Premium Only Content
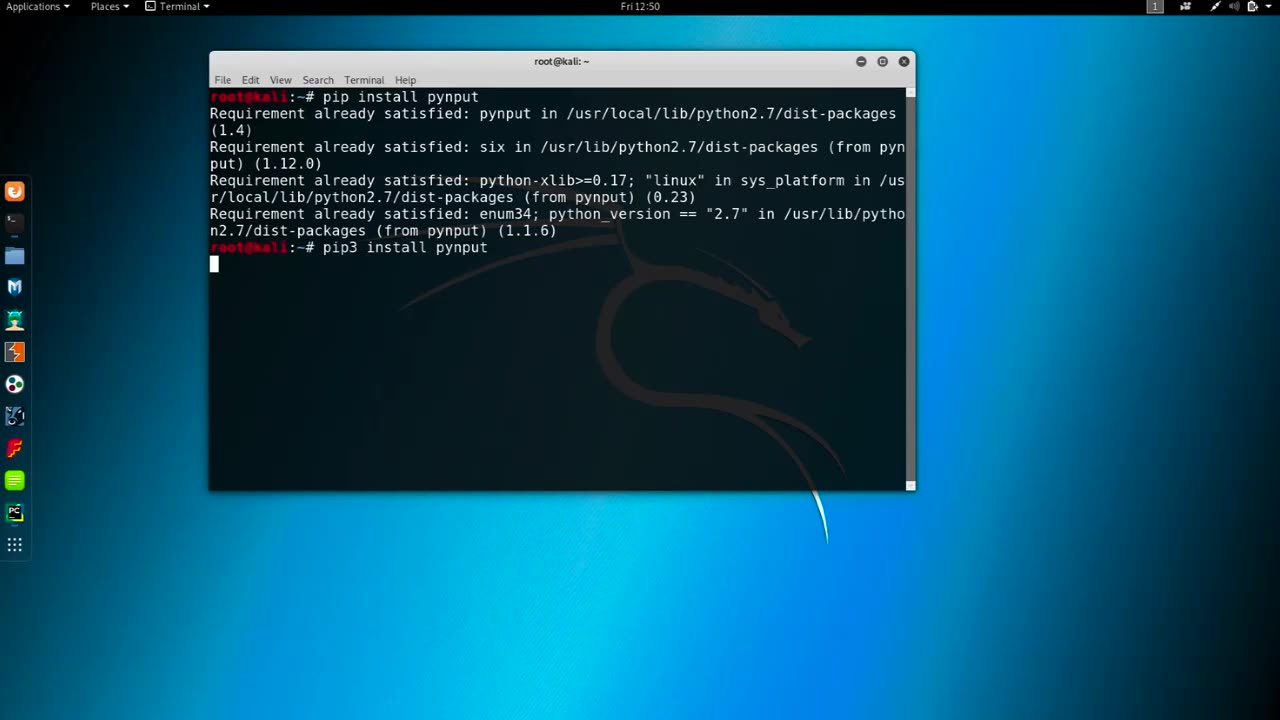
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 13:14
13:14
Upper Echelon Gamers
22 hours ago $2.09 earnedThe "Slop YouTubers" Are Angry... (And the Reason is Hilarious)
8.46K9 -
 1:06:28
1:06:28
A Cigar Hustlers Podcast Every Day
1 day agoHustler Every Week Day Episode 433 "Oscars And Chill"
13.7K -
 4:26
4:26
GreenMan Studio
1 day agoGREENMANS STOCKING STUFFERS 5 – GREENMAN AI
8.83K5 -
 5:00
5:00
SethDrums
4 days ago $8.42 earnedStaind – It's Been Awhile if it was 1980s
69.6K18 -
 20:18
20:18
itsSeanDaniel
2 days agoCandace Owens CALLED OUT by Piers Morgan, So She FIRES BACK
23.2K22 -
 4:57:14
4:57:14
Akademiks
13 hours ago21 Savage Wants Young Thug, Wham & Gunna to SQUASH IT! Future Sneak Dissing? Jim Jones Pays 50 Cent?
398K13 -
 6:01:38
6:01:38
Right Side Broadcasting Network
2 days agoLIVE: President Trump to Deliver Remarks in Rocky Mount, NC - 12/19/25
154K65 -
 3:24:48
3:24:48
VapinGamers
12 hours ago $50.36 earnedDestiny 2 - Dungeons and Loot with Friends - !rumbot !music
118K1 -
 2:07:44
2:07:44
TimcastIRL
13 hours agoTrump's Secret Plan To Make Charlie Kirk VP, America Fest IN CIVIL WAR | Timcast IRL
247K253 -
 4:09:13
4:09:13
I_Came_With_Fire_Podcast
22 hours agoLive Fire: Christmas Special
60.4K19