Premium Only Content
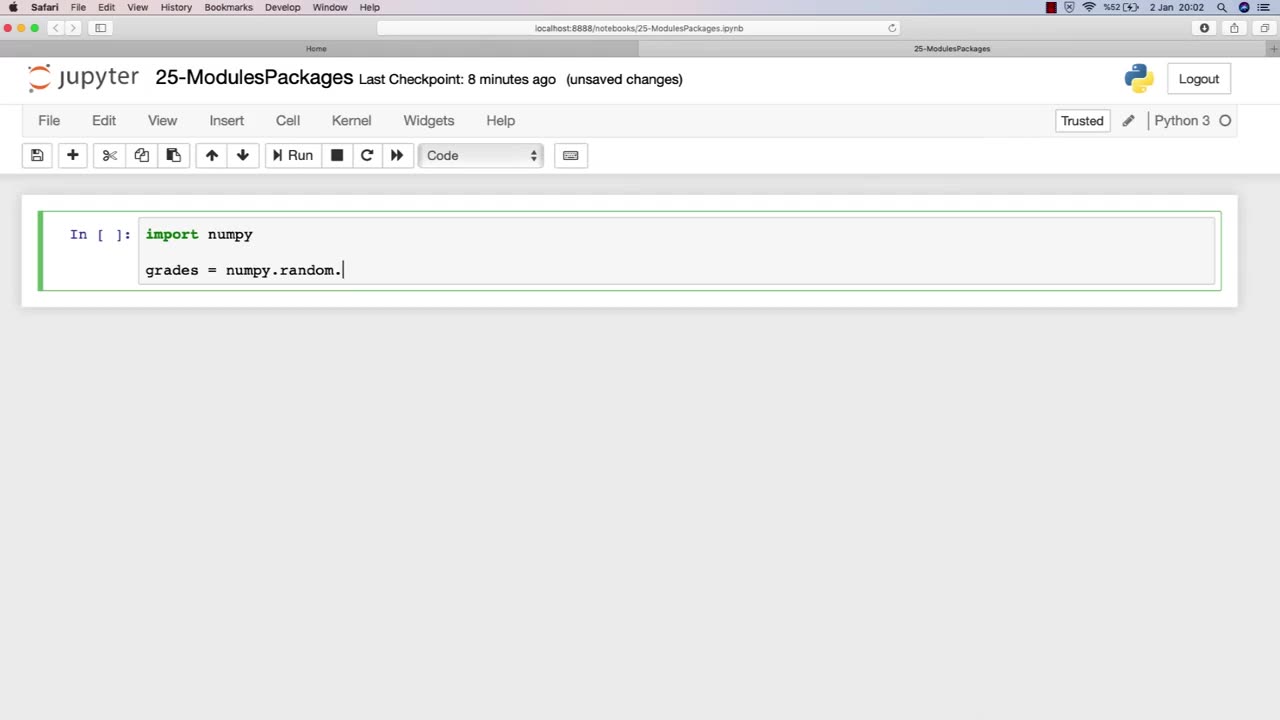
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 1:31:09
1:31:09
Amy Dangerfield
3 hours ago $0.02 earnedJames Fishback at Seed to Table Naples Florida @jamesfishback
4.1K1 -
 UPCOMING
UPCOMING
DLDAfterDark
2 hours agoHoffman Tactical Vs. RareGreed Triggers - Whoa - Forced Reset Saga Cont. Feat. NightStryke
1.56K1 -
 10:24
10:24
Clyde Do Something
8 hours ago $0.02 earnedPresident Trump EXPOSES Carney’s Plan to Sell Canada to CHINA
5.52K2 -
 LIVE
LIVE
Flyover Conservatives
11 hours agoDR. BRYAN ARDIS | Newborn Babies. Monsanto. Transgenderism. What’s the Connection? You’re NOT Going to Believe it! | FOC Show
454 watching -
 25:42
25:42
Jasmin Laine
3 hours agoFox News Panel ROASTS Mark Carney Over China Deal—“Canada Is Detached From Reality”
6.19K14 -
 18:20
18:20
Connor Tomlinson
8 hours agoWas George Orwell an Ethnonationalist?
3.81K -
 1:03:58
1:03:58
Sarah Westall
3 hours agoEpstein Was the Front to Something Bigger | Cathy O’Brien
7.63K4 -
 LIVE
LIVE
SpartakusLIVE
4 hours agoGames w/ Rall || #1 Spartan and Dragon DYNAMIC Duo
317 watching -
 LIVE
LIVE
megimu32
2 hours agoON THE SUBJECT: 2000s Things That Don’t Exist Anymore 👽
83 watching -
 LIVE
LIVE
CHiLi's Dojo
1 hour agoTekken 8 | Fahk & Rank
40 watching