Premium Only Content
GoBuster for Ultimate Kali Linux Reconnaissance
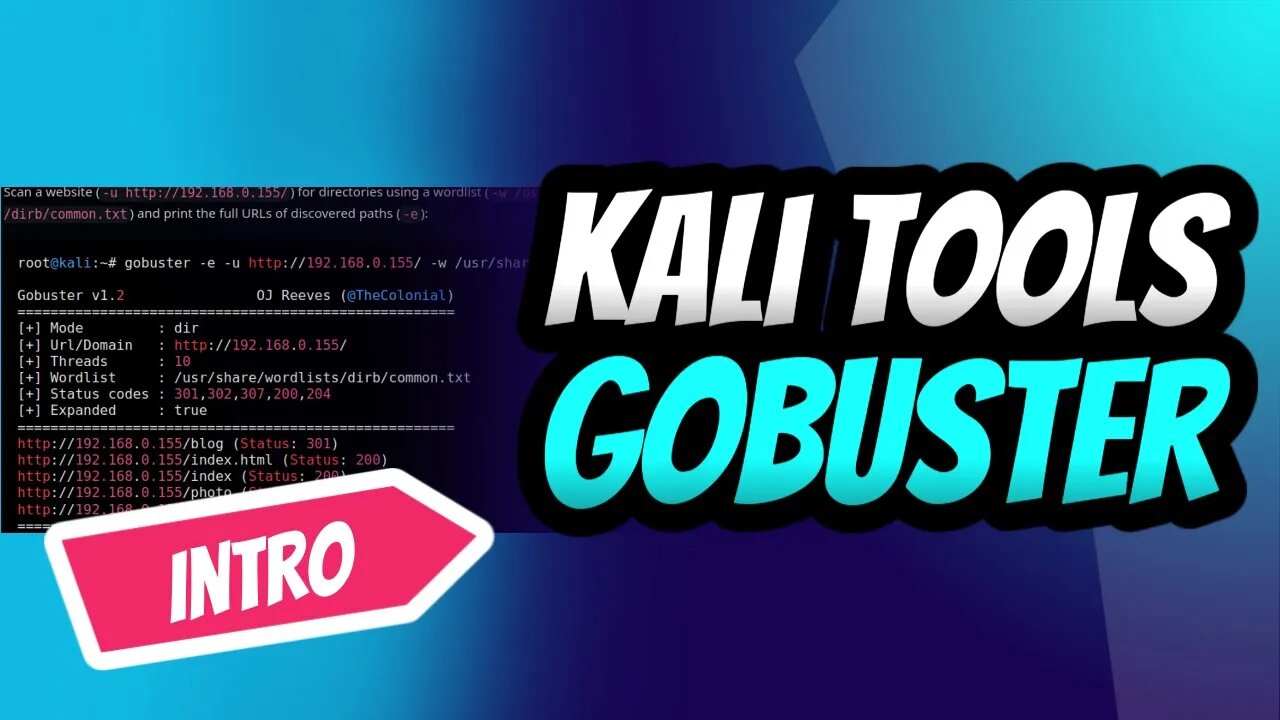
Introduction into the power of GoBuster, the ultimate directory brute-forcing tool on Kali Linux! 🚀🔥 Learn how to reveal hidden directories and files, crack passwords, and uncover vulnerabilities with ease. Follow our step-by-step guide to mastering GoBuster and supercharge your ethical hacking skills.👩💻👨💻
Don't miss out on this essential intro for every aspiring hacker and penetration tester. Subscribe now, and let's get our hands dirty with GoBuster! 💪🔓
#KaliLinux #GoBuster #EthicalHacking #PenTesting #CyberSecurity #Reconnaissance #InfoSec #HiddenDirectories #BruteForce 💻🌐🔧🔒🕵️♀️🕵️♂️
Stay tuned for an upcoming detailed tutorial that will transform you into a GoBuster pro in no time! 🌟🔧
Subscribe and hit the bell icon to make sure you don't miss this comprehensive guide, and unlock your full potential as an ethical hacker and penetration tester. Let's explore the world of GoBuster together! 🌍🔓💡
If you look at the help command, we can see that Gobuster has a few modes.
dir — Directory enumeration mode.
dns — Subdomain enumeration mode.
fuzz — Fuzzing mode.
s3 — S3 enumeration mode.
v host — V host enumeration mode.
Gobuster is a fast brute-force tool to discover hidden URLs, files, and directories within websites. This will help us to remove/secure hidden files and sensitive data.
Gobuster also helps in securing sub-domains and virtual hosts from being exposed to the internet. Overall, Gobuster is a fantastic tool to help you reduce your application’s attack surface.
You can use the following steps to prevent and stop brute-force attacks on your web application.
Audit yourself: Use Gobuster on your own applications and perform an audit. This will help you find the information that will be visible to the attackers.
Apply security policies: To prevent resources like S3 from being exposed on the internet, use AWS bucket policies to prevent unauthorized access.
Use bot protection solutions: Bot protection services like Cloudflare will stop any brute-force attacks making it incredibly difficult to attack your web application.
-
 0:47
0:47
Dev Null - | Hacking| CyberSecurity| Cybersecurity education
2 years agoThe Introverted Cyber Sleuth Decrypting Social Interactions 🕵️♀️🔒#Introvert 🕵️♀️💻 #cybersecurity
69 -
 1:09:01
1:09:01
MattMorseTV
4 hours ago $0.79 earned🔴Trump just handed Congress THE EVIDENCE.🔴
38.2K87 -
 1:01:54
1:01:54
BonginoReport
6 hours agoVanity Fair Goes Nuclear On Trump’s Inner Circle - Nightly Scroll w/ Hayley Caronia (Ep.198)
137K53 -
 53:25
53:25
Katie Miller Pod
8 hours ago $5.88 earnedFBI Director Kash Patel & Alexis Wilkins on Balancing Their Relationship with Work | KMP Ep.19
35.8K25 -
 1:15:37
1:15:37
Candace Owens
6 hours agoErika And I Sat Down. Here’s What Happened. | Candace Ep 280
202K715 -
 2:06:47
2:06:47
Quite Frankly
9 hours agoDestroying the West to Save the West? | J Gulinello | 12/16/25
47.2K11 -
 13:51
13:51
ARFCOM News
7 hours ago $0.11 earnedShould Bystander Have Blasted? + DOJ Lawyers: Don't Make Us Defend Gun Rights! + How To STOP Flock?
41.6K12 -
 1:04:59
1:04:59
TheCrucible
7 hours agoThe Extravaganza! EP: 75 (12/16/25)
97.6K14 -
 1:13:35
1:13:35
Kim Iversen
6 hours agoTurtle Island Terror: A Narrative That Serves Israel
57K122 -
 2:04:10
2:04:10
Redacted News
7 hours agoGet Ready! Something Big is Coming and They're Putting all The Pieces in Place | Redacted News
166K221