Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
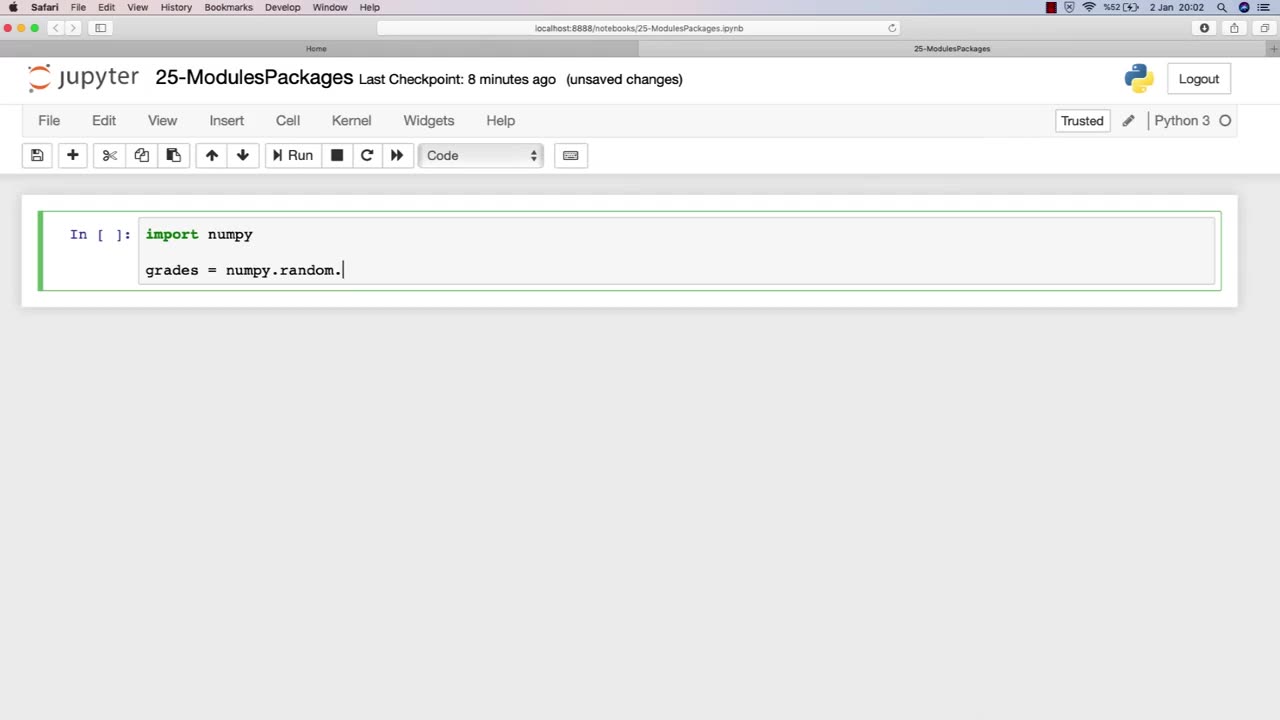
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 2:07:44
2:07:44
TimcastIRL
10 hours agoTrump's Secret Plan To Make Charlie Kirk VP, America Fest IN CIVIL WAR | Timcast IRL
228K211 -
 4:09:13
4:09:13
I_Came_With_Fire_Podcast
19 hours agoLive Fire: Christmas Special
48.2K9 -
 46:26
46:26
Sarah Westall
12 hours agoWhat’s Behind the Silver Surge? Large Institutions Cashing In w/ Andy Schectman
47.8K3 -
 6:42:10
6:42:10
Turning Point USA
18 hours agoLIVE NOW: AMFEST DAY 2 - VIVEK, JACK POSOBIEC, MEGYN KELLY, ALEX CLARK AND MORE…
1.32M189 -
 1:14:37
1:14:37
Flyover Conservatives
1 day agoHow to Win 2026 Before It Starts — Clay Clark’s Goal-Setting Blueprint | FOC Show
52.2K1 -
 12:52
12:52
The Kevin Trudeau Show Limitless
2 days agoBeyond Good And Bad: The Hidden Reality Code
95.6K22 -
 1:03:11
1:03:11
BonginoReport
14 hours agoBrown U Security Failures EXPOSED - Nightly Scroll w/ Hayley Caronia (Ep.201)
168K49 -
 51:09
51:09
Patriots With Grit
9 hours agoWill A.I. Replace Doctors? | Dr. Stella Immanuel MD
31.6K6 -
 4:10:32
4:10:32
Nerdrotic
15 hours ago $18.19 earnedHollywood's DOOMSDAY! WB FIRESALE! - Friday Night Tights 385 w Zachary Levi
90K24 -
 12:25:53
12:25:53
LFA TV
1 day agoLIVE & BREAKING NEWS! | FRIDAY 12/19/25
208K32