Premium Only Content
Chapter-31, LEC-5 | Inheritance | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
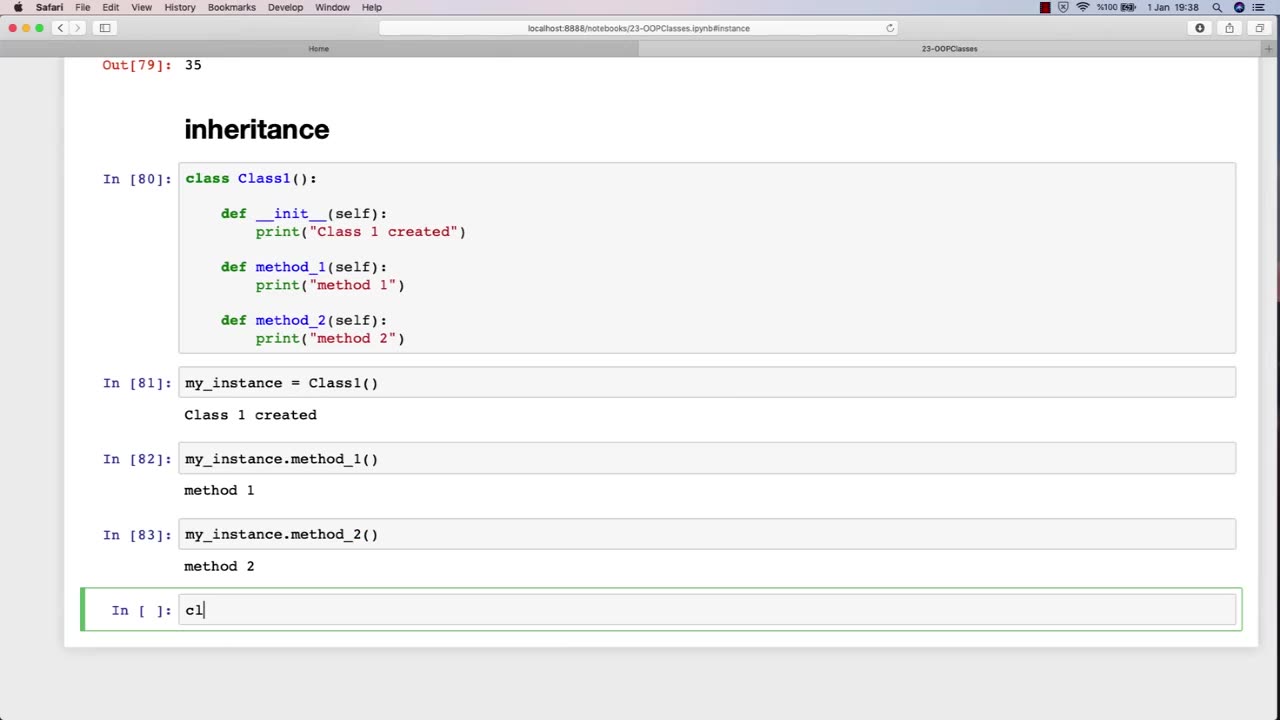
Inheritance is an important concept in object-oriented programming, and it can also be relevant to an ethical hacking course. In the context of ethical hacking, inheritance can refer to the use of pre-existing code or tools to aid in the hacking process.
For example, ethical hackers may inherit code or tools from previous projects, open-source software, or online resources. This code or tools may help them automate tasks, test for vulnerabilities, or exploit known weaknesses. By inheriting code or tools, ethical hackers can save time and effort, while also benefiting from the knowledge and expertise of other developers.
However, it is important for ethical hackers to be aware of the potential risks and limitations of inheriting code or tools. Inherited code may contain bugs or vulnerabilities that could introduce new security risks, and inherited tools may not be well-suited to the specific context of the hacking project. Therefore, ethical hackers must exercise caution when using inherited code or tools, and should always verify their functionality and security before incorporating them into their own work.
Furthermore, ethical hackers must also consider the ethical implications of inheriting code or tools. They must ensure that the code or tools they use are legally obtained and do not infringe on intellectual property rights or other legal obligations. They must also be mindful of the potential impact of their actions, and ensure that they are using their skills and tools for ethical purposes.
In summary, inheritance is an important concept in ethical hacking, as it allows hackers to leverage pre-existing code or tools to aid in their work. However, ethical hackers must be aware of the potential risks and limitations of inherited code or tools, and must also consider the ethical implications of their actions.
-
 1:01:26
1:01:26
VINCE
3 hours agoA Turning Point In The Culture | Episode 125 - 09/15/25
181K239 -
 1:40:09
1:40:09
Dear America
3 hours agoBREAKING NEWS UPDATE! Dark Truth EXPOSED: Charlie Kirk's Assassin & the Trans Agenda-This Is WAR!
129K126 -
 LIVE
LIVE
Badlands Media
10 hours agoBadlands Daily: September 15, 2025
4,681 watching -
 LIVE
LIVE
The Big Mig™
2 hours agoUncaged Host w/ Controversial Patriot Ret. MLB Closer John Rocker
4,615 watching -
 LIVE
LIVE
Caleb Hammer
1 hour agoHe Needs To Divorce Her | Financial Audit
149 watching -
 LIVE
LIVE
Chad Prather
1 hour agoCharlie Kirk’s Impact Felt WORLDWIDE, Even At Coldplay Concert + Pastors SPEAK UP Across America!
613 watching -
 LIVE
LIVE
Wendy Bell Radio
6 hours agoWe Are Charlie.
8,107 watching -
 2:01:01
2:01:01
Matt Kohrs
12 hours agoTesla Stock Is SQUEEZING (Market Open Analysis) || Live Trading
40.6K5 -
 40:43
40:43
Randi Hipper
2 hours agoBIG WEEK FOR BITCOIN! LATEST PRICE UPDATE
33.5K -
 1:26:16
1:26:16
JULIE GREEN MINISTRIES
5 hours agoLIVE WITH JULIE
140K297