Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
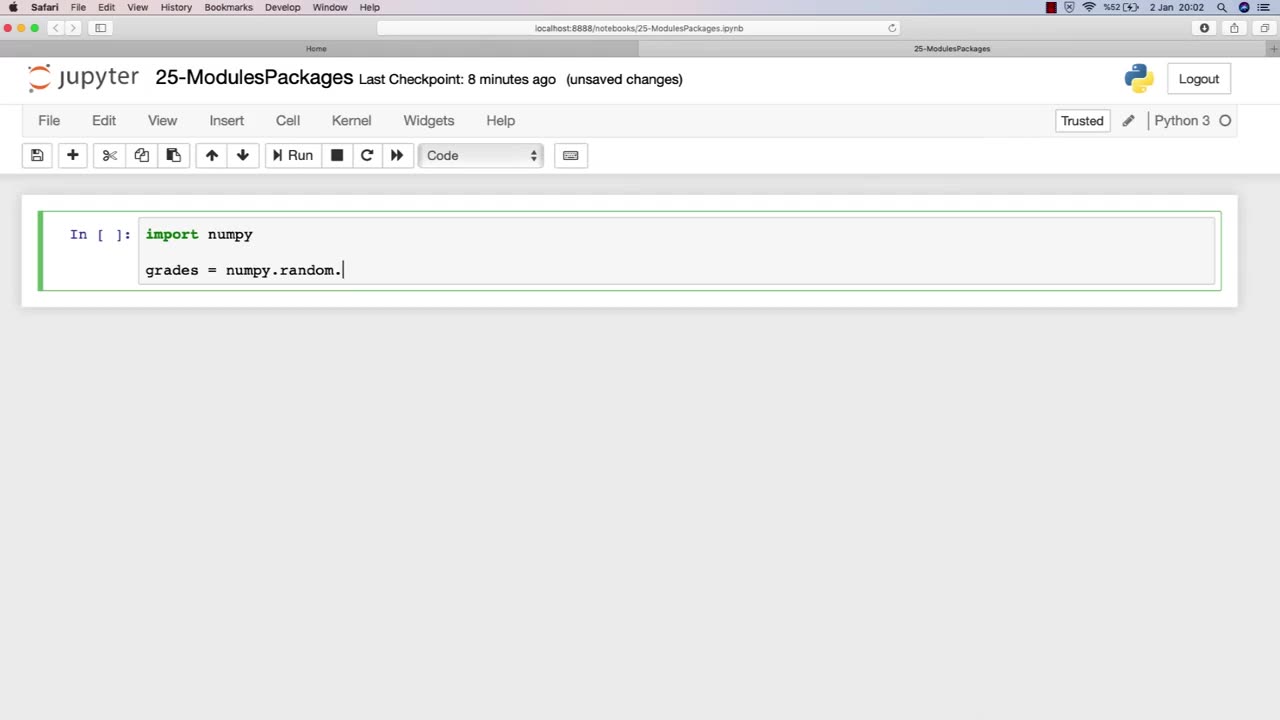
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 LIVE
LIVE
Nerdrotic
2 hours agoHollywood Will EAT Itself | Amazon BENDS The Knee to 007 Fans - Nerdrotic Nooner 524
348 watching -
 LIVE
LIVE
The Shannon Joy Show
2 hours agoMoody’s: Recession Incoming! Economic Slowdown Crushing Americans while Trump builds a ballroom
206 watching -
 LIVE
LIVE
The Mel K Show
1 hour agoMORNINGS WITH MEL K -Armor of God: Humanity Must Choose their Destiny 10-6-25
682 watching -
 LIVE
LIVE
LFA TV
17 hours agoLIVE & BREAKING NEWS! | MONDAY 10/6/25
4,095 watching -
 LIVE
LIVE
Trumpet Daily
1 hour agoTrumpet Daily LIVE | October 6, 2025
308 watching -
 30:03
30:03
Tudor Dixon
2 hours agoRep. Tim Burchett on the Government Shutdown & Leadership Crisis | The Tudor Dixon Podcast
2.49K1 -
 DVR
DVR
Bannons War Room
7 months agoWarRoom Live
39.5M9.13K -
 1:01:24
1:01:24
VINCE
3 hours agoDomestic Terrorism Is Spreading, And Fast | Episode 140 - 10/06/25
165K156 -
 40:58
40:58
Clownfish TV
6 hours agoHollywood is BROKE and JOBLESS?! Animation Most Affected! | Clownfish TV
19.3K9 -
 2:02:27
2:02:27
Benny Johnson
2 hours agoTrump Deploys National Guard to Chicago as Democrat Leader Caught CALLING For Murder of Republicans
55.9K43
