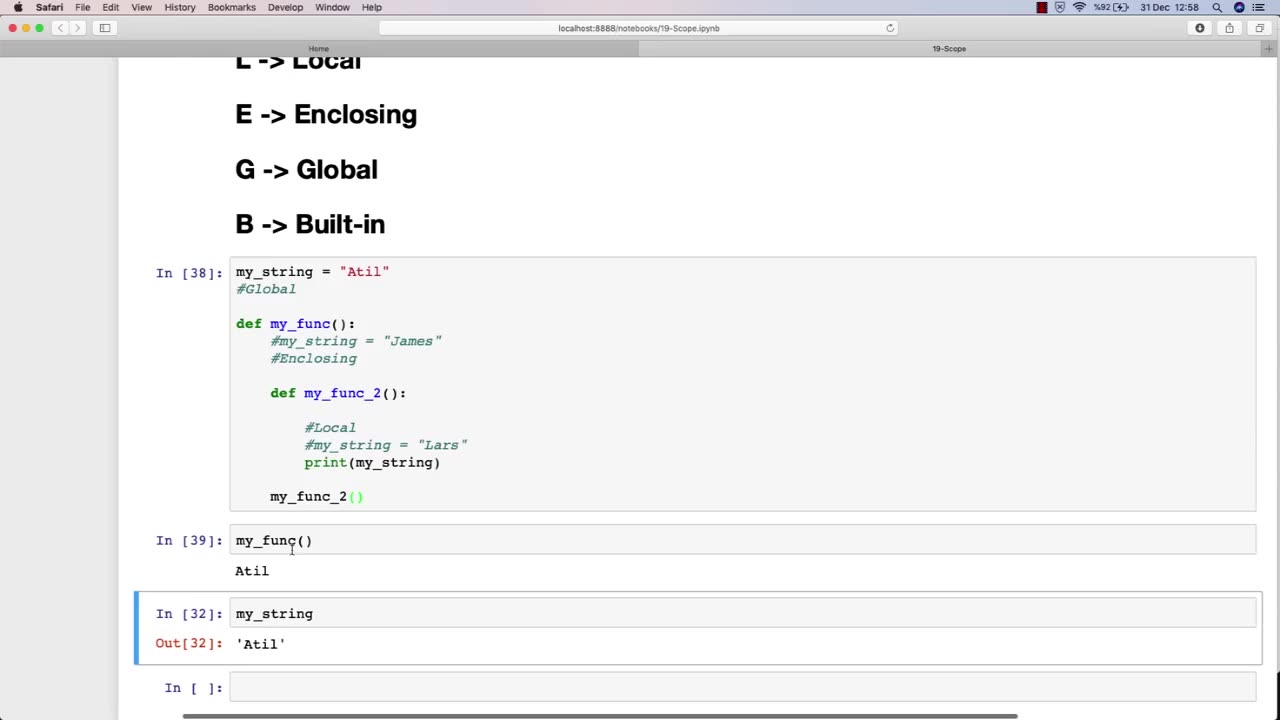
The scope of an ethical hacking course is vast and covers a wide range of topics related to cybersecurity and information security. At a high level, the scope of an ethical hacking course typically includes:
Understanding the fundamentals of cybersecurity: This includes understanding the various types of cybersecurity threats, such as viruses, malware, and phishing attacks, and the principles of risk management and threat modeling.
Network security: This includes understanding the fundamentals of network architecture and protocols, as well as how to secure networks against attacks such as denial-of-service (DoS) attacks and man-in-the-middle (MITM) attacks.
Web application security: This includes understanding the principles of web application architecture and how to secure web applications against common attacks such as cross-site scripting (XSS) and SQL injection.
Wireless security: This includes understanding the fundamentals of wireless networks and how to secure them against attacks such as rogue access points and eavesdropping.
Penetration testing: This includes understanding the principles of penetration testing and how to conduct effective ethical hacking activities, including reconnaissance, vulnerability assessment, and exploitation.
Ethical and legal considerations: This includes understanding the ethical and legal considerations associated with ethical hacking, such as obtaining permission and respecting privacy.
The scope of an ethical hacking course is constantly evolving to keep pace with the ever-changing cybersecurity landscape. As new threats emerge and new technologies are developed, the scope of an ethical hacking course must adapt to provide students with the latest knowledge and techniques in the field of cybersecurity.
-
 10:31
10:31
Dr. Eric Berg
1 hour ago13 Foods You Should Never Buy Organic
8.83K10 -
 15:10
15:10
SB Mowing
1 month agoShe had TEARS OF JOY on her face - An update on Beth
8.34K31 -
 LIVE
LIVE
Lofi Girl
3 years agolofi hip hop radio 📚 - beats to relax/study to
176 watching -
 LIVE
LIVE
Nikko Ortiz
1 hour agoLIVE - Trying Rumble Studio!
187 watching -
 9:30
9:30
Sugar Spun Run
5 hours agoBlack and White Cookies
31K1 -
 2:45
2:45
SLS - Street League Skateboarding
4 days agoManny Santiago's 'THIS IS 40' Part
18.3K2 -
 6:40
6:40
Homesteading Family
5 days agoNever Make Pie Crust From Scratch Again (Do THIS Instead)
14.2K2 -
 44:20
44:20
Melissa K Norris
3 days ago $0.30 earnedThe Most Overlooked Way to Preserve Food for Months (No Freezer Needed) w/ Sam Knapp
10K1 -
 23:00
23:00
Tony Jeffries
6 days agoThe Best & Worst Boxing Training Methods (Ranked by Olympic Boxer)
7.06K -
 44:44
44:44
Scammer Payback
17 days agoCrazy Confrontation with Hacked Scammer Group
34K20