Premium Only Content
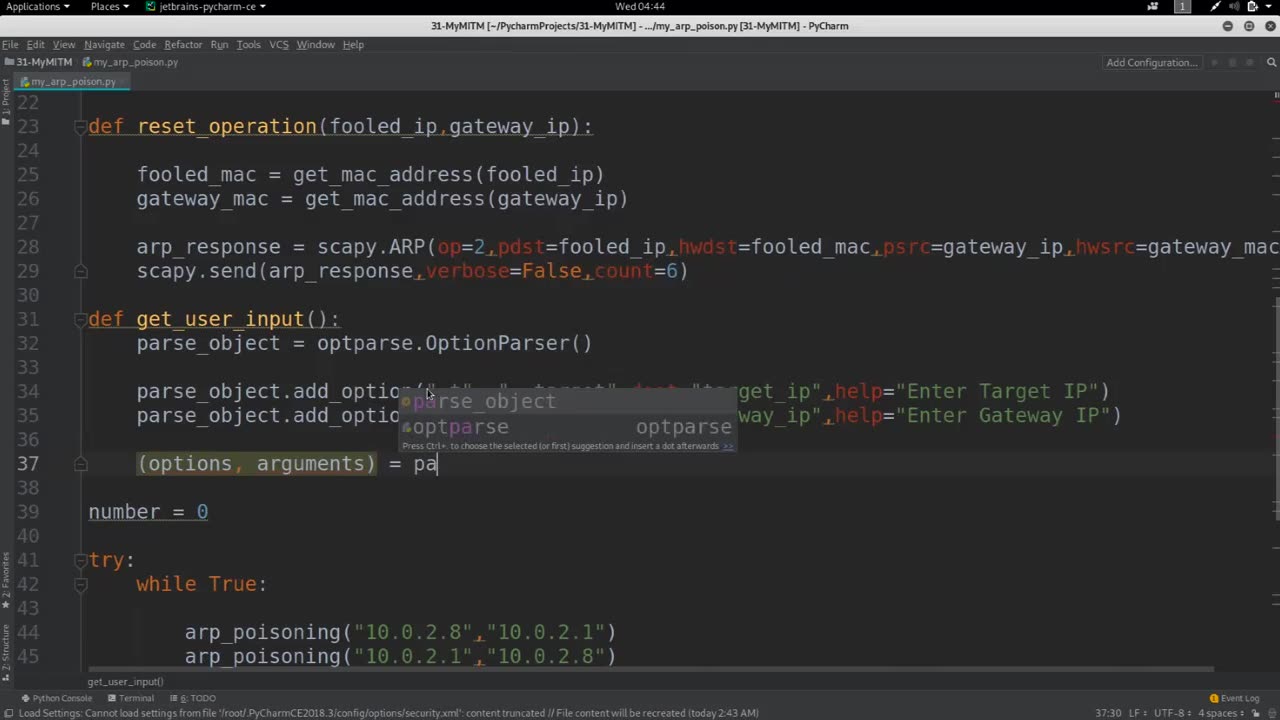
Chapter-35, LEC-9 | Getting User Input | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Getting user input is a fundamental aspect of software development that involves allowing users to provide data or information to a software application or system. User input can come in various forms, such as text, numbers, selections, checkboxes, buttons, or other interactive elements, and it serves as a way for users to interact with the software and provide input that influences the behavior or output of the application.
Getting user input typically involves the following steps:
Input collection: Providing a mechanism for users to enter or select input data. This can be done through graphical user interfaces (GUIs), command-line interfaces (CLIs), web forms, or other input methods depending on the type of application or system.
Input validation: Verifying the validity, accuracy, and integrity of the user input to ensure it conforms to expected formats, ranges, or constraints. This may involve checking for required fields, data types, length limits, and other validation rules to prevent incorrect or malicious input from causing errors or vulnerabilities.
Input processing: Processing the user input to perform the intended operation or task based on the provided input. This may involve performing calculations, making decisions, or updating the application state or database with the user-provided data.
Error handling: Handling errors that may occur during the input collection, validation, or processing stages. This may involve displaying meaningful error messages to users, logging errors for further analysis, or taking appropriate actions to recover from errors.
Feedback and response: Providing feedback to users about the outcome of their input and updating the application state or output accordingly. This may involve displaying results, updating GUI elements, or sending notifications to users to inform them of the outcome of their input.
Getting user input is a critical aspect of many software applications or systems, as it enables user interaction and customization of the software's behavior. Properly handling user input is important for ensuring the usability, reliability, and security of the software, as it involves validating and processing user-provided data in a robust and secure manner. Careful consideration should be given to input validation, error handling, and feedback mechanisms to provide a smooth and user-friendly experience for users interacting with the software.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 DVR
DVR
Russell Brand
3 hours agoRoblox ICE Raids, God and Country, and the Epstein–Israel Connection — SF680
108K25 -
 LIVE
LIVE
Decoy
21 minutes agoThey're hiding this
454 watching -
 1:11:52
1:11:52
vivafrei
2 hours agoTim Dillon Crosses a Line? Epstein Disclosure Latest! Chinese Student Making Bombs in Canada & MORE
29.7K14 -
 22:21
22:21
Stephen Gardner
1 hour ago🔥Trump STRIKES Fear! Maxwell LEVERAGES Epstein Secrets!
8.81K2 -
 LIVE
LIVE
Dr Disrespect
5 hours ago🔴LIVE - DR DISRESPECT - WARZONE - NEON HUNTER
1,446 watching -
 13:31
13:31
Clintonjaws
5 hours ago $0.31 earnedPiers Morgan CALLS OUT Andrew Wilson For Humiliating Him On Joe Rogan
5.09K5 -
 LIVE
LIVE
The HotSeat With Todd Spears
1 hour agoEP 247: Is American Pride Becoming a Thing of the PAST??
672 watching -
 LIVE
LIVE
The Tom Renz Show
1 hour agoHow Can You MAGA If You Won’t Stand For MAHA & Prosecute Child Rapists?
112 watching -
![[Ep 842] Super Bowl for Today’s Culture | Walz Resign! | Hate America? Leave!!](https://1a-1791.com/video/fwe2/d6/s8/1/G/Y/d/Y/GYdYz.0kob-small-Ep-842-Super-Bowl-for-Today.jpg) LIVE
LIVE
The Nunn Report - w/ Dan Nunn
1 hour ago[Ep 842] Super Bowl for Today’s Culture | Walz Resign! | Hate America? Leave!!
167 watching -
 1:37:00
1:37:00
The Quartering
2 hours agoSUPER BOWL MELTDOWN FROM BOTH SIDES, SUPER BOWL ADS PUSH ANTI-WHITE & DYSTOPIAN CAMERAS & MORE
126K40