Premium Only Content
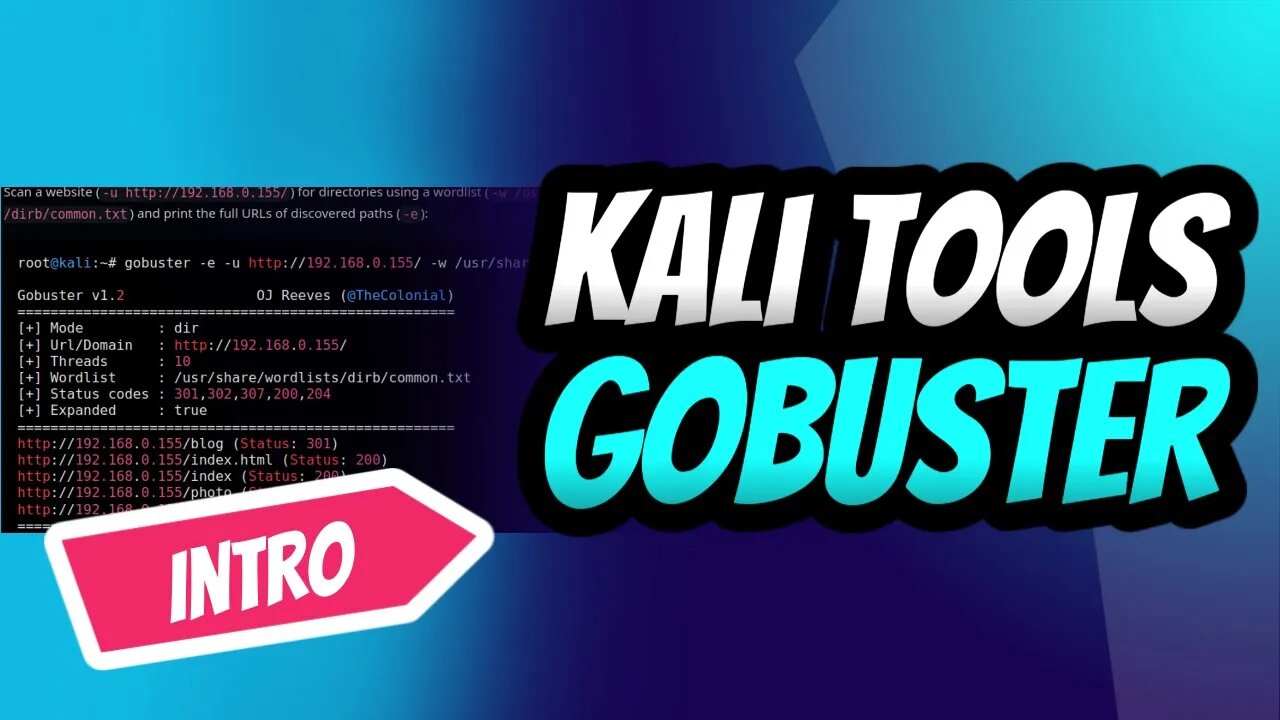
GoBuster for Ultimate Kali Linux Reconnaissance
Introduction into the power of GoBuster, the ultimate directory brute-forcing tool on Kali Linux! 🚀🔥 Learn how to reveal hidden directories and files, crack passwords, and uncover vulnerabilities with ease. Follow our step-by-step guide to mastering GoBuster and supercharge your ethical hacking skills.👩💻👨💻
Don't miss out on this essential intro for every aspiring hacker and penetration tester. Subscribe now, and let's get our hands dirty with GoBuster! 💪🔓
#KaliLinux #GoBuster #EthicalHacking #PenTesting #CyberSecurity #Reconnaissance #InfoSec #HiddenDirectories #BruteForce 💻🌐🔧🔒🕵️♀️🕵️♂️
Stay tuned for an upcoming detailed tutorial that will transform you into a GoBuster pro in no time! 🌟🔧
Subscribe and hit the bell icon to make sure you don't miss this comprehensive guide, and unlock your full potential as an ethical hacker and penetration tester. Let's explore the world of GoBuster together! 🌍🔓💡
If you look at the help command, we can see that Gobuster has a few modes.
dir — Directory enumeration mode.
dns — Subdomain enumeration mode.
fuzz — Fuzzing mode.
s3 — S3 enumeration mode.
v host — V host enumeration mode.
Gobuster is a fast brute-force tool to discover hidden URLs, files, and directories within websites. This will help us to remove/secure hidden files and sensitive data.
Gobuster also helps in securing sub-domains and virtual hosts from being exposed to the internet. Overall, Gobuster is a fantastic tool to help you reduce your application’s attack surface.
You can use the following steps to prevent and stop brute-force attacks on your web application.
Audit yourself: Use Gobuster on your own applications and perform an audit. This will help you find the information that will be visible to the attackers.
Apply security policies: To prevent resources like S3 from being exposed on the internet, use AWS bucket policies to prevent unauthorized access.
Use bot protection solutions: Bot protection services like Cloudflare will stop any brute-force attacks making it incredibly difficult to attack your web application.
-
 1:43
1:43
Dev Null - | Hacking| CyberSecurity| Cybersecurity education
2 years agoSelecting a Laptop for Ethical Hacking Success
3081 -
 1:32:16
1:32:16
Uncommon Sense In Current Times
16 hours ago $0.02 earnedPolygyny Debate: The Biblical Case For and Against Plural Marriage | Uncommon Sense
3.94K -
 LIVE
LIVE
BEK TV
22 hours agoTrent Loos in the Morning - 12/17/2025
172 watching -
 23:42
23:42
Athlete & Artist Show
4 days ago $0.01 earnedWorld Junior Invites & Snubs, NHL Threatens To Pull Out Of Olympics
1.58K -
 57:22
57:22
Coin Stories with Natalie Brunell
15 hours agoWill 1 Bitcoin Be Generational Wealth? Whales Selling, Legacy Planning & Price Drivers
59.2K5 -
 3:04:49
3:04:49
Price of Reason
14 hours agoTrump wants Tim Walz to RESIGN! Welcome to Derry Finale! Song Sung Blue EARLY REVIEW! Lanterns WOKE?
275K22 -
 11:47
11:47
Liberty Hangout
1 day agoAnti-Trump Beta FARTS On Me Instead of Debating
61.7K86 -
 1:37:20
1:37:20
FreshandFit
10 hours agoShe’s Not Your Girl It’s Just Your Turn
71.1K11 -
 5:26:18
5:26:18
Akademiks
12 hours agoEbro has MELTDOWN after Drake tells him to *** SLOWLY! Radio Over? NLE vs Youngboy part 805?
51.5K1 -
 1:35:27
1:35:27
Inverted World Live
13 hours agoLost Satellites, Wild Horses, and 3i/Atlas
167K7