Premium Only Content
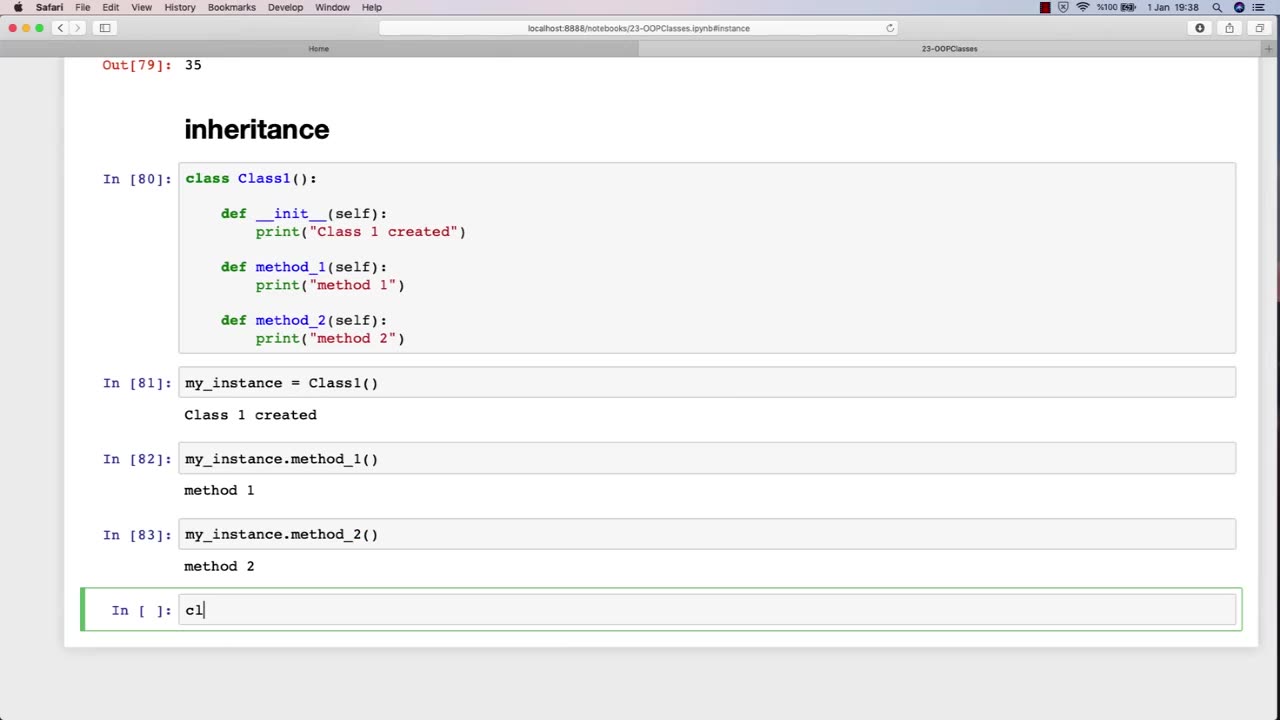
Chapter-31, LEC-5 | Inheritance | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Inheritance is an important concept in object-oriented programming, and it can also be relevant to an ethical hacking course. In the context of ethical hacking, inheritance can refer to the use of pre-existing code or tools to aid in the hacking process.
For example, ethical hackers may inherit code or tools from previous projects, open-source software, or online resources. This code or tools may help them automate tasks, test for vulnerabilities, or exploit known weaknesses. By inheriting code or tools, ethical hackers can save time and effort, while also benefiting from the knowledge and expertise of other developers.
However, it is important for ethical hackers to be aware of the potential risks and limitations of inheriting code or tools. Inherited code may contain bugs or vulnerabilities that could introduce new security risks, and inherited tools may not be well-suited to the specific context of the hacking project. Therefore, ethical hackers must exercise caution when using inherited code or tools, and should always verify their functionality and security before incorporating them into their own work.
Furthermore, ethical hackers must also consider the ethical implications of inheriting code or tools. They must ensure that the code or tools they use are legally obtained and do not infringe on intellectual property rights or other legal obligations. They must also be mindful of the potential impact of their actions, and ensure that they are using their skills and tools for ethical purposes.
In summary, inheritance is an important concept in ethical hacking, as it allows hackers to leverage pre-existing code or tools to aid in their work. However, ethical hackers must be aware of the potential risks and limitations of inherited code or tools, and must also consider the ethical implications of their actions.
-
 LIVE
LIVE
Steven Crowder
3 hours ago🔴 Deport Them All: Trump Takes Fight to Leftist Chicago & Portland Over Attacks on ICE
26,031 watching -
 1:01:46
1:01:46
The Rubin Report
1 hour agoBill Maher’s Crowd Stunned as Van Jones Gives a Brutal Message to Liberal Media
23.8K36 -
 LIVE
LIVE
Nerdrotic
2 hours agoHollywood Will EAT Itself | Amazon BENDS The Knee to 007 Fans - Nerdrotic Nooner 524
351 watching -
 LIVE
LIVE
The Shannon Joy Show
2 hours agoMoody’s: Recession Incoming! Economic Slowdown Crushing Americans while Trump builds a ballroom
206 watching -
 LIVE
LIVE
The Mel K Show
1 hour agoMORNINGS WITH MEL K -Armor of God: Humanity Must Choose their Destiny 10-6-25
683 watching -
 LIVE
LIVE
LFA TV
17 hours agoLIVE & BREAKING NEWS! | MONDAY 10/6/25
4,092 watching -
 LIVE
LIVE
Trumpet Daily
1 hour agoTrumpet Daily LIVE | October 6, 2025
306 watching -
 30:03
30:03
Tudor Dixon
2 hours agoRep. Tim Burchett on the Government Shutdown & Leadership Crisis | The Tudor Dixon Podcast
2.49K1 -
 DVR
DVR
Bannons War Room
7 months agoWarRoom Live
39.5M9.13K -
 1:01:24
1:01:24
VINCE
3 hours agoDomestic Terrorism Is Spreading, And Fast | Episode 140 - 10/06/25
165K156
