Premium Only Content
Chapter-31, LEC-5 | Inheritance | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
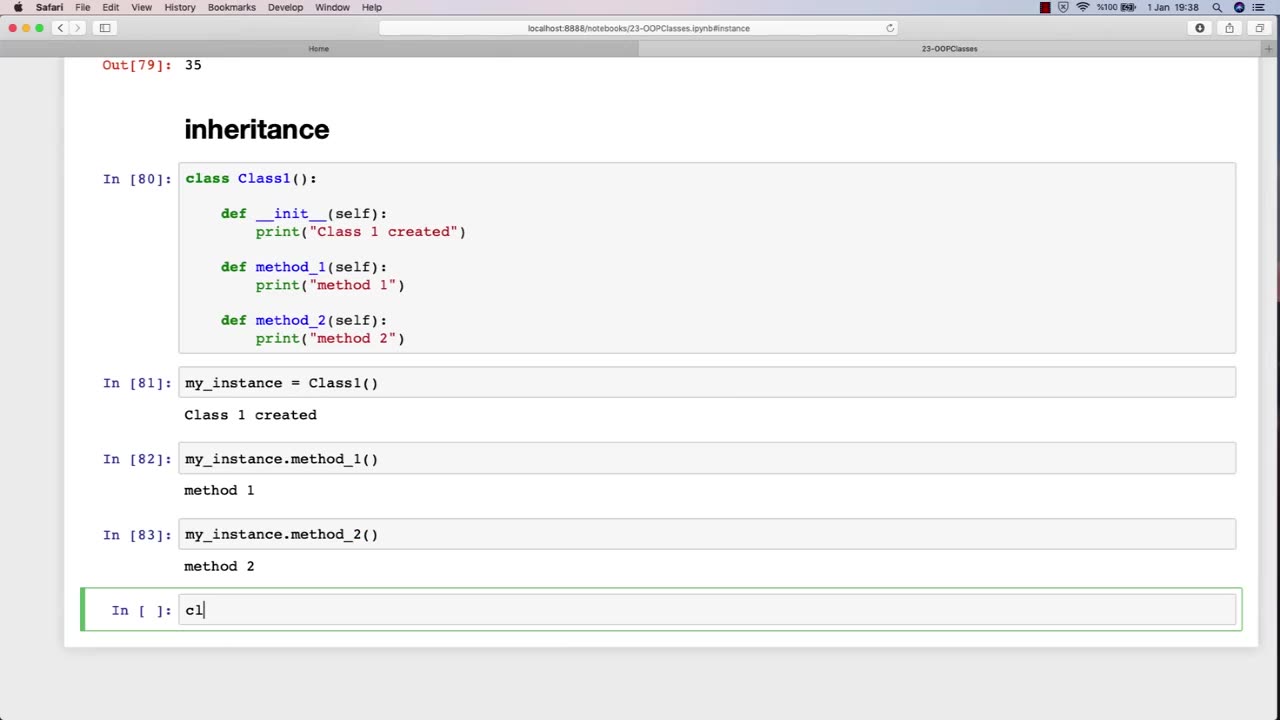
Inheritance is an important concept in object-oriented programming, and it can also be relevant to an ethical hacking course. In the context of ethical hacking, inheritance can refer to the use of pre-existing code or tools to aid in the hacking process.
For example, ethical hackers may inherit code or tools from previous projects, open-source software, or online resources. This code or tools may help them automate tasks, test for vulnerabilities, or exploit known weaknesses. By inheriting code or tools, ethical hackers can save time and effort, while also benefiting from the knowledge and expertise of other developers.
However, it is important for ethical hackers to be aware of the potential risks and limitations of inheriting code or tools. Inherited code may contain bugs or vulnerabilities that could introduce new security risks, and inherited tools may not be well-suited to the specific context of the hacking project. Therefore, ethical hackers must exercise caution when using inherited code or tools, and should always verify their functionality and security before incorporating them into their own work.
Furthermore, ethical hackers must also consider the ethical implications of inheriting code or tools. They must ensure that the code or tools they use are legally obtained and do not infringe on intellectual property rights or other legal obligations. They must also be mindful of the potential impact of their actions, and ensure that they are using their skills and tools for ethical purposes.
In summary, inheritance is an important concept in ethical hacking, as it allows hackers to leverage pre-existing code or tools to aid in their work. However, ethical hackers must be aware of the potential risks and limitations of inherited code or tools, and must also consider the ethical implications of their actions.
-

iCkEdMeL
1 hour ago $5.19 earnedFrom Music to Murder? D4VD’s Tesla Horror Story
15.5K4 -
 LIVE
LIVE
TwinGatz
1 hour ago🔴LIVE - Strike Out Saturday | CS2 | Counter-Strike 2 | New Subs = Case Opening
23 watching -
 LIVE
LIVE
Simulation and Exploration
4 hours agoHow well does this play on a controller? Future console players check this out!
41 watching -
 LIVE
LIVE
MrR4ger
6 hours agoTHE THREE SPLOOGES (THE RECKONING) - ACTIVE MATTER w/ AKAGUMO & TONYGAMING
38 watching -
 1:25:04
1:25:04
Michael Franzese
4 hours agoJames Comey, Epstein Files Block, Tylenol | Michael Franzese Live
185K54 -
 1:24:44
1:24:44
Winston Marshall
9 hours agoThe Hamas Hoax That Fooled The West...
19.2K19 -
 LIVE
LIVE
Grant Cardone
4 hours agoReal Estate Live Training
157 watching -
 22:53
22:53
Jasmin Laine
1 day agoParliament ERUPTS After "WORST Decision EVER!"—Carney Left SPEECHLESS by SHOCKING Report
20K31 -
 11:50
11:50
Mrgunsngear
1 day ago $5.89 earnedSteiner MPS Enclosed Red Dot: Better Than The ACRO P2? 🔴
20.7K14 -
 1:27:55
1:27:55
Sarah Westall
20 hours agoSelecting World Leaders: Intelligence No Longer a Prerequisite w/ Martin Armstrong
28.3K9