Premium Only Content
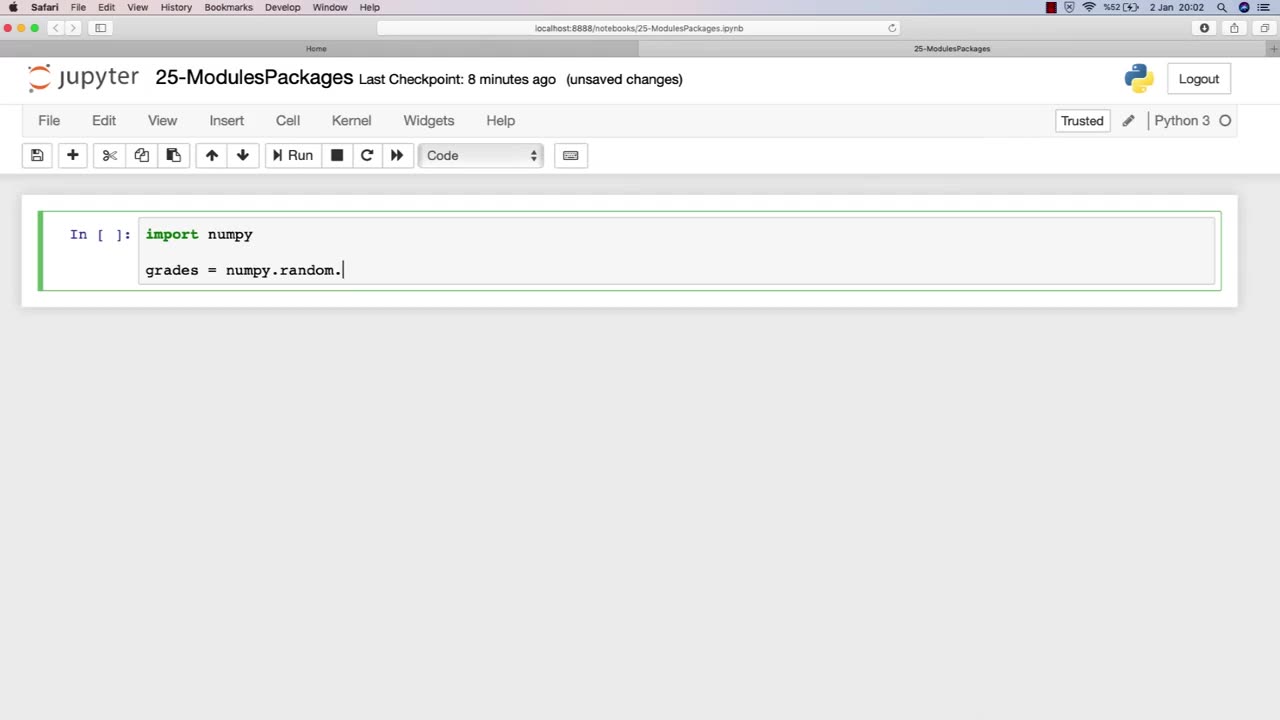
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 13:31
13:31
Clintonjaws
5 hours ago $0.31 earnedPiers Morgan CALLS OUT Andrew Wilson For Humiliating Him On Joe Rogan
5.09K5 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 247: Is American Pride Becoming a Thing of the PAST??
658 watching -
 LIVE
LIVE
The Tom Renz Show
1 hour agoHow Can You MAGA If You Won’t Stand For MAHA & Prosecute Child Rapists?
105 watching -
![[Ep 842] Super Bowl for Today’s Culture | Walz Resign! | Hate America? Leave!!](https://1a-1791.com/video/fwe2/d6/s8/1/G/Y/d/Y/GYdYz.0kob-small-Ep-842-Super-Bowl-for-Today.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 842] Super Bowl for Today’s Culture | Walz Resign! | Hate America? Leave!!
160 watching -
 1:37:00
1:37:00
The Quartering
2 hours agoSUPER BOWL MELTDOWN FROM BOTH SIDES, SUPER BOWL ADS PUSH ANTI-WHITE & DYSTOPIAN CAMERAS & MORE
126K40 -
 LIVE
LIVE
TheCrucible
2 hours agoPapa Gut vs Andrew Wilson: Hater Debate!
1,518 watching -
 18:02
18:02
cybersecuritygirl
11 days agoHow a 'Vibe Check' Stopped a Major Cyber Scam: Andy Piazza | Cyber Confessions
6.76K1 -
 1:12:01
1:12:01
HotZone
5 days ago $1.01 earnedBREAKING: Regime Troops Enter Rojava – Kurds Face Takeover
17.7K3 -
 1:02:23
1:02:23
DeVory Darkins
3 hours agoSuperbowl Halftime sparks MELTDOWN as Trump celebrates MAJOR Economic Update
126K55 -
 1:04:43
1:04:43
Tucker Carlson
3 hours agoRay Dalio: How to Survive the Coming Civil War and Plot to Use Debt and CBDCs to Enslave You
79.4K69