Premium Only Content
Chapter-35, LEC-5 | Getting MAC Address | #rumble #ethicalhacking #hacking #porthacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
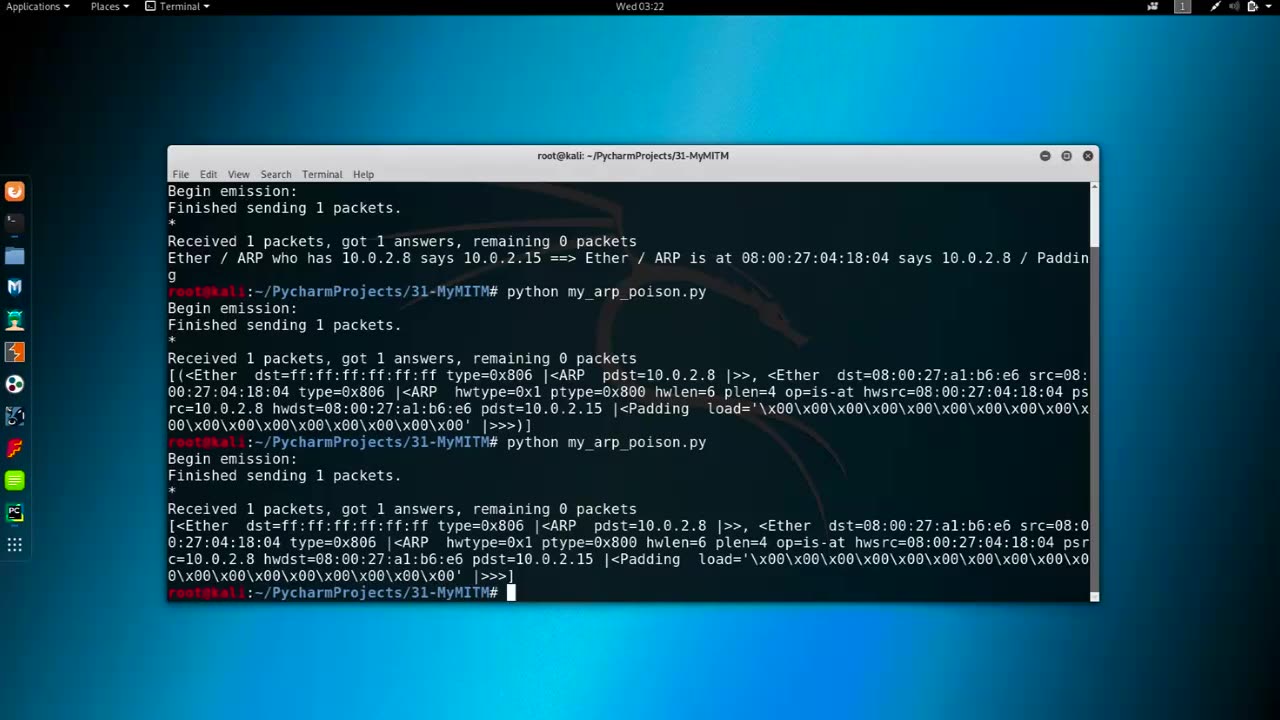
Getting MAC Address refers to the process of obtaining the Media Access Control (MAC) address of a network interface card (NIC) or a network-connected device. The MAC address, also known as the hardware address or physical address, is a unique identifier assigned to the NIC or network interface of a device at the factory, and it is used to uniquely identify a device within a network.
There are several methods to obtain the MAC address of a device:
Command-Line Interface (CLI): Many operating systems, such as Windows, macOS, Linux, and networking devices, provide command-line interfaces (CLI) that allow users to retrieve the MAC address using commands like "ipconfig" (Windows), "ifconfig" (macOS and Linux), or "show interfaces" (networking devices).
Graphical User Interface (GUI): Some operating systems, such as Windows and macOS, provide graphical user interfaces (GUI) that display the MAC address in the network settings or device properties.
Network Configuration or Management Tools: Network configuration or management tools, such as network monitoring software, network scanners, or network inventory tools, may have features to automatically detect and retrieve MAC addresses of devices within a network.
Physical Inspection: On some devices, the MAC address may be printed on a label or engraved on the NIC or device itself, making it possible to physically inspect the device to obtain its MAC address.
Network Protocol: Some network protocols, such as the Address Resolution Protocol (ARP) or the Dynamic Host Configuration Protocol (DHCP), may provide information about MAC addresses during network communication or device registration.
Obtaining MAC addresses can be useful for various networking tasks, such as troubleshooting, network monitoring, network access control, or device identification. However, it's important to note that MAC addresses can be easily spoofed or manipulated, and they should not be solely relied upon for device authentication or security purposes. Other security measures, such as encryption, authentication protocols, and access controls, should also be implemented to secure network communications and protect against unauthorized access.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 17:11
17:11
Nikko Ortiz
1 day agoIs Poverty Your Fault?
29K35 -
 1:25:15
1:25:15
The HotSeat
1 day agoIn Less Than Two Weeks, Here We Are Again.....
13.5K15 -
 12:55
12:55
The Pascal Show
12 hours ago $1.72 earned'THAT'S HIS GIRLFRIEND!' D4vd's Friends Speak Out Revealing They Thought Celeste Was His Girlfriend!
5.15K1 -
 LIVE
LIVE
Lofi Girl
2 years agoSynthwave Radio 🌌 - beats to chill/game to
248 watching -
 33:02
33:02
DeVory Darkins
7 hours ago $34.24 earnedComey INDICTED by grand jury in shocking announcement by DOJ as Trump claims MAJOR VICTORY
38.4K97 -
 2:06:23
2:06:23
Inverted World Live
9 hours agoEpstein Worked for CIA According to OMG Reporting | Ep. 114
133K41 -
 3:14:39
3:14:39
TimcastIRL
9 hours agoTrump DOJ Indicts James Comey, The ARRESTS Have BEGUN | Timcast IRL
322K392 -
 7:54:14
7:54:14
SpartakusLIVE
11 hours ago#1 Hulking MASS squashes NOOBS for viewers’ DELIGHT
72.6K2 -
 1:32:21
1:32:21
The Charlie Kirk Show
9 hours agoTHOUGHTCRIME Ep. 98 — The Comey Indictment? Antifa Agenda? Charlie and the Cubs?
126K63 -
 1:04:56
1:04:56
Sarah Westall
9 hours agoPolitical Assassinations, Targeted Hit Lists - Manufactured Chaos w/ Harley Schlanger
79.1K13