Premium Only Content
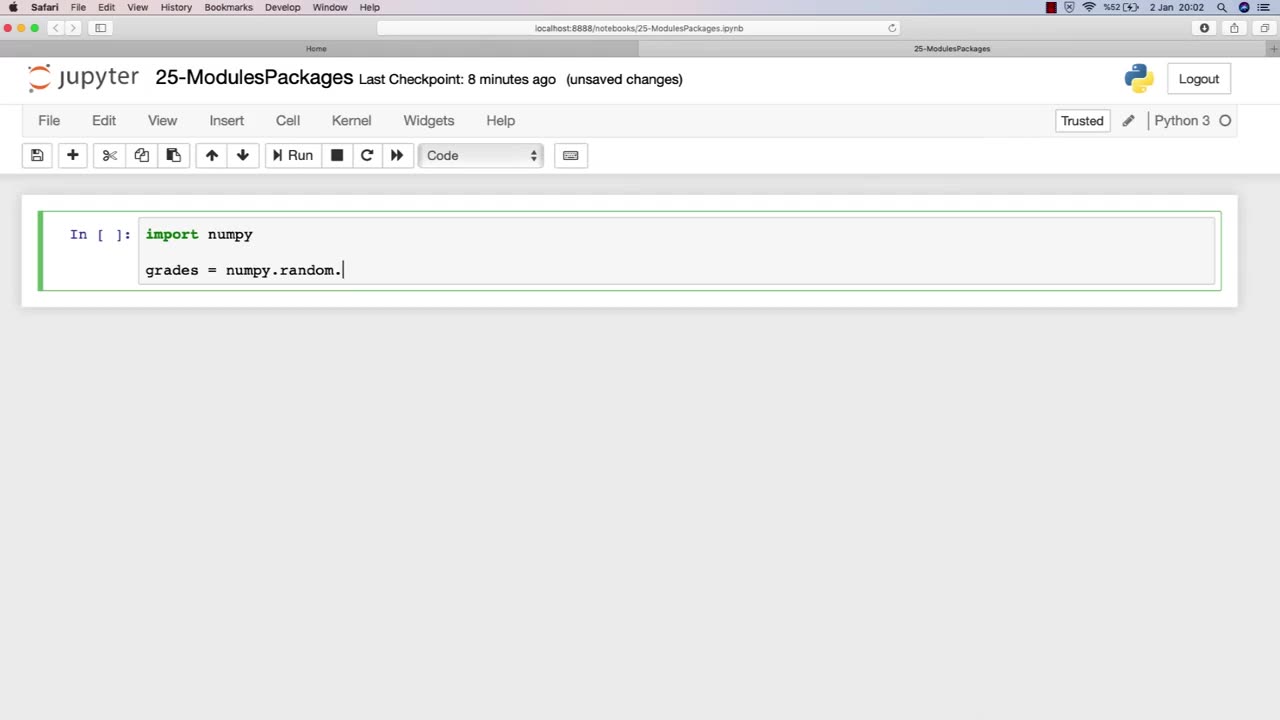
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 1:05:07
1:05:07
Timcast
1 hour agoTrump Orders DOJ Bondi To Prosecute Democrats In Public Statement
42.2K43 -
 2:15:20
2:15:20
Steven Crowder
4 hours ago🔴 Charlie Kirk Conspiracies Spread Like Wildfire: What's Really Going On?
341K496 -
 LIVE
LIVE
Nerdrotic
5 hours agoStar Wars: Mandalorian and Grogu Trailer Reaction - Nerdrotic Nooner 518
482 watching -
 LIVE
LIVE
Rebel News
51 minutes agoOstrich cull imminent, Rebel on the ground | Rebel Roundup
613 watching -
 1:04:57
1:04:57
The Rubin Report
2 hours agoCrowd Stunned by Trump’s Brutally Honest Remark at Charlie Kirk’s Funeral
45.4K33 -
 1:00:19
1:00:19
Grant Stinchfield
2 hours agoThe Exploitation of Charlie Kirk's Death is Very Real
2.81K11 -
 1:40:13
1:40:13
Nikko Ortiz
3 hours agoJapan's Prison System Is CRAZY...
17.5K2 -
 LIVE
LIVE
The Mel K Show
2 hours agoMORNINGS WITH MEL K Globalist Descend on America: Is it Time to Pull the Plug? 9-22-25
728 watching -
 LIVE
LIVE
The Shannon Joy Show
2 hours agoEpstein Cover Up - Kash Patel Has Names Of Epstein’s Pedophiles. Live Exclusive With Nick Bryant!
382 watching -
 LIVE
LIVE
LFA TV
17 hours agoLFA TV ALL DAY STREAM ! | MONDAY 9/22/25
4,008 watching